Another European nation hit by hackers, Montenegro grapples with ongoing ransomware attack

Multiple Montenegrin government websites remained inaccessible Friday, a week after government officials there said the country’s “critical state infrastructure” had been targeted with an “unprecedented” cyberattacks.
Officials initially blamed the attacks, which came in two waves over the course of the past week or so, on a “coordinated” digital assault from Russian cyber offensive services.
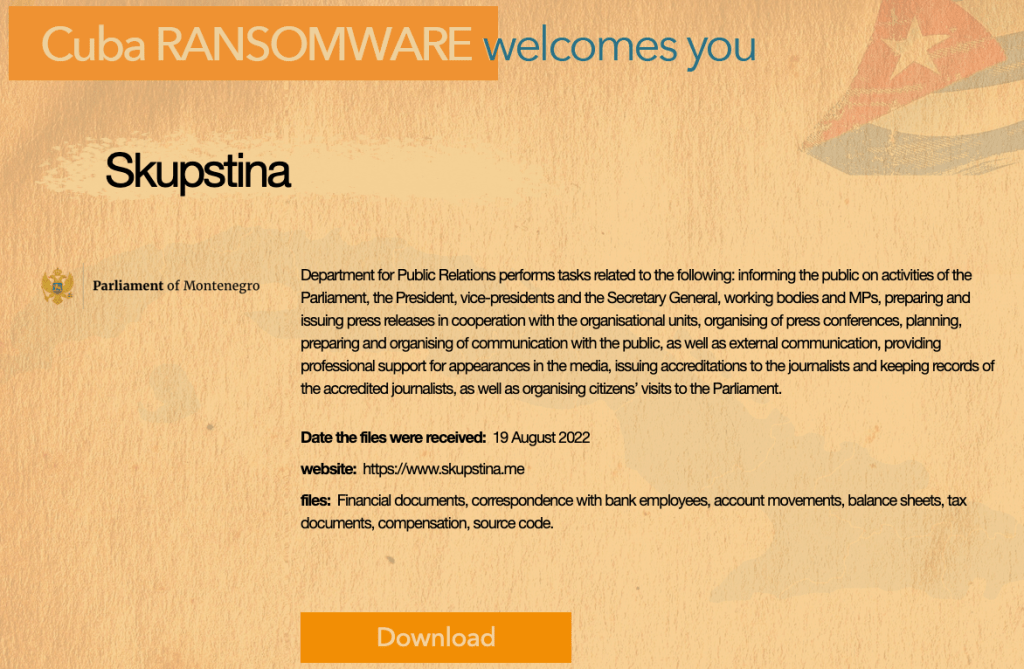
But on Tuesday, the shadowy Cuba Ransomware group, which some researchers believe has Russian members, claimed to have attacked the Parliament of Montenegro, causing more uncertainty about who is behind the crippling series of attacks and what they want to achieve.
Now, the Cuba development points to a case of criminal ransomware and Montenegrin leaders have backed away from blaming Russia. Officials confirmed that Cuba Ransomware was behind the attack and demanded a $10 million ransom.
But whoever is responsible for the ongoing digital assault on the country that has been a NATO member nation since 2017, it’s causing significant disruption.
Public Administration Minister Maras Dukaj told reporters that 150 workstations across 10 state institutions had been “infected,” although it’s unclear what infected means, with reports suggesting that the state-owned power utility switched to manual operations to prevent any possible damage.
BBC Cyber Reporter Joe Tidy reported that along with the ransomware, the government was “under waves of DDoS attacks too.”
The attacks on the country spurred help from NATO and other western governments. A NATO spokesperson told CyberScoop this week that the alliance’s “experts are in touch with the Montenegrin authorities,” and that “NATO Allies are providing support.” The French Agency for Information Systems Security sent a team to help Aug. 27, and the FBI confirmed to CyberScoop Thursday that it was “aware of the situation and is providing assistance at the request of the Montenegro government.”
