Intel bill puts DNI in charge of countering Russian election meddling
The nation’s top intelligence official will have to assess spy agencies’ response to Russian election meddling last year and devise a whole-of-government strategy for combatting similar efforts in the future, if a Senate bill that advanced this week becomes law.
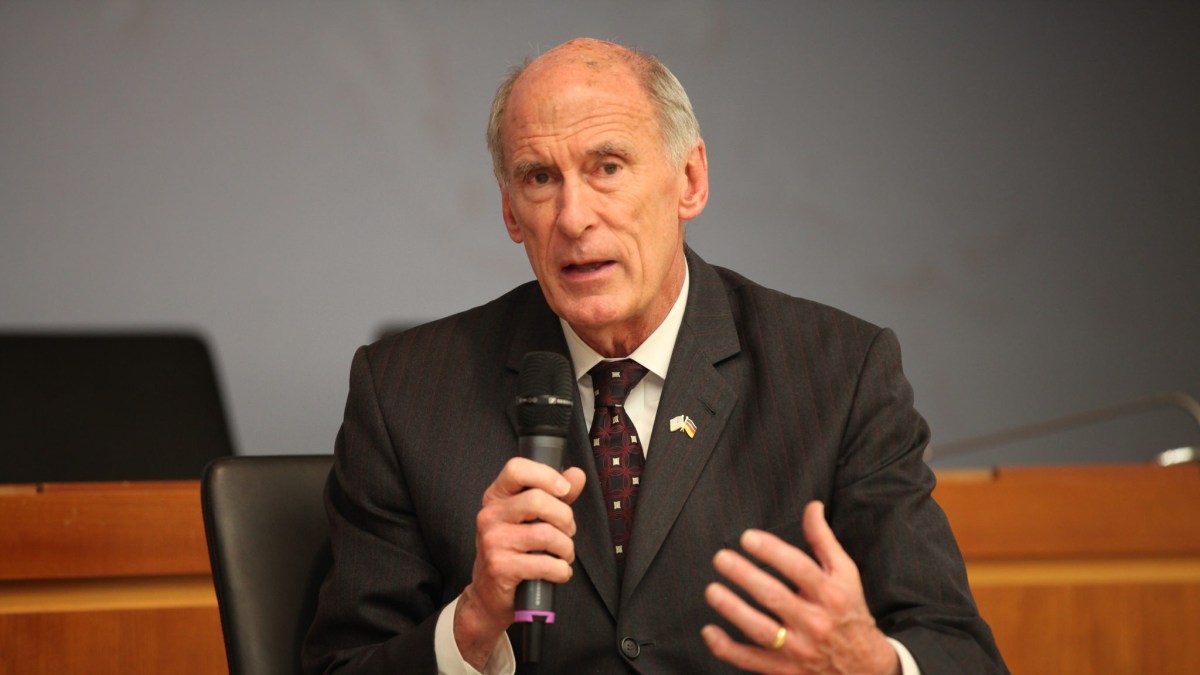
The bill, S.1761, the Intelligence Authorization Act for Fiscal Year 2018, passed out of committee this week with a single vote dissenting. If it becomes law in its current form, it would require a number of reports to Congress on a variety of cybersecurity issues in addition to election hacking from Director of National Intelligence Dan Coates.
Sen. Ron Wyden, D-Ore, said in a statement he voted against the bill, “over a provision that could set a troubling constitutional precedent” — by identifying Wikileaks and its senior leaders as “a non-state hostile intelligence service often abetted by state actors.”
“My concern,” he said, “is that the use of the novel phrase ‘non-state hostile intelligence service’ may have legal, constitutional, and policy implications, particularly should it be applied to journalists.” He added that “The introduction of vague, undefined new categories of enemies” would be “ill-considered.”
The bill now heads to the Senate floor, where lawmakers can debate its election-meddling provisions, including:
- A detailed, unclassified report to Congress within 60 days from the Undersecretary of Homeland Security for intelligence and analysis on all cyberattacks and attempted cyberattacks by foreign governments on U.S. election infrastructure in 2016 and “such cyberattacks or attempted cyberattacks as the undersecretary anticipates against such infrastructure” in the future. The report “shall identify the states and localities affected and shall include cyberattacks and attempted cyberattacks against voter registration databases, voting machines, voting-related computer networks, and the networks of secretaries of state and other election officials.”
- A classified after-action report to Congress within a year, from the Director of National Intelligence, assessing how well U.S. intelligence agencies discovered and analyzed Russian interference in last year’s election; including how well information was shared, whether open source intelligence was used effectively and what additional authorities the nation’s spies might need in the future.
- An assessment of the “security vulnerabilities of state election systems … and … foreign intelligence threats to the election,” to be submitted to intelligence committees and congressional leadership not less than six months before any regularly scheduled election, by “the Director of National Intelligence, in coordination with the Director of the CIA, the Director of the NSA, the Director of the FBI, the Secretary of Homeland Security, and the heads of other relevant elements of the intelligence community.”
- A “whole-of-government strategy for countering the threat of Russian cyber attacks and attempted cyber attacks against electoral systems and processes in the United States,” to be produced by the Director of National Intelligence, this time in coordination with “the Secretary of Homeland Security, the Director of the FBI, the Director of the CIA, the Secretary of State, the Secretary of Defense, and the Secretary of Treasury.” To be developed and briefed to Congress within 90 days, the strategy “shall include … Public education and communication efforts.”
This last provision may prove controversial, as some observers say they’re concerned that the Director of National Intelligence has the leading role in an effort that ultimately touches on the very heart of American democracy.
“It’s a new assignment for the DNI that straddles the boundary between foreign intelligence and domestic security,” Steven Aftergood, who monitors intelligence policy for the Federation of American Scientists’ Project on Government Secrecy, told CyberScoop.
The bill language calls out cyber attacks on election systems — seemingly excluding the “fake news” Russian influence operations that used bot armies of Twitter and Facebook accounts to amplify useful media narratives. But Aftergood noted that the inclusion of public education and communication meant the strategy “might extend to [countering] information operations.”
“It’s implicit rather than explicit,” he said, adding that the intent of the authors would likely become clearer when the committee report language was published.
In addition, the bill has an entire section on protecting the energy grid, and several other cyber provisions, including reports on the operation of the Vulnerability Equities Process and authorities to award special higher pay rates to cyber experts in the intelligence agencies.