Hacker exploits router zero-day vulnerability in efforts to build Mirai-like botnet
Hackers are attacking hundreds of thousands of Huawei routers with variants of Mirai malware in a bid to build a massive botnet like arsenal used in global cyberattacks in 2016, according to the Israeli cybersecurity firm Check Point.
A zero-day vulnerability in the Huawei home router HG532 is being exploited to deliver a payload called Satori (or Okiru) by an amateur identified as “Nexus Zeta,” Check Point says.
Mirai malware was first discovered in August 2016. By October of that year, it was behind the vast denial-of-service attacks against the Domain Name System provider Dyn. The offensive brought down a wide array of services, including Twitter, Reddit, CNN, Fox News, Visa and Slack. Earlier this month, three men pleaded guilty to their roles in creating, operating and selling access to the botnet.
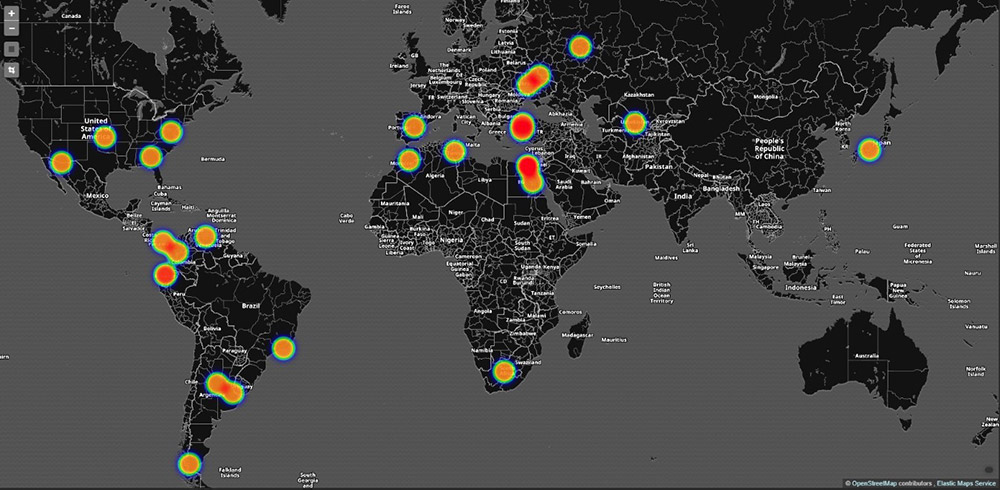
Beginning in November 2017, Check Point detected global attacks against Huawei HG532 devices. One day later, the Chinese security firm Qihoo 360 Netlab spotted 100,000 IP addresses in Argentina tied to attacks from the new Mirai variant. Huawei, a Chinese hardware giant, confirmed the zero-day exploitation in a blog post released in late December.
Satori’s payload is simple in that it floods targets with manually crafted UDP or TCP packets, researchers explained.
“An authenticated attacker could send malicious packets to port 37215 to launch attacks. Successful exploit could lead to the remote execution of arbitrary code,” Huawei’s security team wrote.
Check Point’s investigation into the perpetrator behind the attacks led to an amateur nicknamed “Nexus Zeta” operating on HackForums.net, a technical forum popular with generally low-skill, young males new to the hacking world. The website has a long history with cybercrime and in September 2016 it was the place where Mirai source code was publicly posted.
Courtesy of Check Point’s investigation, here’s Nexus Zeta’s post on that forum just before the attacks began:
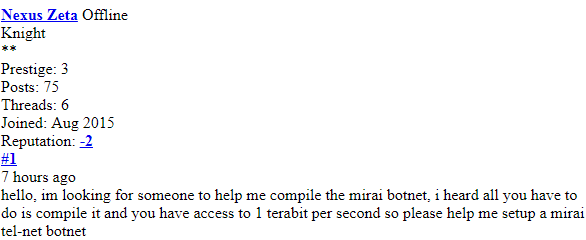
Nexus Zeta’s HackForums post (Check Point)
“Indeed, he had recently been active in hacker forums seeking advice on how to build such an attack tool indicating that a combination of leaked malware code together with exploitable and poor IoT security, when used by unskilled hackers, can lead to dangerous results,” Check Point researchers wrote.
Huawei released updated intrusion prevention signatures on Dec. 1 to block exploitation. Further defense against these attacks is simple: Change the device’s default password and configure the built-in firewall.
Experts urge changing default credentials as a regular practice. Default usernames and passwords are almost always easily available on the public internet.




