How Microsoft’s Azure platform can help agencies with the Cybersecurity EO
Microsoft Security Response Center research into recent cyberattacks indicates that the average time for infection or exploitation of an unpatched node on a compromised network is as little as 90 seconds. Verizon’s Data Breach Investigation Report found that 12 percent of phishing mail recipients will click on a link or attachment in under four minutes. And the Presidential Executive Order on Cybersecurity noted that “Known but unmitigated vulnerabilities are among the highest cybersecurity risks.”
However, despite understanding the risks, many organizations struggle to maintain consistent security policies and practices that would ensure protection against known threats. Why?
I believe it’s ultimately a question of risk management culture and resourcing. Cybersecurity is a practice, requiring consistency and repeatability — goals which are difficult to achieve where humans are involved. Adding to that, when security is successful, it is also invisible, which can impact resource prioritization. Though we know what we should do, we may not be properly focused on execution until crisis strikes.
As the CISO for Azure Government, one of my responsibilities is to ensure that our infrastructure is not vulnerable to known weaknesses. I also ensure that platform’s security is our highest priority. Microsoft Azure is one of the world’s largest and most complex information systems, offering dozens of unique services and representing millions of assets worldwide. Due to our scale, we can dedicate significant resources toward cybersecurity and the automation of cybersecurity. Through hyperscale automation, we achieve consistent and repeatable security practices.
The Executive Order directs agency heads to prefer the procurement of shared IT services for email, cloud, and cybersecurity services. The use of shared services allows mission owners access to the same scale advantages enjoyed by Azure, without having to make the same level of investment; Microsoft spends more than $1 billion annually on cybersecurity.
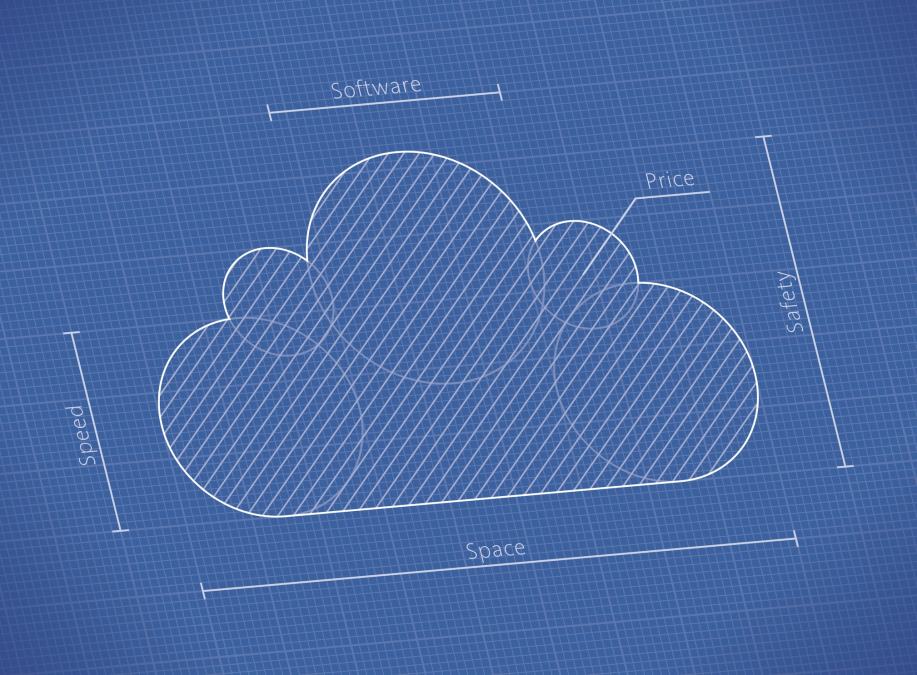
Unfortunately, not all shared IT service models are equal, especially when it comes to cybersecurity. It may seem like the easiest way to enjoy the benefits of shared service security is to “lift and shift” existing applications to the cloud using an Infrastructure-as-a-Service (IaaS) implementation. While that will eliminate the risks related to end-of-life hardware, it leaves the system owner with responsibility for patching and securing the configuration of their operating systems. Even cloud providers who offer “managed services” to maintain software on behalf of customers still require human administrators; simply moving the costs and prioritization challenges from one organization to another.
A Platform-as-a-Service (PaaS) model allows customers to eliminate the risk of “known but unmitigated” vulnerabilities altogether. PaaS services follow the evergreen model of IT management, meaning the underlying infrastructure is always up to date. PaaS services allow federal agencies to run complex, custom applications, without having to worry about the security risks related to patch management or configuration. Architecting applications to use PaaS services, rather than replicating those services in an IaaS infrastructure, ultimately improves security, enables scalability and reduces cost.
I understand that architecting completely for PaaS may be easier said than done for many applications, and those applications may not be slated for modernization, refresh or any additional funding for years to come. However, portions of nearly any application can be “lifted-and-shifted” to PaaS without significant modification. For example, most modern applications use a web front end. That web code can be easily shifted to a “PaaS Web Apps” service, even if the backend remains on premises, or better yet is itself shifted to an IaaS implementation. This type of hybrid implementation ensures that the “front door” for the application, likely its most frequently attacked surface, is on the most secure platform.
The use of shared cybersecurity services can be especially helpful in these types of hybrid cloud deployments, bridging the gap between traditional IT and evergreen platforms. Even applications that can’t move any processing to a PaaS architecture can still benefit from the use of shared cyber services. For example, reliable, cloud-integrated backup and recovery solutions can protect important applications and workloads, no matter where they reside; correctly configuring these backups can protect against ransomware attacks.
A shared cybersecurity management service allows an organization to manage diverse operating systems, in any instance of any cloud, including on-premises. These services enable you to collect and analyze machine data from virtually any source. Data generated across devices, operating systems, workloads and user actions provides instant access to critical information through one integrated console. For example, is the fleet vulnerable to latest cyberattack?
Cybersecurity management consoles allow organizations to easily deploy patches and make configuration changes across their entire fleet. A single operator can use the intelligence of the log analytics engine to deploy, defend, and modify infrastructure to protect against known vulnerabilities, or respond dynamically to zero day attacks. These consoles also allow an administrator to quickly respond to anomalous behavior, similar to the cybersecurity processes Microsoft uses to manage the security of our global cloud assets.
The publication of the Executive Order provided a directive for change and focused attention on the cybersecurity risks facing the federal community, creating an opportunity for change. We have the chance to rethink our risk management culture and reprioritize resources toward cybersecurity. We have the impetus to accelerate federal IT modernization. All at a time in history when shared IT services, especially those of the hyperscale cloud computing providers, are simultaneously improving cybersecurity and reducing cost.
Microsoft is committed to assisting our customers in complying with the Executive Order, addressing the core risks it outlines, and implementing the NIST Cybersecurity Framework as it requires. We offer shared IT services for email, cloud, and cybersecurity services that align with the framework. Over the course of the Executive Order reporting period, we will publish self-service guidance for implementing the framework; risk assessment templates based on our own, internal, framework risk management program; videos demonstrating the shared cybersecurity service capabilities of our cloud platforms; software for automated deployment of framework aligned applications; and we will sponsor community discussion through in person roundtables, webinars, and “white glove” sessions with agencies.
Please visit http://aka.ms/cybersecurityeo for our current content and schedule of events.