Russian hackers heavily targeted news outlet in days after U.S. election, researchers say

Hackers working for the Russian government sent a barrage of targeted phishing emails between 2014 and 2016 to employees of major news outlets, and they focused particularly on Al Jazeera in the days following the U.S. presidential election, according to new research by cybersecurity firm Trend Micro.
It’s unclear exactly why the elite team of hackers — known as APT-28, Fancy Bear or Pawn Storm — focused so heavily on the Qatar-based, state-funded global broadcaster during that short window. Like other news agencies targeted over the longer two-year span, including the New York Times and Buzzfeed, the award-winning outlet covered the election in detail and dedicated a section of its website to election-night coverage.
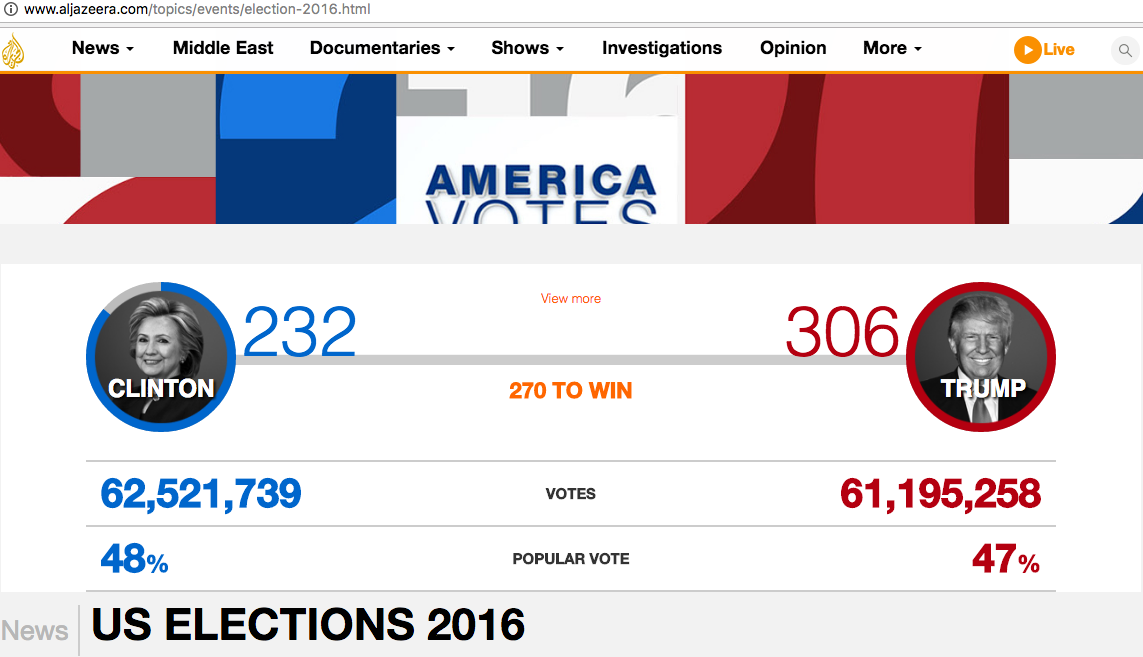
Al Jazeera coverage of 2016 U.S. election
Trend Micro’s Forward-looking Threat Research, or FTR, team said staff at Al Jazeera were repeatedly sent phishing emails with deceptive links, including “account-aljazeera.net” and “sset-aljazeera.net.” The subject line for some emails sent by the hacking group include “News: Yemen air strikes kill 23 in factory: residents” and “News: Tragedy in Nepal.”
“Pawn Storm often uses the exact same headlines [in phishing attacks] from recent news reports seen on media sites like CNN, Al Jazeera, Huffington Post, Military Times and many others,” the report reads.
Al Jazeera representatives did not respond to CyberScoop inquiry concerning the findings of TrendMicro’s research report. The outlet had shut down its U.S.-based news team several months prior to the targeting dates listed by Trend Micro.
“Attacking corporate email makes a lot of sense for threat actors as email is one of the weakest points in the targets’ defense. In the last four years, Pawn Storm [also known as APT-28 or Fancy Bear] has launched numerous credential phishing attacks against the corporate email system of many organizations,” the research report notes. “Breaching corporate email accounts may lead threat actors to valuable, confidential data and it can be a stepping stone for penetrating deeper into the target organization.”
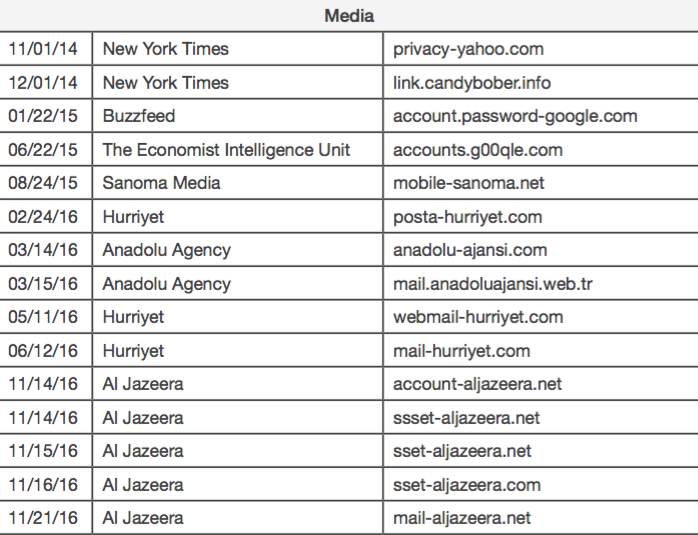
date of sent phishing email / organization / phishing domain used — image via Trend Micro report
“The research team didn’t have any additional information or speculation on why no other media outlets were confirmed targets,” said Trend Micro Vice President of Cloud Research Mark Nunnikhoven. “It’s an area that needs follow-up but we don’t have verified data on that question at this time … we could certainly have missed certain campaigns. We also did not include all campaigns we know about for various reasons.”
APT-28, a codename developed by the private sector to categorize the nebulous hacking group, is perhaps best known for breaching the Democratic National Committee in the run-up to last year’s election. The Office of the Director of National Intelligence published a declassified report in January stating that Russia was behind the hack and that it weaponized leaked documents by sharing stolen material with media outlets and via social media.
In the past, APT-28 has indirectly worked with media organizations to disseminate stolen material. Experts say the group has done so largely through proxies, a collage of faux identities, anonymized websites and other platforms. There are known cases where the group has compromised systems, accessed confidential records and waited for months until the most opportune moment to leak documents to discredit a victim. A leak of internal Al Jazeera communications has yet to occur.
It’s not clear if APT-28 compromised any computers used by Al Jazzera staff — the research alone only suggests an attempt to do so.
Other organizations that were apparently targeted by APT-28, cited by Trend Micro, include Emmanuel Macron’s French presidential campaign and the office of the prime minister of Turkey. A spokesman for French government cybersecurity agency ANSSI confirmed the existence of attacks on the Macron campaign to Reuters but did not attribute the phishing emails to Russian hackers, specifically.