Winter Olympics cyberattacks meant to ‘send a message’

Security researchers say they’ve uncovered a set of hacking tools that were likely used to target and disrupt the Pyeongchang Winter Olympics over the weekend.
On Friday, the official 2018 Winter Olympics website went down for several hours causing a disruption to ticket sales and downloads during the opening ceremony. Localized Wi-Fi networks surrounding the games in South Korea also became temporarily unavailable in the preceding hours. Olympics officials confirmed on Sunday that a cyberattack had hit their systems, but provided few details about the incident.
New research published Monday by multiple cybersecurity firms now suggests that a hacking group equipped with “destructive” wiper malware, dubbed “Olympic Destroyer,” may have been behind the disturbance.
While various experts have already begun to assess the parties responsible for Olympic Destroyer — blaming nondescript hackers linked to either North Korea, China or Russia — the technical evidence to support such a conclusion is sparse. It’s notoriously difficult to accurately attribute a large-scale cyberattack to a specific group or nation-state due to techniques often employed by hackers to obfuscate their operations.
There may be a very limited, loose relation that exists between the computer code for Olympic Destroyer and another infamous wiper variant tied to Russian intelligence, named NotPetya, but that conclusion is also based on the discovery of a shared tool that is commonly available.
“We are still working to attribute the activity described in the blog, and can’t yet connect it to any known actor,” said FireEye Director of Analysis John Hultquist. “We have anticipated an attack of some nature on the events for quite a while, particularly by a Russian actor. Actors like APT28 have unceasingly harassed organizations associated with the games and the Russians have been increasingly willing to leverage destructive and disruptive attacks. In fact, such attacks against media by Russian actors have been going on for almost a decade.”
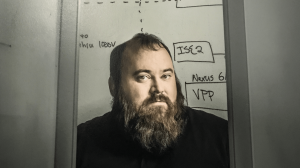
Olympic Destroyer uses the increasingly common combination of a malicious payload and credential stealer with two legitimate software tools, including Window’s PsExec and WMI (Windows Management Instrumentation), to laterally move across an already compromised network in order to covertly delete files, like shadow backups, Boot Configuration Data (BCD) and event logs on infected machines. In other words, it wipes remote data located on mapped share folders; not local files.
The malware will force connected computers to crash, become unresponsive and otherwise not function properly. For the victim, a complete recovery will likely take several days to accomplish.
“Wiping all available methods of recovery shows this attacker had no intention of leaving the machines useable. The purpose of this malware is to perform destruction of the host, leave the computer system offline, and wipe remote data,” a blog post written by Cisco’s Talos cybersecurity unit reads.
Warren Mercer, an analyst with Talos, and Hultquist both described the malware as unique. Technical forensic evidence obtained by researchers shows the attackers purposefully restrained Olympic Destroyer by underwriting it with parameters that isolate each infection; unlike the NotPetya or WannaCry incidents before it.
“The tool appears to be designed to propagate within a specific computer network and destabilize and disrupt systems by deleting recovery information and boot configurations,” Hultquist told CyberScoop. “If affected, systems will probably not be able to boot into their operating systems if system failure occurs or if rebooted. While the tool does destroy backup data and modifies the configuration of the system, as described, it does not destroy data resident on the system similar to previously observed ransomware families or destructive tools such as KillDisk or Shamoon.”
Prior to Friday, attackers had successfully harvested dozens of login credentials from privileged users of several authentic domains belong to an actual Olympics organization, according to Talos outreach director Craig Williams. This preliminary espionage would have allowed them to understand the inner workings of the Olympics’ disordered server infrastructure; such as usernames, domain names, server names and passwords.
The stolen credentials were likely leveraged to access each of the disrupted computer networks, Williams said. It remains unclear how the hackers were able to obtain these credentials but, according to Silicon Valley cybersecurity firm CrowdStrike, “several threat actors” had backdoor access to supporting Olympic organizations at the time of attack.
It’s also not clear how the hackers in this case originally deployed Olympic Destroyer; the infection vector is unknown.
It’s possible that the malware discovered by Cisco Talos is only scratching the surface.
“It could have been much worse given, you know, how far into the infrastructure they got,” Williams said. “This seems like signaling … like they were maybe sending a message.”