Twitter may have given user’s private data to a ransomware hacker, who then ran a researcher offline

A man living in Russia whom the U.S. government accused of being involved in multiple REvil ransomware attacks may be involved in a phony emergency disclosure request to Twitter used to threaten a ransomware researcher in recent weeks and force them offline.
Twitter’s policies state the company will provide account information “to law enforcement in response to a valid emergency disclosure request.” The “quickest and most efficient method,” the company says, it through its legal request submissions site.
Twitter received 12,370 government information requests between January and June 2021, the latest period for which data is available, with emergency requests making up about 15%, according to data posted to the company’s site.
The disclosure request was just one part of an ongoing and escalating series of threats against researchers and at least one blogger by a cybercriminal known as “Lalartu” or “Sheriff” — or someone tying to pose as them — nicknames that security researchers in the past have tied to Aleksandr Sikerin. Federal prosecutors in Texas said in a November 2021 filing that Sikerin was most recently living in St. Petersburg, Russia, and had been an affiliate of the notorious REvil ransomware crew.
This person has in recent weeks threatened a blogger and their family, and also threatened a cybersecurity researcher with planting articles accusing the researcher of being a pedophile.
In an online chat with CyberScoop, a person claiming to be Sikerin said they’ve been threatening the researchers and the blogger because they make his work harder, and because the person said they hate Americans. The person claimed without proof that recent allegations that Sikerin is also “Lalartu” and “Sheriff” are true.
“i hate americans and i also hate researchers,” they said, referring to information security researchers who focus on ransomware activities. “i hate when they waste my time during negotiations. makes me want to throw the decryption key away you know?”
The person, offering no proof, said they worked with an “american affiliate” using a stolen government email to fake a death threat from the person associated with the Twitter account “Ido_Cohen2,” a researcher who regularly tweeted about ransomware incidents and operated the DarkFeed.io ransomware monitoring website. “twitter fell for the bait and gave up all his info.”
The person operating the Ido_Cohen2 account could not be reached for comment.
On April 30 a thread posted to a dark web forum under the username “RichTheKid” detailed what they claimed was a step-by-step on how to create and submit an emergency disclosure request to Twitter. The instructions included a section on faking an emergency. “say that the user has kidnapped a someone (sic) or they are part of a criminal group … and they extort children [to be honest I don’t care], just make sure its a good enough story to cause a response,” they wrote.
Twitter has not responded to multiple requests for comment about the account in question or the emergency disclosure request.
The apparent phony data request represents the latest troubling example of hackers and others using compromised government or law enforcement emails to compel major tech companies to turn over users’ private data.
Ransomware operators often “feel cornered, and they feel the need to strike back. And so they’re getting viscerally more aggressive at striking back.”
Allan liska, intelligence analyst with Recorded Future
Claims about the Twitter emergency disclosure request surfaced in an April 20 post on Databreaches.net, a site that covers data breaches and other cybersecurity matters. In the post, a blogger working under the pseudonym Dissent Doe reported that someone they suspected to be “a Russian threat actor” contacted them on April 12 to say that a researcher tweeting under the name “ido_cohen2” was going to get “a visit to his house.”
That supposed “Russian threat actor” then sent a screenshot of what looked like a directory containing Twitter data associated with that account. The person claiming to be Sikerin provided the same screenshot in the chat with CyberScoop April 28.
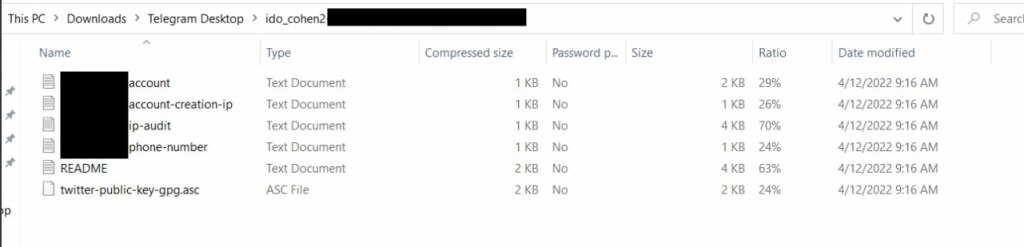
A few days later, the Twitter account for VX-Underground, an online library of malware samples, tweeted that the researcher, Ido Cohen 2, “was doxed and has left Twitter.” In recent days the Twitter account has returned, but the name has been chanced to “Offline,” and the bio simply reads “Closed.”
On April 24 Dissent Doe went into more detail on the threats against them and the others. On May 1, Dissent Doe tweeted they had interviewed “RichTheKid,” who told them that they were paid to file 20 data requests, including the one on Ido_Cohen2. “i have seen how this data can be used first hand its not pleasant,” the person told Dissent Doe.
RichTheKid told CyberScoop in an online chat Monday that Twitter did fulfill the emergency disclosure request in “less than 5 hours,” and that RichTheKid made the request after “sheriff” asked them to do so.
In since-deleted tweets, another one of the threatened researchers, who goes by the name pancak3 on Twitter, posted screenshots of an alleged chat between themselves and someone they claimed was Sikerin. In the chat, the person said it was “funny when we encrypt the hospitals,” and referenced a 2019 incident where a ransomware attack involving a hospital may have contributed to the death of newborn child. “i hope when you have a baby he dies just like this,” Sikerin said to the researcher.
U.S. prosecutors disclosed in November the August seizure of nearly 40 bitcoin — worth roughly $2.3 million at the time — from an account they said belonged to Sikerin. In the filing, prosecutors included Sikerin’s last known address and an Gmail email address.
That email address was published by the administrator of BreachForums — an online forum where people post information about stolen data, hacks that took the place of the recently seized RaidForums — after the account holder, “Sheriff,” was accused of spamming, Dissent Doe wrote April 24.
Allan Liska, an intelligence analyst at cybersecurity firm Recorded Future who closely monitors the ransomware ecosystem, said he was familiar with Lalartu from the various dark web forums. Lalartu was more “over the top” than most typical ransomware operators, he said, but overall the situation is becoming more dangerous.
“There is a lot of concern in the community that some of these ransomware actors, him in particular, have gotten very aggressive toward researchers,” Liska said. As researchers and private cybersecurity threat intelligence firms have gotten better at identifying and unmasking aspects of ransomware activity, ransomware operators can often “feel cornered, and they feel the need to strike back. And so they’re getting viscerally more aggressive at striking back.”
The increased aggression may show some level of desperation, Liska added, given the increased law enforcement activity all over the world working to shut down ransomware operations. Nevertheless, ransomware activity continues and researchers are going to have to take more precautions about the type of information they share online.
Twitter, he added, needs to take a hard look at its data sharing policies. While the emergency data request issue affects the entire industry, Twitter in particular needs to step up.
“That’s the medium that so many security researchers use, that’s the medium we use to share information, that’s the medium that we use to communicate with each other, more so than any other,” he said. “Unfortunately Twitter does have a level of responsibility here that they need to figure out.”
Last week Bloomberg reported that bogus data requests, which have been sent to Twitter and other major firms such as Apple, Meta, Alphabet, and Discord, have been used to harass and sexually extort minors. On March 29, Krebs on Security explored the practice of criminals obtaining data through data requests, with one hacker claiming some companies return data in as little as 30 minutes.



