DMARC use continues to climb inside federal government

The number of federal government departments and agencies deploying the highest level anti-spoofing and anti-phishing email security has nearly doubled since the end of May, new figures show.
A total of 135 federal email domains had some form of the Domain-based Message Authentication, Reporting and Conformance (DMARC) protocol deployed Aug. 1, according to the non-profit Global Cyber Alliance.
That’s only six more than the 129 who had some deployment May 26 — but of those 135, 60 had the protocol set to p=reject, the highest level of deployment. That compares to just 32 who had the protocol fully deployed in May.
DMARC helps prevent phishing and other email spoofing attacks, when a message is made to look as if it comes from a company or government agency. The IRS, for instance, is a frequent target of phishers, who prefer to impersonate banks or other email senders who might have a financial relationship with potential victims. At lower levels, the protocol just warns the sender if someone is trying to impersonate their domain; but at the highest level, delivery of spoofed or unauthorized messages is blocked altogether.
Many of those 28 who moved up to the highest level of implementation are domains managed by the U.S. Department of Health and Human Services, like healthdata.gov, GCA CEO Phil Reitinger told CyberScoop.
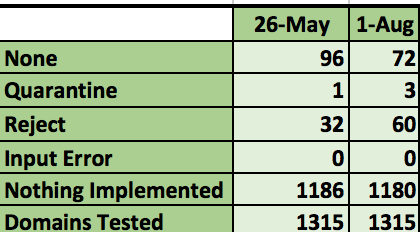
Federal DMARC adoption May-Aug 2017 (Source: Global Cyber Alliance)
At the lowest level of implementation, p=none, senders are warned when their domain is being spoofed. At the next, intermediate level, p=quarantine, senders and addressees are likely to find spoofed email diverted to their spam folder.
But when senders and recipients both fully implement DMARC, switching on p=reject, unauthenticated email messages appearing to come from the sender’s domain are simply not delivered to addressees. The problem is, that might include messages sent by a third party, for instance a marketing campaign or a email newsletter.
“The big change [from May until now] was in [domains] moving from a DMARC policy of ‘none’ to ‘reject,'” Reitinger said. “But fbiic.gov from the Federal Reserve moved from ‘no policy’ to ‘reject’ and the FBI moved from ‘none’ to ‘quarantine.'”
DMARC is an email authentication policy and reporting protocol first developed a decade ago, originally by PayPal.
Earlier this month, Sen. Ron Wyden, D-Ore., wrote to the Department of Homeland Security to use its government-wide cybersecurity authorities to require federal agencies to use DMARC and eventually implement “p=reject.”






