European police round up 23 suspected scammers accused of $1.2 million fraud

An international police sting netted 23 arrests in three countries of suspects behind a business email compromise scheme that last year turned to capitalizing on COVID-19 fears, Europol announced on Wednesday.
Together, the fraudsters are believed to have stolen at least $1.2 million from companies in 20 countries, mainly European and Asian nations, the European Union police agency said.
The scheme relied on use of compromised email accounts for advance-payment fraud, Europol said. The suspects created fake emails and websites that resembled those of legitimate companies to trick victims into placing orders with them. They then laundered financial data through Romanian bank accounts to ultimately withdraw money from ATMs.
“The fraud was run by an organised crime group which prior to the COVID-19 pandemic already illegally offered other fictitious products for sale online, such as wooden pellets,” Europol’s announcement said. “Last year the criminals changed their modus operandi and started offering protective materials after the outbreak of the COVID-19 pandemic.”
Besides Europol’s Cyber Crime Centre, the operation drew resources from three nations’ national police forces: Romania’s Politia Romana, the Netherlands’ Polite and Ireland’s An Garda Siochana.
The simultaneous raids in those three countries led to the arrests on Monday of nationals from African countries residing in Europe, resulting from searches of 34 locations. Europol said it had been supporting the case since 2017.
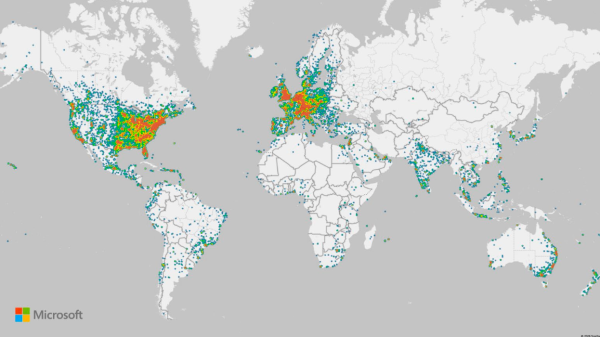
Business email compromise (BEC) regularly tops the list of most expensive cyber-enabled crimes in the annual accounting from the FBI’s Internet Crime Complaint Center, with the IC3 last year enumerating nearly $1.8 billion in known losses reported to the center.
Europol’s own annual report last year said BEC was on the rise, even as ransomware generated headlines due to the large number of victims.
“Business Email Compromise (BEC) continues to increase,” the agency said. “As criminals are more carefully selecting their targets, they have shown a significant understanding of internal business processes and systems’ vulnerabilities.”