Leaked NSA hacking tools are a hit on the dark web

Underground hackers are now sharing, promoting and working to adopt executable computer code evident in NSA documents that were published last week by the Shadow Brokers, private sector intelligence analysts tell CyberScoop.
Tutorials on how to utilize some of the tools began appearing the same day the NSA documents were originally published, according to researchers at Israel-based dark web intelligence firm SenseCy. Forum members have shown a particular interest in a leaked framework similar to Metasploit that’s unique to the NSA called Fuzzbunch.
SenseCy, a firm focused on the dark web staffed by former intelligence officials, identified a series of conversations occurring in a hidden Russian cybercrime forum discussing how members could exploit a bug in Windows Server Message Block, a network file sharing protocol.
“Hackers [have] shared the leaked [NSA] information on various platforms, including explanations [for how to use the tools] published by Russian-language blogs,” said SenseCy Director Gilles Perez. “We identified [one] discussion dealing with the SMB exploit [ETERNALBLUE], where hackers expressed interest in its exploitation and share instruction on how to do so.”
Perez declined to name the dark web forums surveilled by SenseCy, but provided CyberScoop with screenshots of conversations between members discussing the matter in discussion boards — “We can never provide the names of the forums as that could jeopardize our operations,” he wrote in an email.
One of the powerful tools shared by the Shadow Brokers last week, and addressed by a March Microsoft security update, is codenamed ETERNALBLUE in the leaked documents — it is also referred to as vulnerability MS17-010 by Microsoft.
ETERNALBLUE allows for an attacker to remotely cause older versions of Windows to execute code.
Security researcher Matthew Hickey was able to show in a video that ETERNALBLUE is effective against machines running Windows Server 2008 R2 SP1, an old but popular version of Windows Server.
SenseCy researchers told CyberScoop they’ve already seen cybercriminals attempt to utilize the MS17-010 vulnerability in ransomeware-style attacks.
“We are now seeing a trend, that most likely will gain momentum in the following weeks, of infecting Windows servers with Ransomware utilizing the [NSA] leaked exploits,” Gilles said.
Some security researchers believe that exploiting MS17-010 will become popular amongst cybercrime gangs because it allows for a more damaging ransomware infection.
https://twitter.com/GossiTheDog/status/854824179778162688
Researchers at cyber intelligence firm Recorded Future told CyberScoop that they too have spotted separate discussions in several Russian and Chinese hacker forums in which users successfully reversed engineered some of the Windows tools and were openly sharing their findings.
“The surprising recent release — one of the most comprehensive and up to date — of hacking tools and exploits by the notorious Shadow Brokers group stirred up great interest among Russian-speaking cyber criminals,” said Andrei Barysevich, Recorded Future’s director of advanced collection. “Only three days after the data was leaked, we identified a discussion among members of an elite dark web community sharing expertise in weaponizing the EternalBlue exploit as well as the DoublePulsar kernel payload.”
He added, “considering that Microsoft patched the EternalBlue vulnerability as recently as March 14, the number of potentially affected systems could still be tremendous.”
Recorded Future similarly declined to name the forums where they discovered this content.
“[In the Chinese forum], they were particularly interested in the exploit framework (named FUZZBUNCH), the SMB malware (ETERNALBLUE) and privilege escalation tool (ETERNALROMANCE),” members of Recorded Future’s research team wrote in an email. “Actors were focused on the unique trigger point for [ETERNALBLUE] and some claimed that the patches for CVE-2017-0143 through -0148 were insufficient because they did not address the base code weaknesses.”
These discussions indicate that there’s broad interest in the unique malware triggers published by the Shadow Brokers and a belief that the underlying vulnerabilities being exploited had not been completely mitigated by Microsoft’s patches, according to Recorded Future. “These two factors combine to increase the risk that malicious Chinese actors may reuse or repurpose this malware in the future,” a spokesperson explained.
