The quantum computing threat is real. Now we need to act.
Cybersecurity is a top national security concern facing America. At this very moment, adversaries are carrying out “store now, decrypt later,” or SNDL, attacks against the U.S., wherein they are exfiltrating and storing sensitive encrypted data critical to national security, critical infrastructure, corporate enterprises and more. The intention is to steal this sensitive data to decrypt it when quantum computers can decrypt this information.
At that time, the public-key encryption algorithms that have protected our stored data, communications, financial transactions, networks, government secrets, intellectual property and other assets for nearly 50 years, will become obsolete, and the sensitive information that they protected will be revealed. Any encrypted data that has already been stolen can no longer be protected. The danger is immediate.
It’s imperative that U.S government agencies and private sector corporations immediately begin migrating vulnerable cybersecurity protocols to post-quantum cryptography (PQC). PQC could safeguard this sensitive government and critical industry data from these cybersecurity attacks.
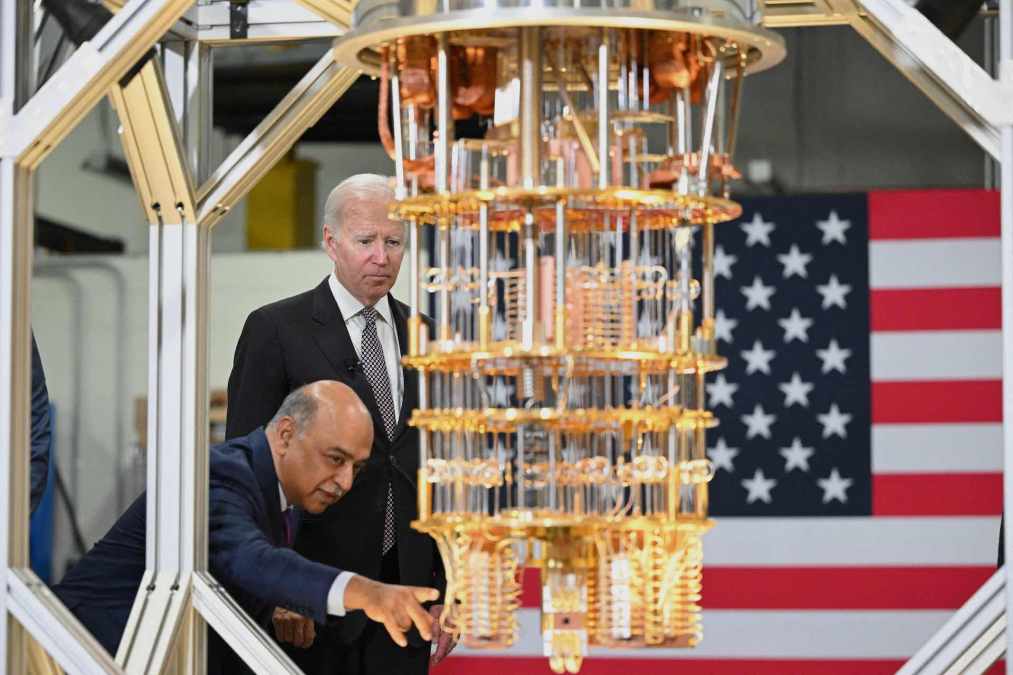
The government has taken positive steps against this national security threat. Recently, President Biden issued an executive order, along with two national security memorandums (NSM-8 and NSM-10) directing the U.S. to accelerate its quantum computing initiatives, including quantum-resistant cybersecurity. To this end, on July 12, the House of Representatives passed the Quantum Computing Cybersecurity Preparedness Act (H.R.7535) and this bill now awaits Senate review. Industry is standing by to support the U.S. government upon Senate approval and U.S. Government implementation.
While it is a much-needed step in the right direction, the proposed legislation does not adequately factor the present threat posed by SNDL attacks on vital government, military and infrastructure systems that rely on current public key cryptography. Much of the encrypted data will continue to be sensitive for decades. Once this data is exfiltrated, there is nothing that can be done to prevent it from eventually being exploited by adversaries. PQC protocols can protect against SNDL attacks, but the migration process to PQC will be lengthy — we must begin now.
NIST has released the first four of their planned PQC algorithms, and major global banks, telecoms, healthcare providers and other enterprises are already beginning the transition to PQC. Given the complexity of federal IT networks, the PQC vulnerability assessment process alone will take several months to complete.
The Office of Management and Budget, which assists the president in meeting policy, budget, management and regulatory requirements, could make funding available now to allow the federal government to start assessing current cryptographic uses and developing migration strategies, while waiting for legislation to be approved. And agencies and organizations need to take the necessary first, foundational steps of this transition — specifically inventory their networks to understand what they have and do a risk-based assessment of what are their protection priorities — to ensure that they are ready when standards are established and funding is available.
As former defense and intelligence officers, we can attest to what is at stake as the world enters the quantum era. Current SNDL attacks represent an existential threat to our government, military, and commercial enterprises, and likewise the prosperity, privacy and safety of our citizens.
Washington should strive with vigor to become the dominant power in quantum information sciences. That includes immediately beginning the process of PQC enterprise migration. We cannot afford to fall behind.
***
Former Principal Deputy Director of National Intelligence Susan M. Gordon is a former senior intelligence official and a renowned expert on strategy, innovation, and leadership. Gordon advises on technology, space, cyber, and global security. Gordon was the second highest ranking officer in the U.S. intelligence Community as the Principal Deputy Director of National Intelligence from 2017 to 2019. She serves on several advisory boards including CACI International, E3/ Sentinel, Pallas Advisors, Primer.AI, and the Draper Richards Kaplan Foundation. Gordon also serves as an advisor to SandboxAQ.
Admiral John Richardson served 37 years in the U.S. Navy, completing his service as the Chief of Naval Operations (CNO), the top officer in the Navy. Since retirement, he has joined the boards of several major corporations and works in leader development. While in the Navy, Richardson served in the submarine force. He commanded the attack submarine USS HONOLULU in Pearl Harbor, Hawaii, for which he was awarded the Vice Admiral James Bond Stockdale Inspirational Leadership Award. Richardson also serves as an advisor to SandboxAQ.
Mike Rogers retired from the U.S. Navy in 2018 after nearly 37 years of naval service rising to the rank of four-star admiral. He culminated his career with a four-year tour as Commander, U.S. Cyber Command and Director, National Security Agency. In those roles he worked with the leadership of the U.S. government, the DoD and the U.S. Intelligence community as well as their international counterparts in the conduct of cyber and intelligence activity across the globe. Admiral Rogers is currently supporting companies in the private sector, serving as a member of various boards or acting as a senior advisor. Rogers also serves as an advisor to SandboxAQ.

