‘Patient zero’ of global ransomware incident was warned and owned before outbreak
A Ukrainian software company at the center of an international ransomware outbreak was reportedly warned about its insufficient digital security multiple times, and new evidence shows it had been compromised by hackers before last week’s incident.
M.E.Doc, a Ukrainian software firm that develops accounting software that is mandated by the country’s government, is widely considered to be the “patient zero” behind ExPetr, a unique ransomware variant that first appeared on June 27 with the capability of spreading quickly across local networks and deleting data.
Cybersecurity researchers with Slovakian security firm ESET published evidence Tuesday that hackers were able to successfully penetrate M.E.Doc in the months preceding the major attack and had installed a series of backdoors. These implants would allow a hacker to remotely execute numerous commands and upload other malicious code. Such a backdoor may have been originally leveraged to launch ExPetr. It’s also possible that the attacker had access to M.E.Doc’s source code, according to ESET.
The findings are significant because they underscore how a vulnerability in the supply chain of a single major software vendor could be used to conduct a global cyberattack.
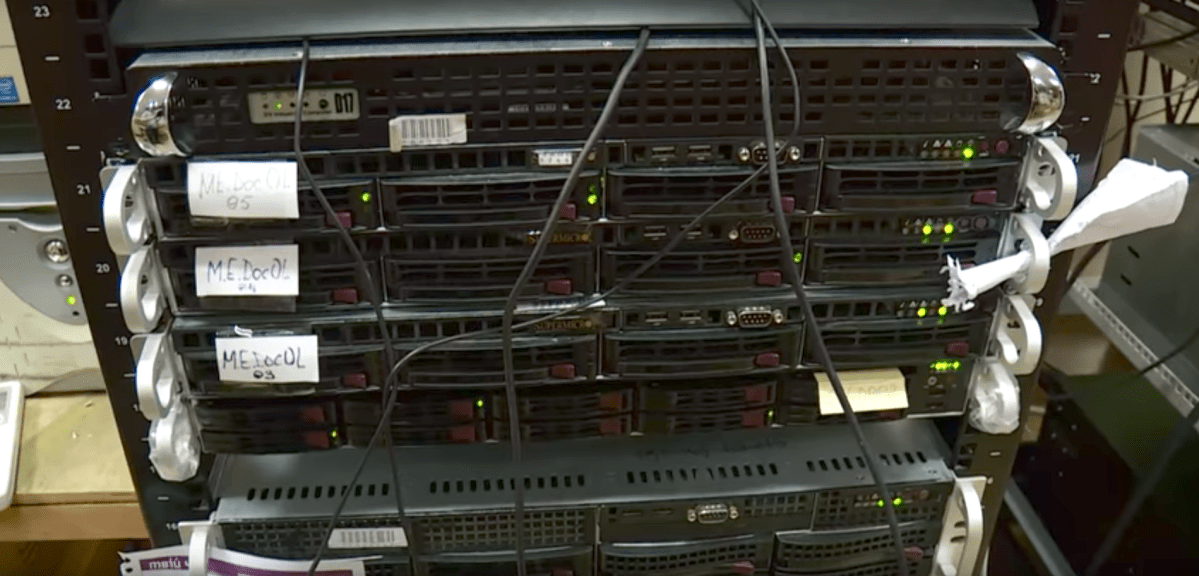
Ukrainian federal police seized several computer servers used by M.E.Doc as recently as Tuesday because of the risk of a new round of malware being distributed by the company’s hijacked IT infrastructure, according to a statement by the Cyberpolice Department of Ukraine’s National Police.

Photo by CyberPolice.gov.ua
A video posted Wednesday by the National Police shows armed men storming a M.E.Doc facility.
A majority of companies in Ukraine rely on M.E.Doc to organize their finances. By hacking into M.E.Doc’s systems and planting malicious computer code inside typically benign software updates, the attackers were able to covertly infect a large number of clients.
After first denying culpability, M.E.Doc admitted Wednesday that its software was partially at fault for the spread of ExPetr. Ukrainian officials are reportedly considering charges against the company, which unknowingly sent out booby-trapped software updates loaded with ExPetr to clients.
Some security researchers say that the tactics, tools and processes used by the hackers behind ExPetr similar to those employed by a Russian hacking group known as Telebot or Sandworm. NATO-sponsored researchers also say ExPetr is the work of a nation-state, but did not provide further attribution details.
Despite those leads, the source of ExPetr remains an open question. Kaspersky Lab researchers only attribute the cyberattack to the Sandworm group with “low confidence.” What is generally agreed upon, however, is that the ExPetr was inherently designed to be destructive in nature rather than operate for financial gain.
Organizations that were not customers of M.E.Doc were affected by ExPetr through, among other things, an interconnection of computer networks tied to Ukrainian partners and associates.
Over the last week, ExPetr has effectively disrupted business operations in more than a dozen companies and is responsible for millions of dollars in damages. Victims of the computer virus already include American pharmaceutical giant Merck and shipping company Maersk.




