Hackers find unpatched servers to secretly mine $17,000 in Monero per month

Secretly mining cryptocurrency by using the machines of unsuspecting victims is a malicious ploy that was invented almost as soon as cryptocurrency came into being.
Just this week, two such schemes surfaced. An operation has been infecting Windows web servers with a silent Monero miner since at least May 2017 to net $63,000 worth of the currency, say researchers from cybersecurity firm ESET.
Cryptocurrency mining, put simply, is when powerful computer processors solve immense math problems that take considerable time and energy. Solving the problems rewards miners with digital currency like bitcoin, Monero and so on. It costs money to power the computers that do the mining, so hackers who sneakily employ other people’s machines are avoiding expenses. The big electricity bill that results is suddenly another person’s problem.
New research from ESET shows that hundreds of unpatched servers were infected with a known vulnerability — labeled CVE-2017-7296 — and used to mine Monero for the hacker’s profit.
The hacker used software called “The Cryptominer” that simply took normal mining software and hardcoded in the attacker’s wallet so all the money went there. The hacker performed large-scale scans searching for the CVE-2017-7296 vulnerability, first discovered in March 2017.
“This vulnerability is especially susceptible to exploitation, since it’s located in a webserver service, which in most cases is meant to be visible from the internet and therefore can be easily accessed and exploited by anyone,” ESET’s researchers wrote. The attackers have been actively exploiting the vulnerability since May and had an especially profitable month in August.
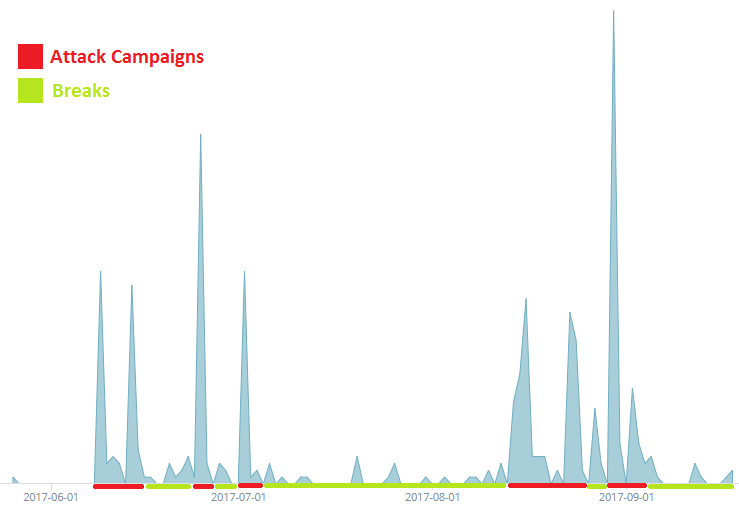
Infection waves over time. Credit: ESET
Websites owned by the premium cable channel Showtime were found to be mining Monero via site visitors’ machines. The offending scripts were shut down once the public caught on.
Monero is a three-year-old cryptocurrency designed for greater privacy than bitcoin. According to Europol researchers, bitcoin remains far and away the top cryptocurrency but alternatives are gaining popularity with cybercriminals because of the distinction from bitcoin. As of publication, Monero’s price is approximately $97.
“Launched in 2014, much of Monero’s growing popularity relates to the additional security and privacy features it offers,” Europol’s researchers wrote this week. “Transactions cannot be attributed to any particular user/ address, all coins used in a transaction are ‘hidden’ by default, and transaction histories are kept private. Monero is now accepted on a number of dark net markets, and 2017 saw the first ransomware, Kirk, which used Monero for ransom payments.”
The newly discovered campaign is low-sophistication but it made nearly $16,000 per month for the attackers. Unpatched machines are sitting ducks for hackers, especially those who can profit from relatively quiet attacks. Earlier this year, Chinese hackers executed an almost identical scheme to the tune of $25,000 per month.
“Sometimes it takes very little to gain a lot,” ESET’s researchers explained, “and this is especially true in today’s world of cybersecurity, where even well-documented, long-known and warned about vulnerabilities are still very effective due to the lack of awareness of many users.”




