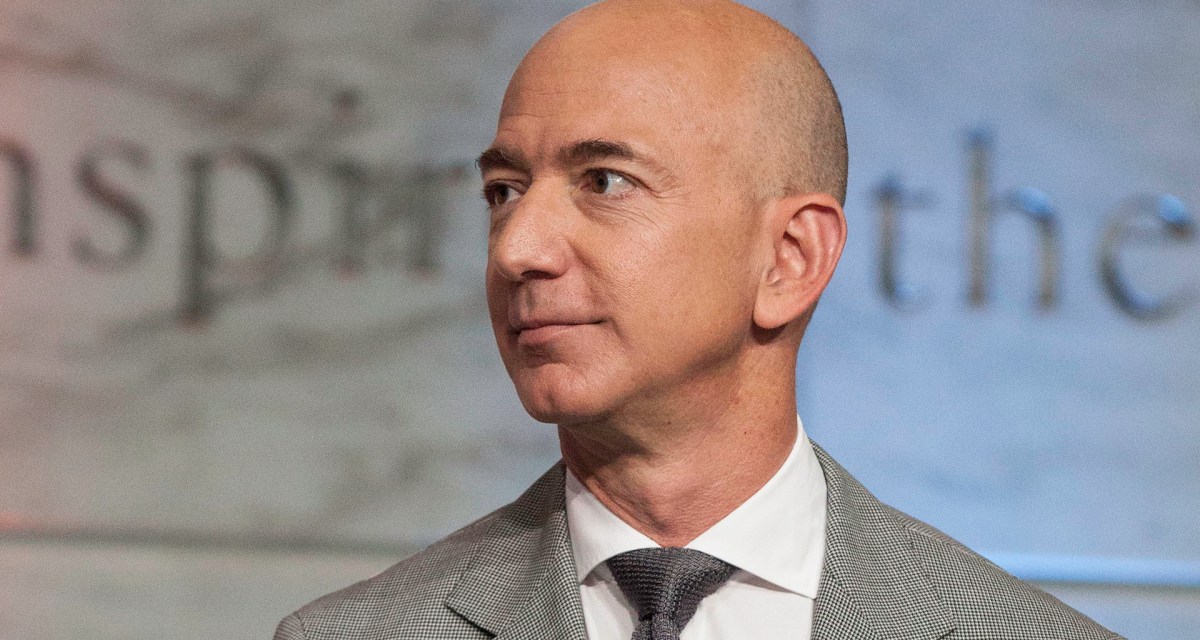
The big questions from FTI’s report on the Jeff Bezos hack
A cybersecurity forensics team has concluded with “medium to high confidence” that Saudi Crown Prince Mohammed bin Salman hacked Jeff Bezos’ iPhone X in 2018, but the analysis has not impressed the information security community.
The firm, FTI Consulting, may have good reasons to conclude there was unauthorized exfiltration of data from Bezos’ phone after bin Salman sent him a WhatsApp message containing a suspicious video file. But the publicly available information about FTI’s work has left many cybersecurity experts with questions about who really hacked Bezos’ phone and how the attackers did it.
The report — published Wednesday by Motherboard after a United Nations statement had summarized its findings — is a rare look into the forensic analysis of a device suspected to be the target of nation-state hacking. And given Bezos’ high profile as the owner of The Washington Post and the founder of Amazon, the case is likely to draw intense scrutiny for the indefinite future.
For now, the published information has left many observers unsatisfied. Alex Stamos, the former CISO of Facebook, which owns WhatsApp, said the FTI report didn’t go far enough in its analysis.
“This FTI forensics report is not very strong. Lots of odd circumstantial evidence, for sure, but no smoking gun,” Stamos said. “The funny thing is that it looks like FTI potentially has the [device] sitting right there, they just haven’t figured out how to test it.”
FTI declined to comment.
The company’s cybersecurity team is led by people who have been responsible for the protection of U.S. government entities at the highest levels, including the FBI and the White House. Its credentials aren’t in question. The report, though, left several things unanswered, the experts say:
Why couldn’t FTI decrypt the downloader?
FTI concluded it could not analyze the downloader, the file that allegedly delivered, the .mp4 video responsible for the infection through WhatsApp. The downloader was encrypted, FTI said.
But based on what’s included in the report, FTI should have been able to decrypt the file, Bill Marczak, a research fellow at Citizen Lab, a University of Toronto rights group that investigates digital espionage, told CyberScoop.
“Sufficient information to decrypt the file should be present in the forensic extraction performed by FTI,” Marczak, who wrote a blog post on other issues FTI failed to address, told CyberScoop.
Matt Green, an associate professor of computer science at Johns Hopkins, told CyberScoop the .enc file cited in the report indicates the keys to decrypt the downloader would have been found alongside the file itself.
“This is encrypted using keys that should also be stored on the device which raises the question of why they haven’t decrypted it and examined what’s inside,” Green told CyberScoop. “This should be decryptable using local keys if they’re around.”
One possible explanation is that the keys were somehow taken out of the equation. The hackers could have designed the attack to destroy the downloader or the encryption keys, in theory. It’s not clear that that’s the case, however.
Is the report’s data accurate?
FTI reports that after bin Salman sent the video file, “within hours … a massive and unauthorized exfiltration of data” began, followed by “anomalous spikes in egress data.” But the numbers accompanying some of the graphs don’t always match what the graph says, according to Rob Graham, a well-known cybersecurity expert who created the first intrusion prevention system.
Another data point that has raised questions is the fact that the baseline of data transmitted out from Bezos’ phone before the bin Salman text exchange is low — a daily average of 430KB.
That’s “less than the background traffic for most phones,” Cisco Talos’ Craig Williams said.
Was there actually any malware?
The FTI analysis “did not identify any malware on the device,” raising questions about whether the Saudi Kingdom actually successfully infected Bezos’ phone with malware.
Of course, even though no known malware strains were found on the phone, there could still be something hiding — a point that FTI conceded in the report. But Graham said that point doesn’t support the notion that what occurred was the result of a hack.
“I see nothing here that suggests Bezos’ phone was hacked. It contains much that says ‘anomalies we don’t understand,’ but lack of explanations point to incomplete forensics, not malicious APT actors,” Graham tweeted.
There’s one process that FTI didn’t complete that could reveal mobile malware on the phone: jailbreaking the iPhone to analyze the root file system. It wasn’t clear why the analysts didn’t do that.
“If FTI doesn’t have the capability to do this analysis themselves, then they should ask for WhatsApp’s help in decrypting the file and then should allow FB and Apple to investigate,” Stamos said. “[T]he idea that this report is the furthest you can go with access to the phone is wrong. The circumstantial evidence is reasonably compelling, but since this is a major national security issue now more eyes need to be on the evidence.”






