Who is World Wired Labs and why are they selling an Android trojan?
A company advertising a remote access tool frequently used by criminals and nation-state hackers may be serving as a front for a Chinese hacking group, according to new research published Tuesday by BlackBerry Cylance.
In a lengthy report on remote access trojans (RAT), BlackBerry Cylance researchers detail an Android malware variant, which they call PWNDROID4, that can be used to monitor targets’ phone calls, record audio, send and receive text messages, and track victims’ GPS location. Researchers believe it has been used by suspected Chinese government-linked hackers known as the Winnti group.
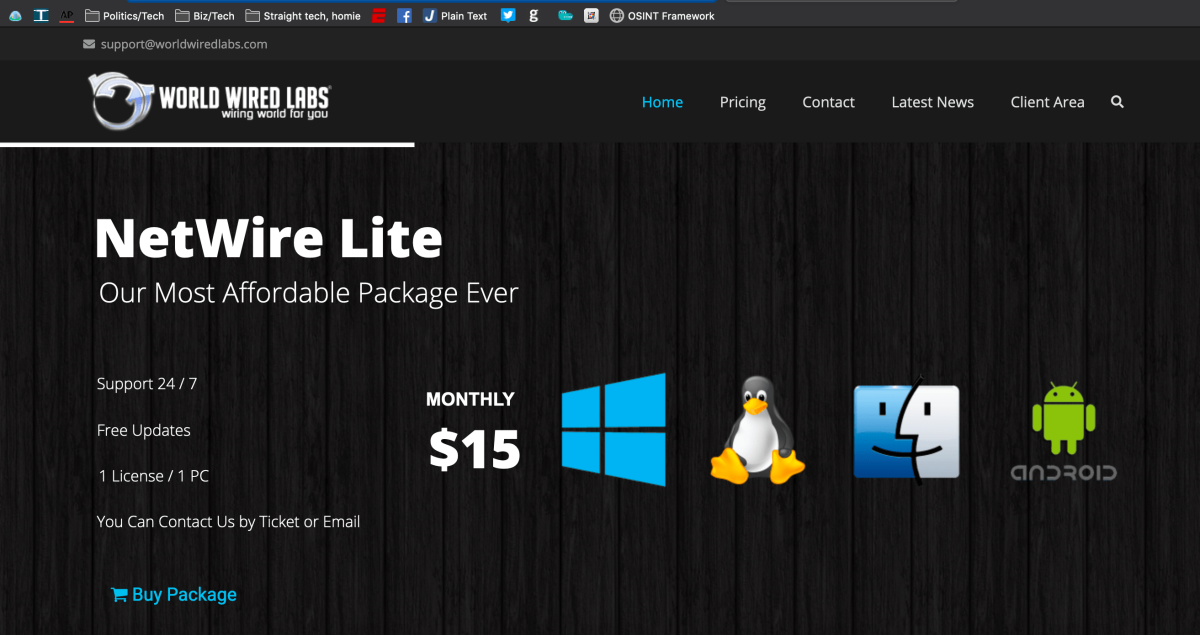
In the report, researchers have pieced together that PWNDROID4 is remarkably similar to the Android version of a RAT known as NetWire, which has been around since 2017. BlackBerry Chief Product Architect Eric Cornelius told CyberScoop that researchers traced NetWire, a multi-platform RAT that’s been in use since at least 2012, back to a firm known as World Wired Labs.
Initially, researchers first suspected that Winnti had found the tool on the internet and folded it into their own arsenal. However, that was quickly dispelled when researchers further compared a number of features and build dates between PWNDROID4 and the Android NetWire, as well as when World Wired Labs began advertising support for the tool, Cornelius told CyberScoop. PWNDROID4 is believed to have been created in 2015, before the Android version of NetWire emerged, according to the research.
“The remarkable overlap in structure and coding combined with the timeline for the development of the tools certainly raises some questions about their connection,” the report reads. “BlackBerry researchers were unable to locate any similar code samples across their archives or anywhere in public and semipublic domains.”
The researchers don’t definitively say Winnti is behind World Wired Labs or the Android NetWire tool, but based on the similarities, the two are almost certainly one and the same, according to Cornelius.
“There are striking similarities between the directory structures and naming structures,” Cornelius told CyberScoop. “The likelihood of two unrelated groups building software with that level of similarity … it’s so close to zero that it’s ridiculous.”
CyberScoop attempted to verify the existence of World Wired Labs, but searches in multiple corporate registries failed to turn up any documentation of the company. The company’s website marks its headquarters using a Google Maps snippet that points to an unlisted address near Belize City, Belize.
CyberScoop further found that World Wired Labs’s website is hosted by Solar Communications, a Zurich-based web hosting company. The company only hosts 77 other websites, the vast majority being online casinos funded by cryptocurrency, bitcoin tumblers or platforms posting illegal streams to global sporting events. Solar Communications did not return CyberScoop’s request for comment.
Cornelius said World Wired Labs could possibly be used for cover by Winnti to hide the fact that the group is responsible for the tool’s development.
“It kind of looks like a shell company,” he told CyberScoop. “[NetWire is] an accessible, almost-commoditized pen-testing tool that’s very prevalent in malware. We believe that [Winnti] sort of open-sourced, or, for profit on the black market, made this tool set available.”
Winnti is known for operations ranging from cybercrime to economic and political espionage. APT33, an Iranian threat actor group, as well as a Nigerian group known as Silver Terrier and a Pakistani group known as The White Company have been previously linked to uses of NetWire.
Linux targeting
Although the Winnti group is commonly known for its Windows-based targeting, especially in the gaming industry, the group has also been running pervasive cyber-operations targeting Linux servers for nearly a decade, according to the BlackBerry Cylance researchers.
Although the Cylance researchers did not name victims, the Linux targeting appears to have been used alongside the Windows targeting, according to Cornelius.
“These aren’t a bunch of random one-off backdoors. These are a tool suite,” Cornelius said.
The backdoors included in the Linux tool suite are capable of allowing attackers to upload and download files, manipulate files and directories, and connect to command and control servers.
The majority of the Linux samples BlackBerry Cylance researchers found had a zero detection rate in industry virus repositories, suggesting this activity has maintained access to targets for some time, largely undetected, according to BlackBerry Cylance.
Based on the malware samples the researchers analyzed, the Winnti group is also likely behind one of the largest Linux botnets ever, Linux.XorDDoS. The researchers write the Winnti Linux tool suite they analyzed “very closely resembles” malware used in the botnet, which targeted video game companies, according to earlier Akamai research.
“[E]ither there was a sharing between the Winnti group and the group behind the botnet or they were in fact one and the same,” the researchers posit.
The suspected botnet, however, is not widely believed to have been used in widespread distributed denial of service (DDoS) attacks, which Cylance researchers puzzled over. Cornelius and the research team suspect either the botnet may be designed for other activity, or Winnti is lying in wait for the right opportunity for a widespread DDoS campaign.
“A botnet is not only useful for DDoSing things,” Cornelius told CyberScoop. “This is a specifically designed DDoS botnet but no DDOS has occurred … It’s useful to have your malware self propagate within a target environment.”
Greg Otto contributed to this report.






