Ukraine blames infamous Russian hackers for ‘BadRabbit’ ransomware attack

A group of hackers believed to be associated with Russia’s Main Intelligence Directorate (GRU), better known as APT28 or Fancy Bear, was responsible for last week’s international ransomware attack dubbed “BadRabbit,” according to Ukraine’s top law enforcement agency, the Security Service of Ukraine (SBU).
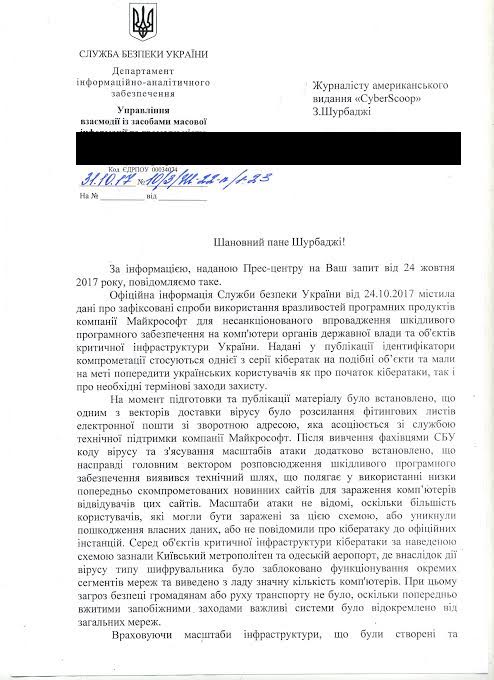
In a letter sent to CyberScoop on Wednesday, SBU officials laid blame on APT28 for launching the massive, coordinated attack that disrupted business operations for hundreds of organizations based in Ukraine and Russia. Victims included multiple Russian news outlets, government organizations in both countries and Ukrainian transportation services.
An official with Ukraine’s state cyber police announced Thursday, as part of an interview with Reuters, that the hackers behind BadRabbit intended for the ransomware to effectively act as a smokescreen while they simultaneously sent highly targeted phishing emails to several organizations. The phishing emails were designed to gain access to “financial and confidential information.” The state cyber police did not name the group responsible during their interview with Reuters.
It’s not clear if APT28 also conducted the phishing component of this expansive, well-disguised espionage operation.
Cybersecurity firms FireEye, Cisco Talos and Kaspersky Lab all concluded that BadRabbit was spread through a collage of compromised websites which dispensed the malware to unsuspecting web visitors.
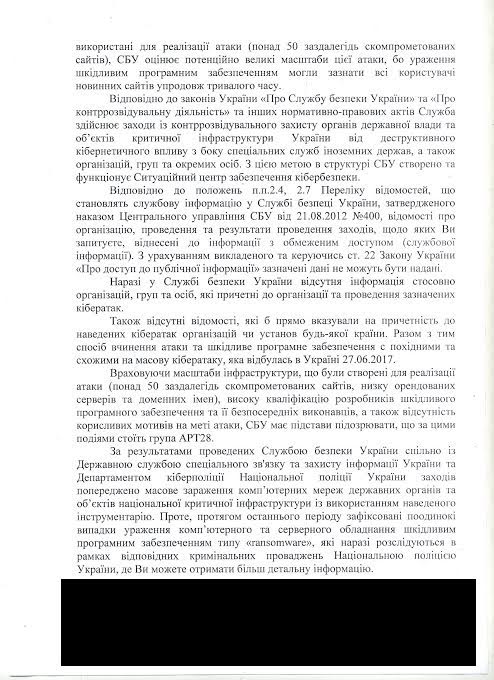
“Given the scale of the infrastructure created for the attack (more than 50 pre-compromised sites, a number of leased servers and domain names), high qualifications of the developers of malicious software and unbiased performers, as well as the lack of mercenary motives for the purpose of attack, the SBU has reason to suspect, that the group APT28 is behind these events,” the letter written by the SBU and translated by CyberScoop reads.
Three separate analysts translated the document, sent to CyberScoop as a JPEG, in order to verify the provided information.
The SBU did not provide further evidence to support this claim. A subsequent email requesting additional information had yet to be answered prior to this article’s publication.
Cybersecurity researchers say APT28 is linked to the GRU.
Slovakian Cybersecurity firm ESET previously connected “BadRabbit” to a hacker group known within the security research community as “Telebots” or “Sandworm group.”
Two former U.S. intelligence officials, who spoke on condition of anonymity to broadly discuss the government’s understanding of the so-called Sandworm group, said that this entity acts as a subunit of APT28.
APT28 is best known for breaching the Democratic National Committee during the run up to the 2016 U.S. presidential election.
Cyberpolice Ukraine, the country’s police department dedicated to cybercrime, did not respond to a request for comment.
To accurately attribute a specific data breach to an individual group, country or hacker remains a notoriously difficult thing to accomplish. Experts say the organizations best equipped to do so include intelligence agencies, however, because they are capable of collecting information from both human and machine-based sources.
The original letter sent to CyberScoop by the SBU can be seen below:
Zaid Shoorbajee contributed to this report.






