FIN7 scammers posed as SEC officials, sick restaurant customers to hack victims

A hacking group known for innovative fraud techniques impersonated angry restaurant customers and targeted specific individuals with unique access to financial information, U.S. prosecutors argue in a court filing that sheds new light on the scammers’ work.
The FIN7 gang, which researchers have blamed for more than $1 billion in theft since 2015, relied on more than 70 members who were assigned to various departments under the larger organization, according to court documents filed on June 17 in U.S. District Court in Seattle.
By masquerading as a cybersecurity testing company dubbed Combi Security, FIN7 leaders organized their personnel into separate teams charged with developing malware, crafting phishing documents and collecting money from breached victims. The group targeted hundreds of U.S. companies, prosecutors say, infecting victims as diverse as the burrito chain Chipotle and the department store Saks Fifth Avenue.
Court documents filed in the case of Andrii Kolpakov, who pleaded guilty in November to working as a kind of recruiter for the hacking gang, help illustrate how the group was so successful. Kolpakov, a Ukrainian national, hired and supervised computer specialists as part of the scheme. Prosecutors this month asked a judge to sentence Kolpakov to seven years in prison at his next court hearing.
In order to help demonstrate Kolpakov’s guilt, prosecutors included screenshots of messages that FIN7 emailed to apparent hacking victims.
In one message to a manager at an unnamed restaurant chain, a person claiming to be a customer named “Oliver Palmer” claimed that a corporate outing to the restaurant ended with the entire group falling ill with diarrhea, which “affected the financial component of the company.”
The message included a malicious .rtf attachment that appeared to be a lawsuit threat. Similar messages to other email addresses impersonated caterers or party planners hoping to book reservations for large groups.
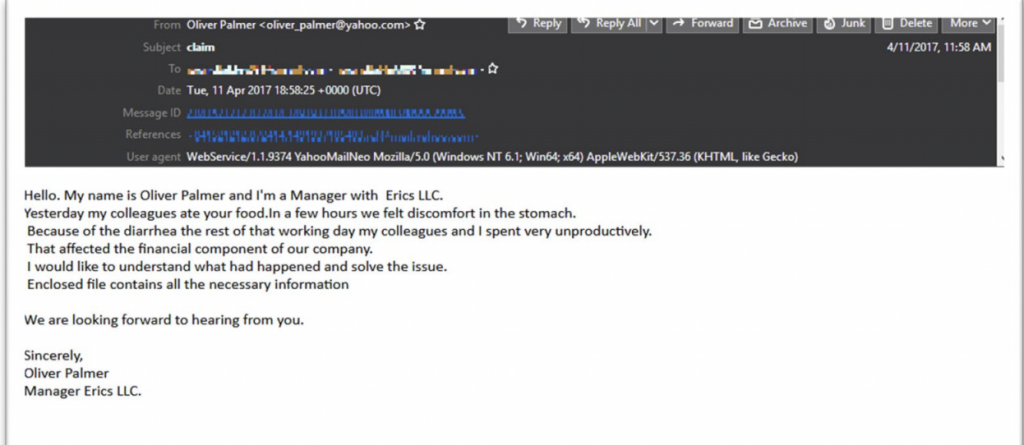
(Department of Justice)
In another message, fraudsters spoofed an email address from the U.S. Securities and Exchange Commission. They sent a message to an in-house corporate counsel at a publicly traded company who was responsible for the firm’s securities filings. The unnamed attorney was properly “induced by the seemingly legitimate email and the significance of the purported subject” to activate the attached malware.
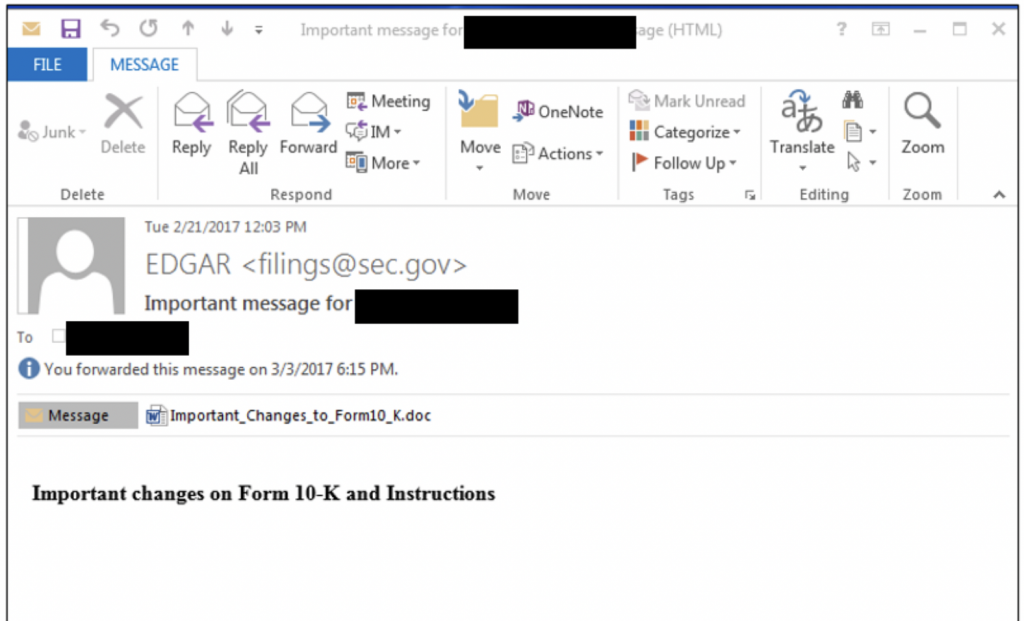
(Department of Justice)
As FIN7’s business model proved successful, the group updated its phishing messages to include Microsoft and Google logos to boost their legitimacy. The thieves would then sell their stolen data on illicit markets like the Joker’s Stash, a forum where buyers and sellers traded stolen personal information. (The site has since closed.)
Fedir Hladyr, another FIN7 administrator, was sentenced in April to 10 years in prison and ordered to pay $2.5 million in restitution.
The latest court filing is available in full below.
https://www.documentcloud.org/documents/20970594-kolpakov_sentencing_request