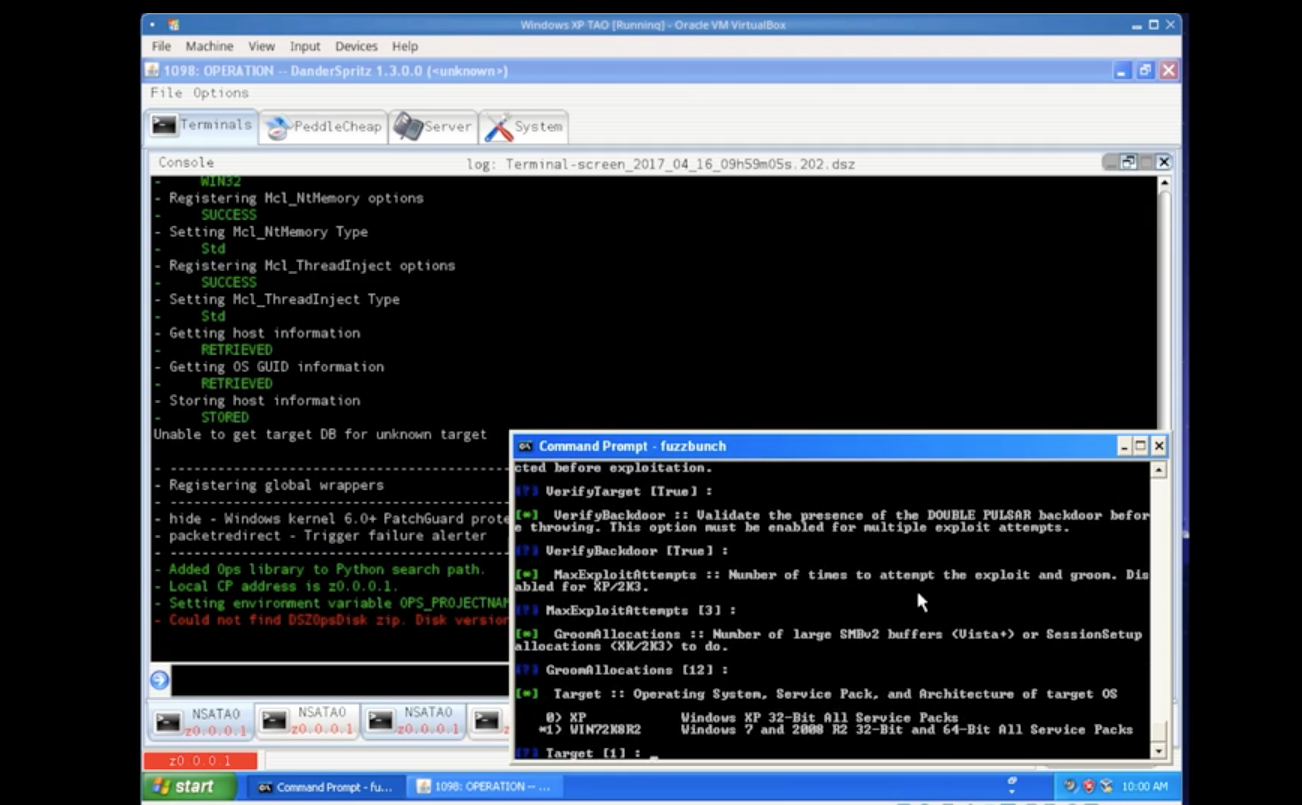
Hickey was able to demonstrate how FUZZBUNCH can deploy malware
Most of the exploits and implants mentioned in the latest release are designed to exploit software vulnerabilities apparent in older Microsoft products, including Office and various operating systems. The technology giant stated in a blog post over the weekend that it had patched most of the exploits. Discontinued, end of life version of Windows, such as XP and 2003, remain vulnerable as they did not receive a security patch.
More than 65 percent of desktop computers connected to the internet last month ran on older versions of Windows like Vista, according to estimates from the tracking firm Net Market Share.
While many of the Microsoft Windows-specific exploits contain remote code execution vulnerabilities, they need to be deployed against a host in order to be successful. In other words, a connection to the organization must already be established for many of these exploits to work — as port 445, which is used in Microsoft’s SMB, is typically blocked internet-wide.
Microsoft declined to answer questions pertaining to how the company originally became aware of the aforementioned vulnerabilities, which were supposedly once exploited by the NSA.
