Critical ManageEngine vulns affect majority of Fortune 500 companies

A new set of vulnerabilities in a network management tool used by nearly two-thirds of Fortune 500 companies is the latest example of how high-consequence IT software can serve as a launching pad for bigger breaches.
Five vulnerabilities in the ManageEngine Applications Manager and one in the Event Log Analyzer were disclosed this week by cybersecurity firm Digital Defense, Inc.
Digital Defense has worked with ManageEngine’s vendor, Zoho, on mitigating the vulnerabilities.
The flaws have not yet been assigned a number in the CVE list, but some are likely to be rated critical, since they would allow an attacker to remotely take total control of an affected system.
The vulnerability disclosures were reviewed for CyberScoop by security firm Tenable.
“These are bona fide vulnerabilities,” said Tom Parsons, Tenable’s director of product management. “They would provide a good beach-head” for an attacker, because a software package like an application monitor “provides broad visibility across the enterprise.”
Applications Manager is a network resource monitoring tool that gives IT staff very detailed data about the performance of various tools across the enterprise — enabling them to identify which programs might be hogging system resources or causing computing bottlenecks.
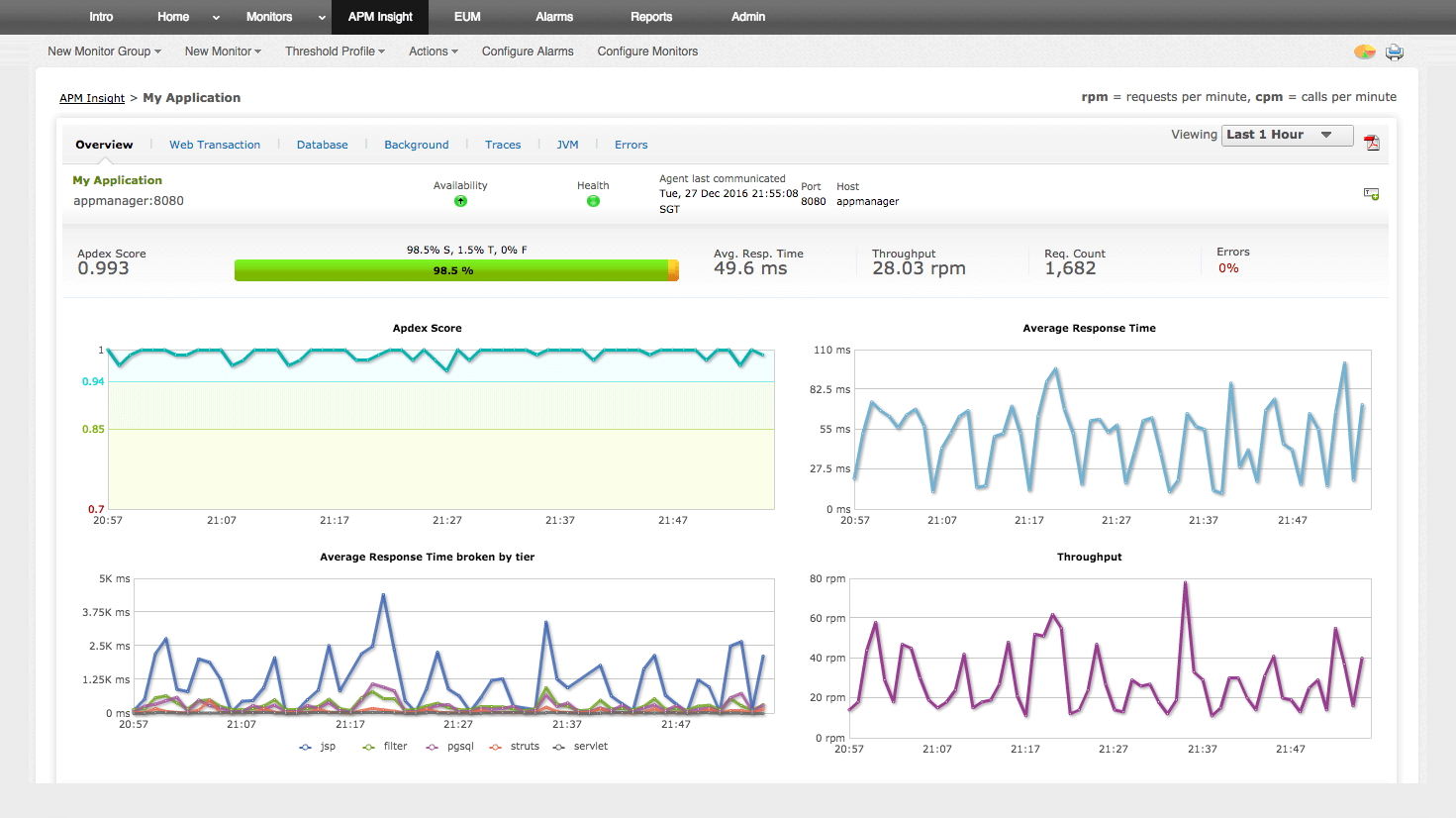
A dashboard offered by ManageEngine’s Applications Manager (Source: ManageEngine)
Currently, according to the Zoho website, ManageEngine products are used by more than 180,000 companies worldwide, including 300 on the Fortune 500.
“Security is a top priority for ManageEngine,” Zoho said in a statement emailed to CyberScoop, “When these vulnerabilities were discovered, we immediately worked to release security patches to mitigate the risk of any potential attack. ManageEngine customers have been notified of the potential threat and how to eliminate any related exposure.”
Most of the vulnerabilities disclosed this week stem from the way Applications Manager handles POST and GET requests — communications used to establish a connection between a client machine and a server in a computer network, or between a web browser and an application.
Parsons told CyberScoop that Tenable researchers themselves had disclosed two other sets of vulnerabilities in ManageEngine products last year.
And this latest announcement from Digital Defense is the second set of security holes in ManageEngine tools that its vulnerability research team has revealed since January.
Mike Cotton, Digital Defense’s senior vice president of engineering, told CyberScoop that isn’t a coincidence.
“I do think there’s a trend in vulnerability research to look for more strategic weak points in IT infrastructure … like ManageEngine,” he said.
Digital Defense’s researchers first came across the software during penetration-testing engagements — when they attempt to break into a customer’s computer network to find its weak spots. ManageEngine software “was part of the attack surface that we were contracted to test out,” Cotton said.
When deciding on targets for vulnerability research, he added, “We do look tactically at the software packages [our pen-testing clients are] using, but also more broadly, we look at the [IT] ecosystem we see all around us.”
ManageEngine had a “big footprint in the Fortune 500,” that made them an attractive place to start looking for bugs, Cotton said.
And Parsons pointed out that, once you find one bug in a product, others will often follow.
“There are opportunistic finds … as you investigate a disclosure and start looking at the code, you quite often find tangential vulnerabilities in the same software,” he said.





