IBM shipped malware-laden USB sticks to unsuspecting customers

Malware-laden USB sticks were accidentally sent by IBM to a series of enterprise customers that had purchased storage systems developed by the computing giant, according to a company advisory published last week.
An unidentified number of these drives were mailed as an installation tool for users setting up IBM Storewize V3700 and V5000 Gen 1 storage systems. IBM says that all of the infected USBs carried the same serial number: 01AC585.
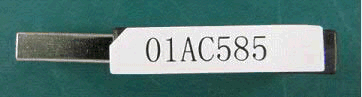
Images via IBM
An IBM spokesperson did not respond to CyberScoop’s inquiry. It remains unclear how the malware originally found its way onto the drives.
When plugged into a vulnerable system, the memory stick will immediately launch the legitimate Storewize initialization tool, which in this case also carries hidden malicious computer code that copies itself to a temporary folder. Fortunately, the malware itself is not executable, meaning that it won’t automatically run on a computer in order to infect the Storwize disks.

The advisory by IBM identifies the malware as “W32.Faedevour!inf,” which Symantec notes is “a worm that opens a back door and steals information from the compromised computer.” The malware variant is part of a family of computer viruses, labeled “WIN32” by security researchers, which has been used by cyber criminal gangs in Eastern Europe and Russia.
IBM recommends that potential victims scan their systems with an antivirus tool and manually remove the folder (%TMP%\initTool on Windows and /tmp/initTool on Linux or Mac) where the malware is commonly stored. Additionally, affected parties are advised to physically destroy the contaminated hardware so that it can’t be reused by anyone.
The incident underlines the inherent security challenges assumed by companies that deal with global supply chains, where individual components to construct a specific products are manufactured in different locations and by different companies based in foreign countries.