Though it remains unclear whether anyone has been able to successfully leverage any of the leaked hacking tools to launch their own computer intrusion, security researchers fully expect and are preparing for a barrage of new attacks supported by NSA’s quality engineering.
“Even though the vulnerabilities released were patched, we feel confident that it will only be a matter of time before we see exploitation in the wild,” said Cylance Chief Research Officer Jon Miller. “The scale will be on par with any other known and patched vulnerability. Only those that aren’t judicious in patching their systems will be affected, mitigating the risk that comes from a true zero-day.”
Liam O’Murchu, the director of Symantec’s security technology and response group, said he expects it will take a “little longer” for attackers to begin incorporating the leaked tools into their own attacks.
“From a defensive perspective, one of the main problems is the volume of data released,” said O’Murchu. “We need to analyze all the files to understand how they could be changed or used to fit in with current cybercrime attacks … with ~7000 files disclosed, it is very resource intensive to understand all of the tools, the full capabilities and how they can be used. That is what we are working on now.”
A cohort of independent researchers and security firms are finding new capabilities and targeted software vulnerabilities hidden in the massive trove of documents on a near daily basis since Friday’s release.
“We have only begun to scratch the surface on these tools and now that they are out there it’s important we can analyze them to determine servers that are impacted as well as what steps can be taken to protect against them,” Hickey wrote in a blog post, Wednesday.
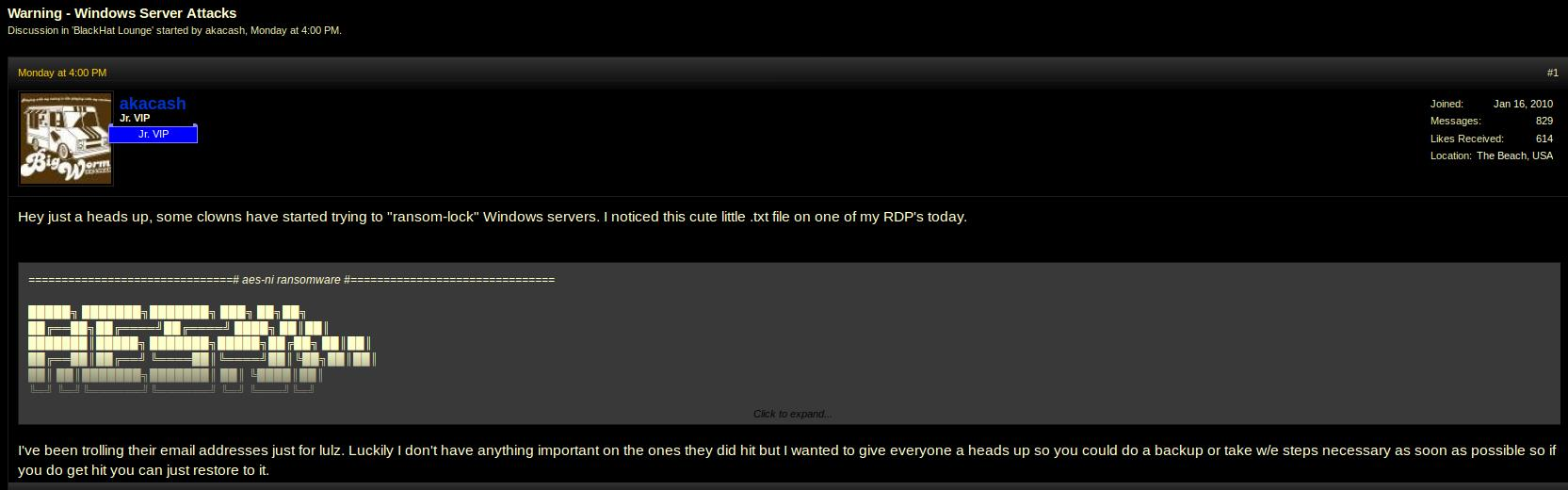
image of a conversation occurring on a hidden forum, where users report – provided by SenseCy
“The tools are released in binary format and as reverse engineering efforts are underway. We will likely discover more interesting features about the attacks,” wrote Hickey. “We are under no illusion that such a huge data trove will not be completely analyzed in its first few days of discovery and neither should you.”