As Russia invades, Ukrainian government networks suffer high-profile DDoS disruption

A series of Ukrainian government websites were inaccessible Wednesday after what a government official described as a “mass DDoS attack,” marking the second apparent distributed denial-of-service disruption to hit government sites there in the last eight days.
The websites for the country’s Ministry of Foreign Affairs, Ministry of Defense, Ministry of Internal Affairs, the Security Service of Ukraine and the Cabinet of Ministers suffered network disruptions in an incident that “appears consistent with recent DDOS attacks,” according to NetBlocks, a London-based organization that tracks internet access. DDoS attacks knock sites offline by flooding them with phony traffic.
Mykhailo Fedorov, Ukraine’s Minister of Digital Transformation, said the country was experiencing another DDoS attack that also targeted Ukrainian banks, the Kyiv Independent reported shortly after observers around the world began noticing the disruptions. In a subsequent message posted to Telegram Fedorov said a “mass DDoS attack” began at about 4 p.m. local time.
The State Service of Special Communication and Information Protection said in a statement that the sites underwent “a massive DDoS attack again,” and noted that some of the sites were not working, or working intermittently, due to switching traffic to other providers “to minimize damage.” Other sites “effectively resist[ed] the attack and work normally,” the agency said in the statement.
Additionally, the webpage for PrivatBank — the largest commercial bank in Ukraine — displayed a warning message that read: “BUSTED!,” along with the message “WAF is watching you).” It’s unclear what “WAF” is referring to in this image.
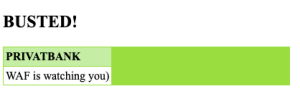
Message displayed on PrivatBank’s website mid-morning U.S. time Feb. 23, 2022.
The disruptions come as Russian President Vladimir Putin sent Russian troops into the eastern regions of Ukraine Monday after Russia formally recognized the areas as independent states. The Ukrainian government announced a 30-day state of emergency Wednesday as it called up military reservists and the legislature voted to allow citizens to carry firearms.
It’s not clear how long the Feb. 23 disruptions lasted, as some of the sites were accessible after the initial reports of disruptions.
If the network disruptions prove to be the result of DDoS attacks — relatively unsophisticated actions where attackers target victim computers with floods of traffic to overwhelm and render them temporarily inaccessible — it would be the second DDoS incident since Feb. 15. In that case, multiple government sites and several state-owned banks, including PrivatBank, and spam text messages were sent to Ukrainian citizens warning that ATMs were not going to work.
In that batch of disruptions, within 48 hours the U.S. government formally blamed the GRU, the Russian military’s intelligence arm, for disrupting the government websites (which the Russian government denied). Anne Neuberger, the White House’s deputy national security adviser for cyber and emerging technology, said the “unusual” speed at which the U.S. made the attribution was because of “a need to call out the behavior quickly as part of holding nations accountable when they conduct disruptive or destabilizing cyber activity.” U.S. and U.K. agencies also on Wednesday identified new malware associated with the GRU-linked hacking group Sandworm.
Matt Tait, a cybersecurity expert and former information security specialist for the U.K.’s Government Communications Headquarters, told CyberScoop that the spate of DDoS incidents against Ukraine “is concerning,” but “part of a consistent campaign of harassment and demoralization against the Ukrainian government and public that has been going on for some time.”
That said, DDoS attacks, while disruptive and attention-getting, represent minor activities for a government dealing with an ongoing invasion and troubled days to come.
“The conventional forces around the Ukrainian borders are a far more pressing concern,” Tait wrote in a message. “And it is their posture, not this comparatively small ddos, that gives me much more worry about a massive escalation by Russia against Ukraine in the hours and days ahead.”

This story was featured in CyberScoop Special Report: War in Ukraine






