FBI accuses Russian man of laundering money for a transnational cybercrime network

FBI agents have arrested a Russian citizen accused of laundering money for a cybercriminal gang that allegedly stole funds from a range of U.S. banks.
A complaint unsealed Monday against Maksim Boiko, 29, alleges that he worked with a transnational organized crime group, called QQAAZZ, by converting stolen money into cryptocurrency.
The Russian man is “a significant cybercriminal who launders money for other cybercriminals” by giving them access to criminally controlled ban accounts, an FBI affidavit says. U.S. authorities previously indicted five Latvian men for their alleged involvement in the QQAAZZ operation. According to prosecutors, hackers who breached victims’ bank accounts would contact QQAAZZ seeking an account to wire stolen funds as part of a kind of “global, complicit bank drops service.”
The Pittsburgh Post-Gazette and Seamus Hughes, the deputy director of the Program on Extremism at George Washington University and a specialist on court filings, first noticed the court records.
Boiko entered the U.S. in January with his wife, and $20,000 in cash, according to the FBI. He claimed he earned the money through bitcoin investments and by renting property in Russia. In fact, pictures on Boiko’s Instagram page showed the young man holding stacks of cash reaped through criminal activity, the FBI said. Agents also searched through his Apple iCloud account to determine that some of the funds had been laundered through Chinese bank accounts, the affidavit said.
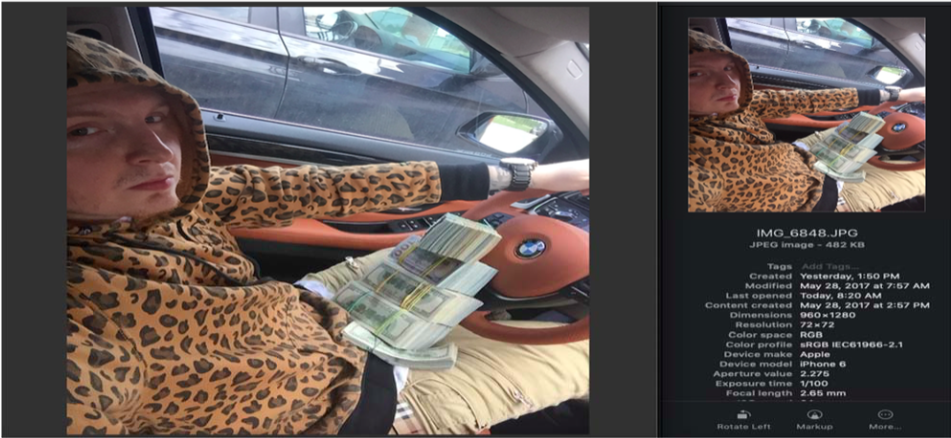
The FBI alleges that Maksim Boiko, a 29-year-old Russian, has spent years laundering stolen money. (FBI)
“To hide his true identity, Boiko sometimes used an online moniker known as ‘Gangass’ in furtherance of his criminal activities,” court documents allege. “To conceal communications with his cybercriminal clientele, he utilized secure and encrypted Jabber instant message platforms, to include ‘exploit.im’ almost exclusively used by cybercriminals.”
Data from Boiko’s account showed that he received $387,964 worth of deposits and had withdrawn roughly 136 bitcoin, the FBI said, which was worth $865,748 at press time.
This is the latest update in the FBI’s ongoing case against the QQAAZZ collective, which the bureau says has been active and includes a dozen members in countries including Georgia, Bulgaria and Latvia.
Members have spent years opening personal and corporate bank accounts, including at JP Morgan Chase and PNC Bank, “for the sole purpose of using the accounts to receive stolen funds from victims.” The group typically uses malware that captures victims’ usernames and passwords, then it directs co-conspirators to start withdrawing money. They have also used a range of aliases on the Jabber messaging platform, including “richrich,” “salazar001” and “donaldtrump55.”
The FBI’s affidavit is available in full below.
[documentcloud url=”http://www.documentcloud.org/documents/6821383-Maksim-Boiko.html” responsive=true]






