Meet ‘Meltdown’ and ‘Spectre,’ the chip flaws causing problems for nearly everyone
Critical bugs in all modern processor chips that allow attackers to potentially steal sensitive data were publicly revealed Wednesday after months of private security industry work and days of public speculation.
Named “Meltdown” and “Spectre,” the vulnerabilities could allow attackers to find passwords or sensitive documents stored in memory.
The exploits work on personal computers, mobile devices and cloud infrastructure that relies on hardware dating back to 1995.
For most people, the solution is to install security updates for their operating system quickly and regularly.
It’s not clear if the exploits have been used in the wild, because neither leave any traces in log files.
One of the researchers to independently discover these flaws was Google Project Zero’s Jann Horn, who “demonstrated that malicious actors could take advantage of speculative execution to read system memory that should have been inaccessible,” Google’s security team explained in a blog post.
“For example, an unauthorized party may read sensitive information in the system’s memory such as passwords, encryption keys, or sensitive information open in applications,” the Google post said. “Testing also showed that an attack running on one virtual machine was able to access the physical memory of the host machine, and through that, gain read-access to the memory of a different virtual machine on the same host.”
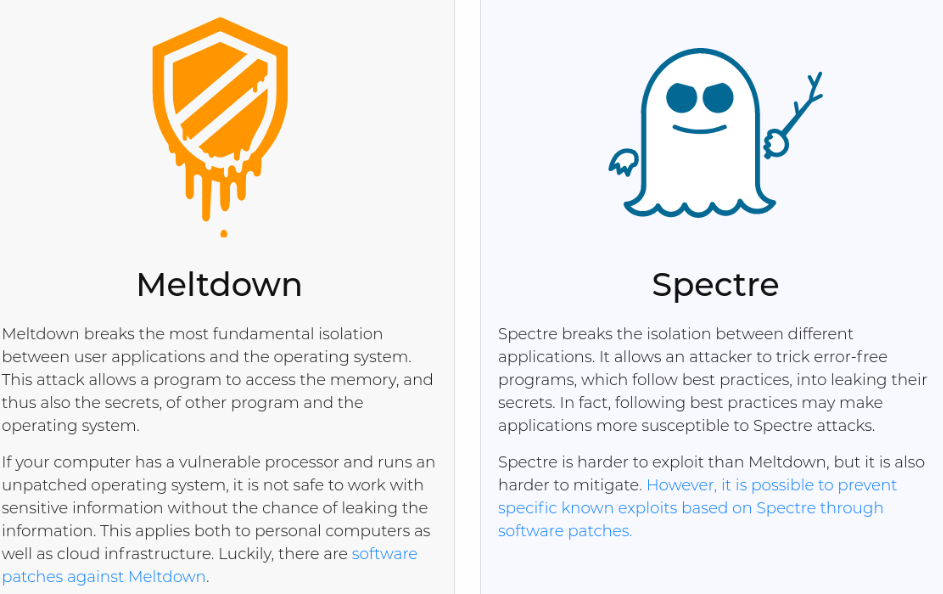
Spectre allows an attacker to trick programs into leaking their secrets even if they follow best security practices. Horn and researcher Paul Kocher have been credited with discovering the attack.
Meltdown breaks the isolation between user applications and the operating system, allowing a program to inappropriately access memory and a machine’s secrets. It was discovered three independent teams including Google Project Zero, Cyberus Technology and another team at Graz University of Technology in Austria.
Intel awarded an unknown sum as a bug bounty to the Graz University of Technology researchers.
The bug is called Meltdown because it melts security boundaries normally enforced by hardware. Spectre derives its name from speculative execution, the process by which a computer system performs a task that may not be actually needed.
The official references are CVE-2017-5753 and CVE-2017-5717 for Spectre and CVE-2017-5754 for Meltdown.
The flaws impact Intel and ARM processors. AMD said there is a “near zero risk” to their own products and users in a statement released Wednesday. The researchers who discovered Spectre say they verified that it works on at least some AMD chips.
The security flaws were originally supposed to go public later in this month, but security researcher Erik Bosman tweeted proof-of-concept code. That tweet lead to wider public scrutiny, forcing the companies involved to quickly go public with their work.
“We are posting before an originally coordinated disclosure date of January 9, 2018 because of existing public reports and growing speculation in the press and security research community about the issue, which raises the risk of exploitation,” Google’s security team explained.
Patches for Windows, MacOS, Android and Linux are available, so users are encouraged to quickly patch the flaw. Amazon and Microsoft recently told customers that major security work and maintenance is on the way.
At this point, the full extent of the impact is not yet clear.