The attacks are just the latest in a string of incidents affecting governments across the region and into Europe, where multiple governments have been hit with various cyberattacks in recent months. Pro-Russian hackers have attacked Lithuania, Germany, Italy, Romania, Norway and the U.S., Wired reported in July, mostly as a result of those countries being perceived enemies of the Russian government and its brutal war on Ukraine.
More recently, in early August, hackers aligned with Iranian government interests attacked multiple government services in Albania, Montenegro’s neighbor to the south. The group behind that attack, “HomeLand Justice,” remains active and as recently as Monday uploaded a series of zip files it says contain various Albanian databases with names and phone numbers to its Telegram channel.
Little is known about the people behind Cuba Ransomware group. In April 2021, incident responders with Israeli security companies Security Joes and Profero reported having talked with Cuba Ransomware attackers “who over the course of the investigation, we discovered are Russian speakers, due to a simple translation mistake on their part.” The responders were unable to approximate the attackers’ location, they said.
Omri Segev Moyal, Profero’s co-founder and CEO, told CyberScoop Thursday that “from our experience, we’ve never seen indicators which might suggest Cuba Ransomware is state sponsored.”
A December 2021 FBI alert said the group had compromised at least 49 entities in five critical infrastructure sectors including the financial, government, healthcare, manufacturing and information technology sectors as of November 2021. The group had demanded at least $74 million in ransoms and received at least $43.9 in payments, the FBI said.
A February 2022 Mandiant analysis examined aspects of the group’s activity and its malware, which it tracks under the label UNC2596. That group is the only one to use a ransomware variant known as “COLDRAW,” according to the Mandiant researchers, “which may suggest it’s exclusively used by the group.” The group employs a “multi-faceted extortion model where data is stolen and leaked on the group’s shaming website, in addition to encryption using COLDRAW ransomware,” the researchers wrote, targeting “dozens of organizations across more than ten countries, including those within critical infrastructure.”
Tyler McLellan, senior principal threat analyst with Mandiant and the co-author of the February 2022 analysis, told CyberScoop in a statement Thursday that Mandiant has not “previously observed UNC2596 conduct, or threaten to conduct, any DDOS activity in previous cases where we also saw Cuba (COLDRAW) ransomware deployed. That said, threat groups do change tactics all the time and this could be a new approach by the group, but we ultimately don’t have enough data to make an assessment with high confidence.”
Brett Callow, a threat analyst with cybersecurity firm Emsisoft who tracks ransomware closely, told CyberScoop he’s unsure what to make of Cuba Ransomware’s attack on Montenegro.
“It does seem that we’re seeing more attacks on governments outside the U.S. — Costa Rica, Peru and Argentina, for example,” he said. “Whether that’s coincidence or an intention shift is impossible to say.”
An affiliate using the Russian-based Conti ransomware platform attacked Costa Rica and Peru in late April, demanding $10 million and then $20 million. The State Department on May 6 announced a $10 million reward for information on Conti leadership, citing the Costa Rica incident. The agency announced a subsequent $10 million reward for specific Conti members Aug. 11, reflecting the increasing attention and resources devoted toward battling ransomware.
“The US has stepped up its counter-ransomware efforts in recent months, so it’s possible the gangs are experimenting to see where else they may be able to make money without risking attracting the attention of [Cyber Command],” Callow said.
Then again, perhaps the response to the attack on Montenegro will induce ransomware crews to think twice, said Ciaran Martin, a professor at the University of Oxford and the founding chief executive of the United Kingdom’s National Cyber Security Centre.
“I would hope that, in time, ransomware groups are deterred from attacking nation states by the fact that a), they won’t pay, and b), it will bring upon them greater attention than they will want,” he said. The Cuba Ransomware group is one of the smaller groups, he said, and had not attracted the widespread attention along the lines of the bigger groups, at least outside of specialist circles.
But an attack like this, which has generated headlines and pledges of support from the around the world, changes the game. “If you’re running the Cuba group, as far as I know the Montenegrins haven’t paid,” Martin said, “and now you’ve got the FBI after you. That doesn’t sound like the wisest decision they’ve ever made.”






