Iranian hackers heisted U.S. defense software for clients blocked by sanctions, indictment says

A group of Iranian hackers broke into multiple U.S. defense contractors between 2007 and 2013 in order to steal intellectual property, software and other proprietary information that they then sold to foreign enterprises and governments, including the Iranian government, according to a newly unsealed indictment by the Department of Justice.
The indictment, published Monday, effectively shows how the Iranian government may have been able to circumvent previous export sanctions tied to the sale and purchase of U.S. defense technology by employing a group of contracted freelance hackers who would steal software products through a network of compromised computers based in the United States. The hackers allegedly stole software from Vermont-based engineering consulting and software design company Arrow Tech Associates and sold it to Iranian clients.
The product, PRODAS, is a software platform designed for aerodynamics analysis and design for projectiles. It sells for $40,000 to $800,000, and customers receive a dongle to download a software license from an Arrow Tech website. According to federal data, the Air Force, Army and Navy have contracts with Arrow Tech.
The hackers were able to steal the product by superseding the typical download process and redirecting it to preferred machines, the indictment says. The defendants allegedly maintained access to Arrow Tech’s internal IT infrastructure for several years, using it to download newer versions of the defense contractor’s flagship software. Because shipping Arrow Tech’s products outside the U.S. would have typically required an export license, the company was barred from doing normal business with Iranian clients.
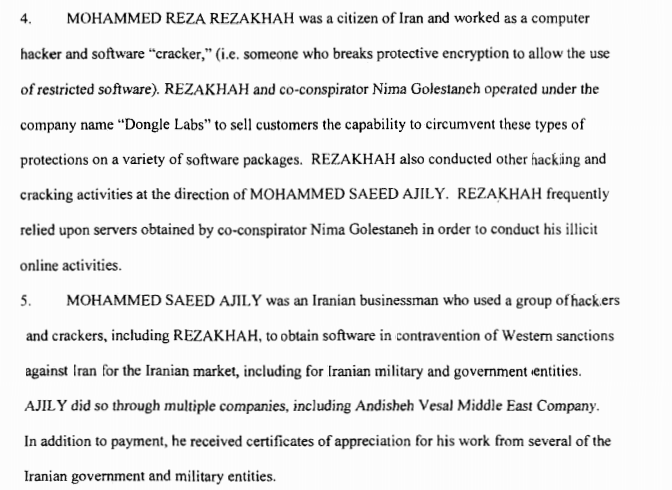
Based on court documents, the case involved multiple defendants, including hackers, Iranian businessmen and other unnamed associates. Two of the primary defendants, Iranian nationals Mohammed Saeed Ajily and Mohammed Reza Rezakhah, are charged with criminal conspiracy relating to computer fraud and abuse, unauthorized access to, and theft of information from, computers, wire fraud, exporting a defense article without a license and violating sanctions against Iran.
Excerpt from indictment – screenshot
Ajily acted as the lead businessman behind the operation, court documents note. After valuable computer code was stolen by Rezakhah, Ajily would typically market and sell the products to a small entourage of recurring customers, including Iranian universities, military and other governmental agencies. Although the indictment describes that Ajily and Rezakhah worked to “obtain software in contravention of Western sanctions against Iran for the Iranian market,” it’s not clear if they only targeted defense contractors as part of their criminal venture.
A third co-conspirator, Nima Golestaneh, is also briefly mentioned in the indictment for his participation in the economic espionage operation. Golestaneh, a university student who was extradited from Turkey, already pleaded guilty in a federal court in Vermont for related conduct in 2015; at the time, little was known about the scale and scope of his criminal activity.
As part of this operation, the hackers allegedly launched their attacks from a series of infected servers belonging to companies based outside both Iran and the U.S. The hackers did so — which in included a server in the Netherlands and Canada — in an effort to obfuscate their own identities. A criminal investigation into the matter began around 2007. It’s not entirely clear from the indictment how many or which companies were victims of Rezakhah and Ajily’s computer crime scheme. Only one victim organization is specifically mentioned by name in the indictment.






