As the military’s cyber units change guard, a battle over control rages on
During a time of rapid change for the U.S. military’s top cyberwarfare teams, the current version of the 2019 defense bill is challenging the president’s ability to exert his authority with regards to those units.
The White House is protesting a series of measures in the newly Senate-approved 2019 National Defense Authorization Act that seek to legislate how and when President Donald Trump can direct generals to launch cyberattacks. That effort comes while the U.S. Air Force, Navy, Army and Marines welcome new leaders to take charge of their respective cyber forces.
Hanging in the balance is how the U.S. operates in cyberspace, which most developed countries now define the fifth domain of warfare, adding to land, air, sea and space.
Amendments introduced in the NDAA would require the executive branch to develop and adhere to a cyberwarfare strategy document that draws lines around what types of malicious foreign activity should result in retaliatory measures, such as attacking an enemy’s server with destructive computer code.
The bill also could limit the military from striking back in cyberspace unless it has a certain level of confidence in its attribution for the source of an attack. Broadly speaking, the NDAA would further define the nation’s ability to wage cyberwar. Members of the National Security Council see the legislation to take a slice out of the president’s authority to independently launch military operations, a current U.S. official told CyberScoop. The official spoke on condition of anonymity to describe internal government deliberations.
There’s also an ongoing discussion in Congress about replacing the Authorization for Use of Military Force (AUMF) that was initially passed following the Sept. 11 attacks. That authorization, among other things, grants the president the unilateral ability to order some military missions without a declaration of war by Congress.
Existing rules, stipulated by Presidential Policy Directive 20, dictate that the president alone must directly authorize any prospective cyber-operations intended to damage another country’s assets. That authorization comes through a chain of command that extends from the Pentagon to the White House.
CyberScoop previously reported that members of the National Security Council have been pushing to rescind PPD-20 and place some power in the hands of generals to conduct operations themselves.
Over the last several months, while lawmakers have debated language in the NDAA, there’s been a change of command in four different military branches. If the political gamesmanship in play becomes a reality, the heads of these units will be the ones responsible for deciding when and where attacks are launched.
Parts of these different units comprise a larger battalion, known as the Cyber Mission Force (CMF), which is run by the Fort Meade-based U.S. Cyber Command. Elevated to a unified combatant command on par with Strategic Command earlier this year, U.S. Cyber Command is led by the dual hat head of NSA, Gen. Paul Nakasone.
On July 2, Maj. Gen. Matthew Glavy will assume command of Marine Corps Forces Cyberspace Command. He previously served as the deputy director of operations at U.S. Cyber Command.
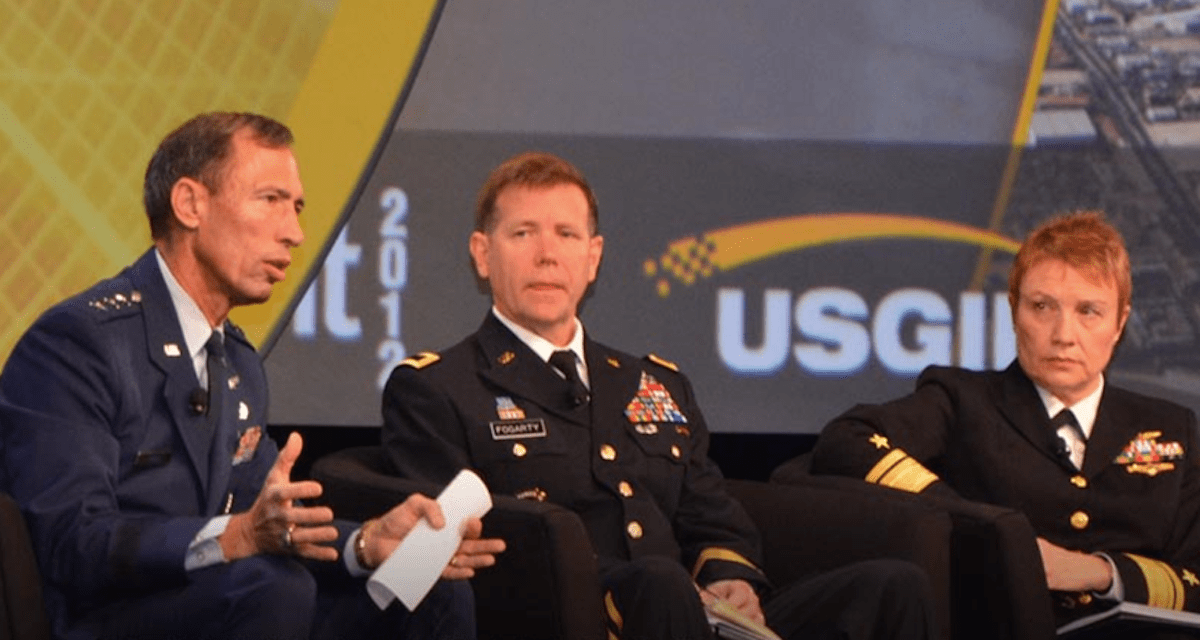
Lt. Gen. Stephen Fogarty recently took over at Army Cyber Command, which Nakasone had previously led. Fogarty previously served as the chief of staff at U.S. Cyber Command.
Adm. Timothy White, a longtime U.S. Cyber Command official who helped build and then led the CMF as its commander, became the commander for the Navy’s 10th Fleet Cyber Command on June 18. His predecessor, Vice Adm. Michael Gilday, left to become director of operations for the Joint Chiefs.
White’s replacement at U.S. Cyber Command is Air Force Brig. Gen. Timothy Haugh, a highly decorated military intelligence professional.
Lastly, Maj. Gen. Robert Skinner will soon take the top spot at the 24th Air Force, the service’s cyber division.






