In studying tech supply chain, feds cite open source products, device firmware
Open-source software and device firmware are two of the biggest areas of vulnerability in the supply chains for information and communications technology, according to a federal report Thursday that called for better risk management practices and improved monitoring efforts by government and industry.
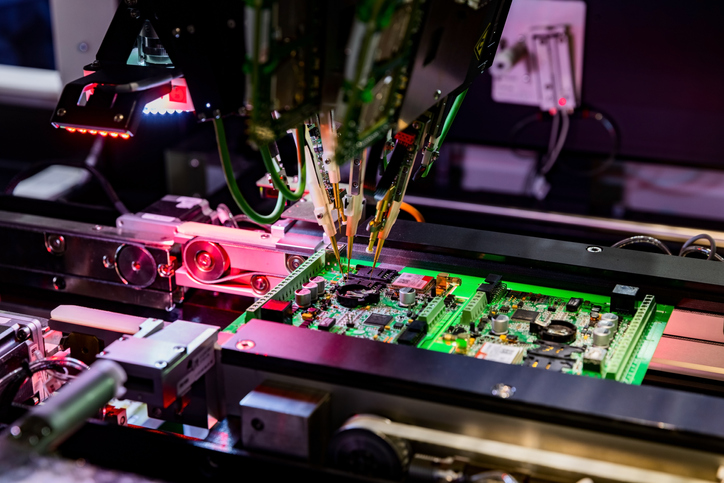
Another area that potentially affects U.S. cybersecurity is a shrinking manufacturing base for hardware, including a “significant reduction” in the related workforce, the report said. The Biden administration asked the departments of Commerce and Homeland Security for the review under an executive order signed in February 2021 as the White House worked to address challenges in the supply chains for goods and services overall.
At the time, the breach of SolarWinds’ software supply chain by Russia-linked hackers had riled Washington, and Thursday’s report comes as the government and cybersecurity industry are still responding to the Log4shell bug found in December 2021 in a widely used piece of open-source logging software for websites. Log4Shell is cited at length as an example of where things can go wrong for open-source software (OSS).
“Given the already vast and growing use of OSS, the urgency and importance of ensuring that OSS is secure and can be trusted cannot be overstated,” the report said. The authors cite specific ways malicious hackers can introduce malware into open-source projects, such as poisoning public software libraries or forcing users to download tainted versions from URLs that look authentic but are slightly misspelled — a practice known as typosquatting.
Also discussed at-length are dangers to firmware, the low-level operating commands for a device often installed during manufacturing. Bogus firmware updates for a firewall device were recently cited in a warning from the U.S. and U.K. governments about a Russian botnet.
“[T]he complexity of the ICT supply chain has led many Original Equipment Manufacturers (OEMs) to outsource firmware development to third party suppliers, which introduces risks related to the lack of transparency into suppliers’ programming and cybersecurity standards,” the report said.
The weak spots include poor control over the authenticity of firmware and irregularity in the way many manufacturers update it, the report said. Both factors make firmware vulnerabilities particularly attractive to ransomware attackers, the authors said, citing the NotPetya and Thanos ransomware incidents.
The recommendations include expanding efforts to bolster the domestic tech workforce and improving the U.S. government’s visibility into its own supply chain — the kind of move that often can drive industry to revise its own practices. The report also calls for a new Critical Supply Chain Resilience Program at the Department of Commerce.
In speaking broadly about the findings of the report, Secretary of Commerce Gina Raimondo and Secretary of Homeland Security Alejandro Mayorkas said “the U.S. government alone cannot address these ICT supply chain vulnerabilities.”
“We look forward to working with industry stakeholders, foreign governments, and other domestic and international partners to implement measures identified in the assessment that build resilience and security throughout the ICT supply chain and across our nation,” the secretaries said in a joint statement.





