Two Methbot suspects set to plead guilty as alleged ringleader maintains his innocence

Two men accused of participating in the multimillion-dollar Methbot digital-advertising fraud scheme are scheduled to plead guilty in the coming days, according to court filings from the Eastern District of New York.
Sergey Ovysannikov and Yevgeniy Timchenko, both originally from Kazakhstan, are scheduled to appear in a federal courtroom in Brooklyn on Sept. 24 and Sept. 25, respectively, to enter plea agreements before Judge Steven M. Gold. Both men initially pleaded not guilty after they were extradited to the U.S. earlier this year.
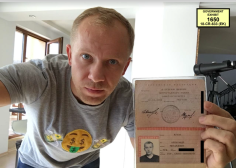
A third man, Methbot’s alleged ringleader, Aleksandr Zhukov, has promised to fight the charges against him. Prosecutors say the operation relied on cybercriminal techniques to defraud companies out of roughly $29 million.
Few details of the plea agreements were immediately available. Arkady Bukh, defense counsel for Ovysannikov, declined to say to which counts his client intends to plead guilty. Attorneys for Timchenko did not respond Friday to phone calls seeking comment.
“They prohibited lawyers from actually discussing the specific details,” Bukh said. “I think I think it was a mistake that they filed it.”
The U.S. Department of Justice linked both men to the Methbot ad fraud operation, also known as 3ve, which relied on a botnet-based scheme to artificially inflate web traffic to fraudulent websites. By selling the ad space to real marketing firms, and making website visitors appear to be real humans, scammers conned international companies out of tens of millions of dollars.
Advertising fraud is a pervasive criminal technique that allows thieves to redirect dollars meant for marketing into their own accounts, and it indirectly hurts smaller, legitimate publications that struggle to keep afloat in the digital age.
U.S. authorities still are investigating the Methbot/3ve operation, CyberScoop reported in August, nine months after the FBI said it took some of the key players into custody.
Ovysannikov was a key player in the operation. He and his team used hidden browsers on 1.7 million hacked computers to load falsified ads. The group not only accessed breached computers without their owners’ knowledge, they also took money from companies which believed their ads were being widely viewed, according to the indictment.
He was arrested in October in Malaysia.
Timchenko worked as a kind of technical operator for the scheme, prosecutors said. The Methbot indictment unsealed in November alleged that Timchenko chose servers in places like Missouri, California and New Jersey to obfuscate the illicit activity.
“Timchenko deliberately chose certain U.S. service providers because they had the ‘coolest processors’ and a ‘larger’ cache (for temporary data storage) than competing providers,” the indictment said.
Meanwhile, Aleksandr Zhukov remains poised for trial. In a note to to the court sent in April from his jail cell in the Metropolitan Detention Center in Brooklyn, Zhukov said in broken English “my cyber crime in my indictment is just imagination of FBI and I wish to go to jury.”
The location of the five other Methbot suspects named in the indictment was not immediately clear.