Mandiant: Belarusian disinformation operation pushes phony organ harvesting tale

A hacking group associated with the government of Belarus and aligned with Russian interests “leveraged compromised assets” to push a false story about an alleged Polish criminal ring harvesting organs from Ukrainian refugees to illegally traffic in the European Union, researchers with the cybersecurity firm Mandiant said Thursday.
The previously unattributed activity was the work of Ghostwriter, which Mandiant formally linked to the Belarusian government in November 2021.
The revelations were just part of a rundown of a portion of the multiple ongoing information operations related to Russia’s assault on Ukraine playing out for select audiences around the world using inauthentic social media accounts, fnews organizations, personas and hacktivists that may or may not be state-aligned.
“The recent phase of Russian aggression toward Ukraine, manifested by Russia’s full-scale invasion, has flooded the information environment with disinformation promoted by a full spectrum of actors,” the researchers wrote in an analysis published Thursday morning. “Concerted information operations have proliferated, ranging from cyber-enabled information operations, including those that coincided with disruptive and destructive cyber threat activity, to campaigns leveraging coordinated and inauthentic networks of accounts to promote fabricated content and desired narratives across various social media platforms, websites, and forums.”
Targets of the operations include Ukrainian citizens and those in other European countries, domestic audiences in China and Iran, but also the domestic Russian populace — “underscoring Russia’s need to sell the war to its own people,” the Mandiant researchers wrote.
Groups known to be Russian-government aligned, as well as those associated with Russian ally Belarus and pro-Russian “hacktivist” personas, are generally pursuing information operations serving at least one of three functions, according to the researchers: demoralizing Ukrainians and fomenting internal unrest, dividing Ukraine from its allies or bolstering perceptions of Russia.
“While these operations have presented an outsized threat to Ukraine, they have also threatened the U.S. and other Western countries. We anticipate that such operations … will continue as the conflict progresses.”
Mandiant
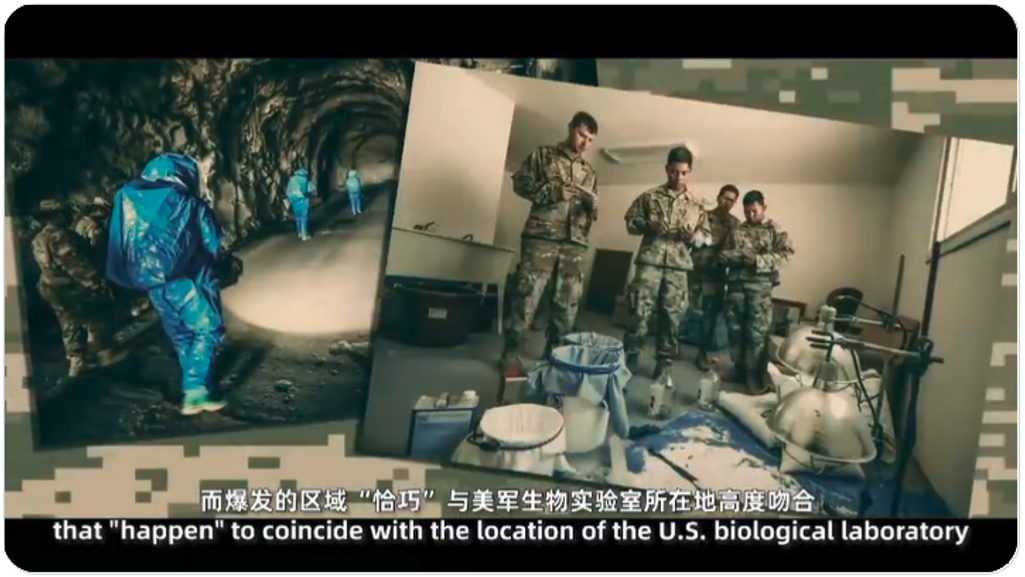
A pro-Chinese campaign known as DRAGONBRIDGE, which has previously been seen using thousands of inauthentic social media accounts across multiple platforms to drive certain narratives, has “shifted its messaging” in response to the war in Ukraine, according to the Mandiant researchers. The campaign’s content has echoed and amplified the Russian narrative associated with Pentagon-linked biological weapons labs in Ukraine, representing “a form of political opportunism in [China’s] continued attempts to target the U.S. and the West’s global standing.” The United Nations has rebutted the bioweapon story.
DRAGONBRIDGE has amplified narratives that the U.S. is “self-serving in its actions and that it is an unreliable partner in its alliances,” the researchers wrote.
The report also examined ongoing activity from Iranian operation previously seen using inauthentic news sites and clusters of social media accounts to push anti-U.S., Saudi and Israeli themes. The researchers included information on a previously unnamed Iranian campaign they dubbed “Roaming Mayfly” due to its potential links to the “Endless Mayfly” information operation reported by human rights investigators at Citizen Lab in 2019.
Iranian efforts include messaging targeting Arabic-speaking audiences that claim the U.S. had fled from Afghanistan and had now abandoned Ukraine, that NATO had sacrificed Ukraine to avoid war with Russia, and amplified charges of racism given disparate Western treatment of Ukrainian refugees versus those coming from the Middle East.
Roaming Mayfly also targeted Russian audiences on the eve of the war in an apparent attempt to drive a wedge between Russia and Israel by tweeting from a now-suspended account impersonating a Russian foreign policy thinker.
“Information operations observed in the context of Russia’s invasion of Ukraine have exhibited both tactical aims responding to, or seeking to shape, events on the ground and strategic objectives attempting to influence the shifting geopolitical landscape,” the researchers wrote. “While these operations have presented an outsized threat to Ukraine, they have also threatened the U.S. and other Western countries … [and] we anticipate that such operations, including those involving cyber threat activity and potentially other disruptive and destructive attacks, will continue as the conflict progresses.”






