Energy sector hacking campaign targeted more than 15 U.S. firms

More than 15 different U.S. energy companies received phishing emails as part of a recently uncovered hacking operation, based on a list of targeted organizations provided to CyberScoop by a person familiar with the ongoing investigation.
While evidence exists that ties these attackers to similar, past intrusion attempts against energy firms in Ireland and Turkey, the most recent wave of phishing emails — which began around early May — appears to have only been sent to U.S. companies, cybersecurity researchers and one government official told CyberScoop.
As this story was being published, there were reports of intrusion attempts into private energy companies in Ireland. This activity showed some similarities to what happened in the U.S. Ben Read, an analyst with FireEye, told CyberScoop that the Ireland-focused campaign predates the U.S.-focused hacking effort by the same group, because it occurred in March. A different set of phishing emails, tailored for non-American targets, were used at the time.
Sources told CyberScoop that approximately 18 U.S.-based energy companies had received the phishing emails, with other incidents being investigated for ties to the same attackers. The number of facilities affected is currently unclear, as the targeted email accounts could be tied to people who work at multiple plants or company installations. Phishing emails were sent to general business email addresses, including accounts related to “jobs@” and “invoices@.”
Some cybersecurity researchers believe the malicious emails were sent by a Russian hacking group as part of an expansive cyber-espionage operation that dates back to at least 2015.
The targeting profile is concerning, experts say, because it shows a concentrated and timely effort to compromise the U.S. energy sector. John Hultquist, head of FireEye’s cyber-espionage analysis division, previously told CyberScoop that the intrusions were likely done in order to gather information, rather than for financial gain.
On June 28, the FBI and Department of Homeland Security sent out a warning to U.S. energy companies to be on the lookout for an advanced persistent threat that was working to “harvest credentials in order to establish persistence on victims’ networks.” The threat actors would be using spear phishing emails and infected websites, according to a joint analysis report labeled “TLP:AMBER.”
Screenshot of JAR Energy report by DHS/FBI
“DHS and FBI identified common themes used by the actors, such as Microsoft Word attachments that appear to be legitimate résumés or curricula vitae (CVs),” the report, which was obtained by CyberScoop, details. “Once actors harvest victim credentials using spear-phishing emails, their payload maps network drives to collect configuration details on the infected system, enabling the actors to traverse the victims’ networks more effectively. This activity is still under investigation.”
If a user were to download the email attachment in question, it would activate a template file through a connection to Microsoft’s Server Message Block so that the user’s credentials can be harvested. By infecting a computer in this manner, the attacker can gather information that would help them conduct future intrusions.
A person familiar with the investigation said less than 30 U.S.-based organizations were targeted in the latest wave, but other cases may exist which are currently unknown to the FBI and Homeland Security Department. The U.S. energy companies targeted by the hackers range in size and location, from small energy distribution firms to regional monopolies.
CyberScoop reached out to a total of six U.S. energy firms that were known targets of the phishing campaign. All six either declined to comment, didn’t respond or said they would not disclose cybersecurity events to the press.
Each target was similarly sent a booby-trapped attachment from an email address that appears to belong to a legitimate Michigan-based construction business. Analysts believe the Michigan business was unaware that its email servers had been hijacked to send out spearphishing emails.
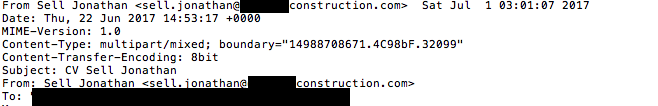
An example of the header for one phishing email used in the U.S. energy sector hacking operation. Names have been redacted to protect the privacy of potential victims.
Multiple foreign government agencies focused on cyber defense said that energy companies in their own countries had not been targeted as part of the recent energy sector-focused phishing campaign.
The German Federal Office for Information Security said that the country’s energy companies were not targeted. A spokesperson for the United Kingdom’s National Cyber Security Centre said the agency was prepared to respond if such a threat should arise, but indicated that the U.K had not seen such activity yet. A spokesperson for Poland’s Computer Emergency Response Team responded with an email: “[we] simply don’t have related data.”
Private sector cybersecurity experts say the attackers also compromised and planted malware on several websites that are commonly visited by individuals working in the U.S. energy sector.
The responsible party’s motive for these attempted intrusions remains unclear.
Ryan Johnston and Cassie Stephenson contributed to this report




