As Methbot trial gets underway, prosecutors say a former scammer will testify against alleged ringleader

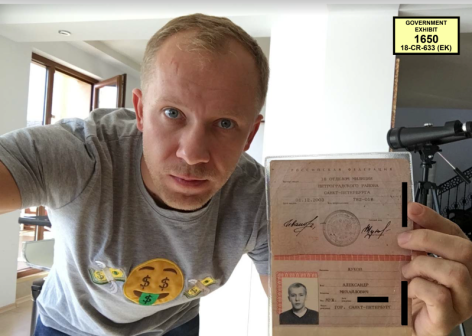
Nearly three years after he was arrested in a Bulgarian apartment, Aleksander Zhukov was seated in a Brooklyn courtroom this week to face charges of running a complex fraud scheme that netted millions of dollars.
Zhukov, a Russian national, allegedly functioned as the ringleader of a scheme to use traditional cybercrime techniques to carry out a larger advertising fraud conspiracy, known as Methbot, that the U.S. Department of Justice says netted some $7 million between 2014 and 2016. The trial, scheduled to take place in the coming weeks in a Brooklen federal courtroom, is slated to include testimony from a range of FBI agents, cybersecurity executives and, as the prosecution said on Wednesday, a cooperating witness who worked with Zhukov to carry out the work.
The ruse involved Zhukov’s use of a fake advertising company, which he used to charge marketing firms to run ads, prosecutors said during their opening statement in the Eastern District of New York on Wednesday. The company, dubbed Media Methane, made “a program that would fool the advertisers into believing that real people had seen their ads, and [Zhukov] and his associates then ran that program on thousands of computers that he rented.” The process allowed the crew to steal the advertisers’ investment.
Zhukov’s arrest in October 2018 in Bulgaria was the first domino to fall in an operation that FBI officials later described as “a beautiful concert of things shutting down.” At roughly the same time, U.S. law enforcement, working on information provided by cybersecurity firms, apprehended suspects in Malaysia and Estonia.
The Methbot scheme also laid the groundwork for another cybercrime effort, popularly known as the 3ve effort. In that case, scammers used similar techniques to defraud marketing firms out of $29 million. Nine suspects have been indicted in all, two of whom have pleaded guilty.
Zhukov has maintained his innocence since he was taken into custody. In 2019, he asked for a new attorney, describing himself as “a weaponless soldier in front of a tank with name FBI.” Last year, Zhukov’s legal representation asked to have his charges dismissed amid concern about the spread of coronavirus in the detention facility where he has been incarcerated.
Prosecutors also told the jury this week that one of Zhukov’s former associates would testify against him, detailing how “he helped the defendant adjust hits bots, fine tune them to act like human internet users, and then get money from advertisers every time those bots looked like ads.” Whether the cooperating witness is Sergey Ovysannikov and Yevgeniy Timchenko, two Kazakh men who have pleaded guilty, or another individual, remains unclear.
In an opening statement for the defense, attorney Zachary Margulis-Ohnuma argued that Zhukov never claimed to have access to human-generated traffic in the first place. It was a common tactic for digital advertisers and publishers around 2015 to trade in fraudulent traffic, he said.
“There are reams and reams of the stuff that they grabbed from his apartment that day [when he was arrested] in Varna, Bulgaria; and nowhere does it say to someone, ‘Oh, I’ve got some human beings that want to sell you the ads,'” the attorney said. “What he was selling was machine-generated traffic.”
It’s an argument that rests in part on the notion that fraud was and remains an inherent facet of the internet advertising ecosystem. The issue is set to cost advertisers some $44 billion annually by 2022, by some estimates.
“So bear with me, fasten your seat belts, sit back and get comfortable,” said Margulis-Ohnuma. “We are going to be here for a few minutes.”
Correction, May 12, 2021: A previous version of this story incorrectly reported that police arrested Aleksandr Zhukov in Belgium. Zhukov was taken into custody in Bulgaria.