Code for massive ‘Memcrashed’ DDoS attack made public
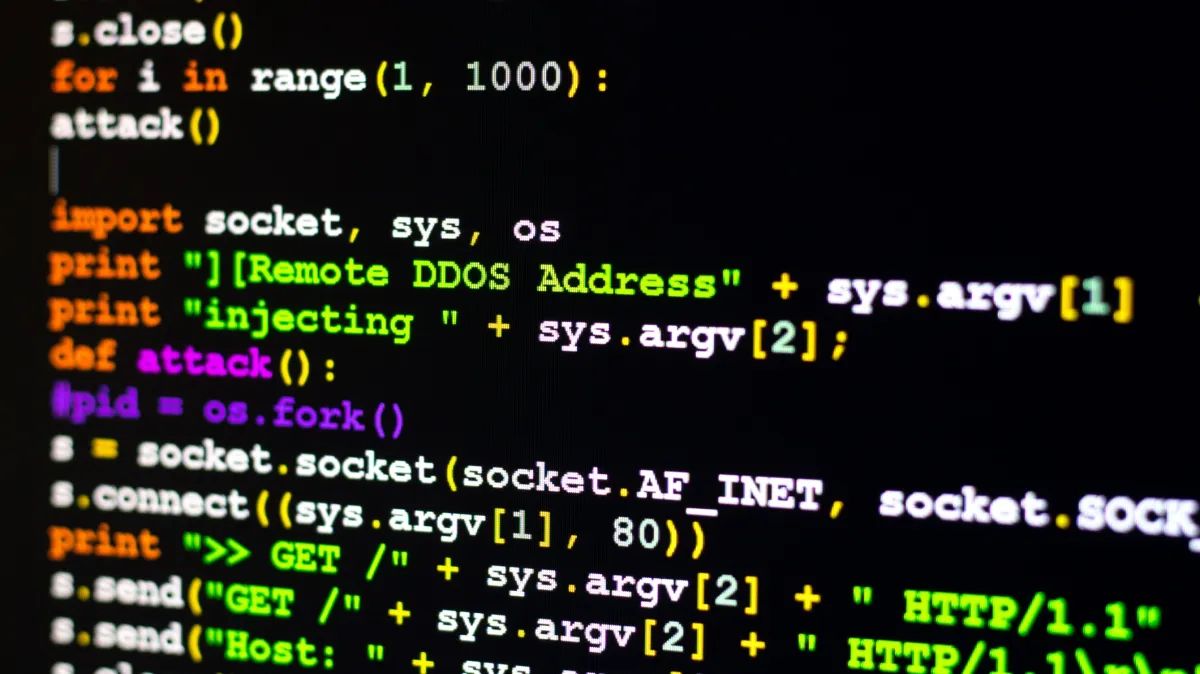
You, too, can now attempt a record-setting denial-of-service attack, as the tools used to launch the attacks were publicly posted to GitHub this week.
Proof-of-concept code by Twitter user @037 combined with a list of 17,000 IP addresses of vulnerable memcached servers allows anyone to send forged UDP packets to memcached servers obtained from the Shodan.io computer search engine.
It’s been just over a week since the first massive memcache-fueled denial of service attack. The code’s authors says it’s being released “to bring more attention to the flaw and force others into updating their devices.”
The era of terabit DDoS attacks was ushered in this month with giant denial of service attacks last week set records with 1.35-terabit-per-second and 1.7 -terabit-per-second attacks. They used unsecured memcached servers to launch the attacks, one of which targeted GitHub itself. The latter attack targeted an unnamed U.S. service provider, according to Arbor Networks.
A second tool was released on Monday, BleepingComputer reports, but the author is unknown.
Akamai and Cloudflare predicted more attacks following the record-setting efforts. Cloudflare CEO Matthew Prince said he was seeing separate attacks of a similar size last week.
Corero, a denial of service protection service, published countermeasures on Wednesday:
“Looking at shodan.io indicates there are many more than just 17,000 Memcached servers that can be used for DDoS attacks,” said Ashley Stephenson, CEO of Corero. “If the vulnerable servers on the list are utilized for attacks they can be neutralized with the kill switch by sending just 17,000 packets, one to each attacking server, neutralizing their DDoS potential until they are reloaded by the attacker which take 10,000 times longer. Corero has announced today that the ‘flush-all’ command can be used as a benign active defense ‘kill switch’ by those being attacked to suppress attacks from the compromised Memcached server.”
The vulnerability has existed for a decade and more and more server administrators are taking steps to secure their machines. Cloud service providers are also taking action by rate-limiting the UDP ports that launch the attacks.