Meet DarkSide, the ransomware gang blamed for the Colonial Pipeline attack
The cybercriminal syndicate accused of causing one of the largest U.S. pipeline operators to shut down is known for running an enterprise that vets criminal customers and avoids targeting Russian-speaking organizations, according to analysts who have tracked the group.
Since emerging on underground criminal forums in August, the so-called DarkSide malicious software has allegedly been used in dozens of intrusions in the health care, energy and finance sectors. (Ransomware gangs and the software they use often have the same name, but multiple criminal entities sometimes buy access to the same malicious code.) The creators of DarkSide have boasted that their mechanism for encrypting data is the fastest of any, and analysts say the ransomware can encrypt Windows and Linux systems alike.
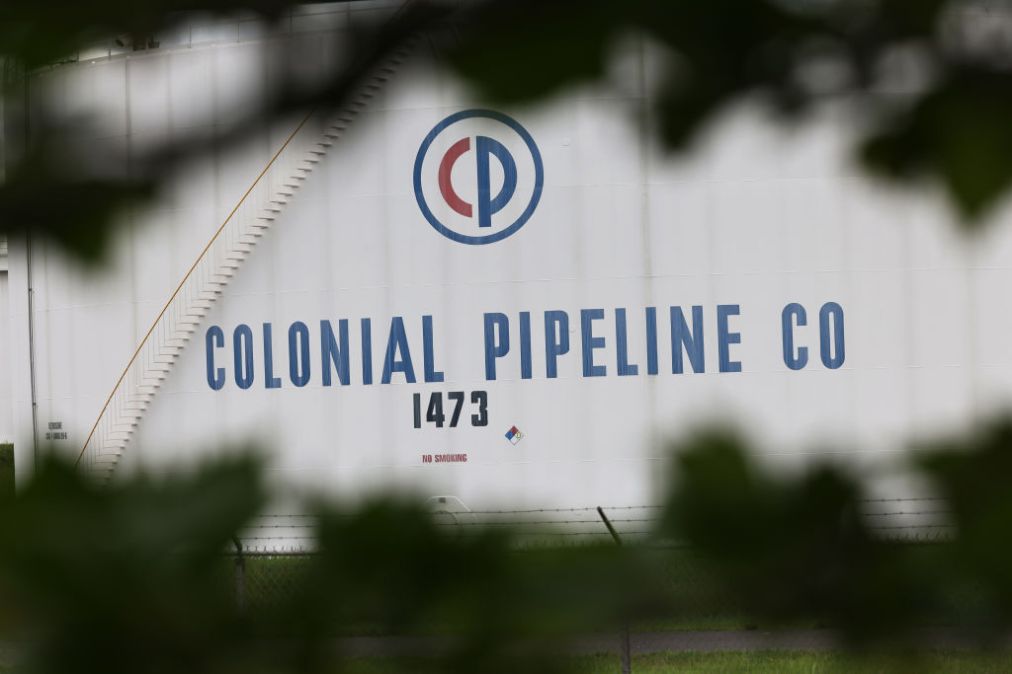
Now, the ransomware developers have gained international attention after hackers last week allegedly deployed DarkSide to encrypt the servers of Colonial Pipeline, a Georgia-based company that transports some 45% of the fuel consumed on the East Coast.
Days later, Colonial Pipeline said it is working to “substantially” restore service by the end of this week, President Joe Biden has condemned the ransomware attack, and the Environmental Protection Agency on Tuesday issued “an emergency fuel waiver to help alleviate fuel shortages” in certain states affected by the pipeline shutdown. Meanwhile, national security officials are focused on the perpetrators.
The DarkSide ransomware employ a strategy that is increasingly popular with well-organized cybercrime groups: They sell access to their hacking tools to other criminals and then split the proceeds from ransom payments.
While that approach can make it more difficult to identify perpetrators of hacks, it also runs the risks that someone purchasing access to the ransomware will use the tool against critical infrastructure, and thus attract attention from law enforcement.
The FBI has said the DarkSide malicious code was used in the disruption of Colonial Pipeline’s IT systems, but it is unclear which specific criminal entity conducted the hack.
“Our goal is to make money, and not creating problems for society,” the ransomware syndicate posted in a message on their website after the Colonial Pipeline incident. The statement claimed that the group would start checking “each company that our partners want to encrypt to avoid social consequences in the future.”
Apparently the group’s previous vetting of criminal customers was insufficient.
Whether the DarkSide affiliates modify their behavior or not, their well-organized approach to digital extortion is not going away. Maze, another Russian-speaking cybercrime group that targeted companies in a dozen sectors, also employed the “ransomware-as-a-service” model.
Dmitry Smilyanets, an analyst at threat intelligence firm Recorded Future, said that the number of active “affiliates” or criminal entities buying DarkSide hacking tools fluctuates regularly, but is currently roughly between five and 10.
“The DarkSide only employs Russian-speaking affiliates and initial access suppliers after a serious interview,” Smilyanets said. The group’s code-writers have extensive experience and its operatives include “top tier eastern European cybercriminals,” he added. Smilyanets, who is fluent in Russian, monitors underground forums where gangs like DarkSide are active.
DarkSide affiliates are also known for targeting an organization’s domain controllers, which are the central hubs that handle data across a network, according to security firm Cybereason. By commandeering a domain controller, the hackers can zero-in on data that they first exfiltrate from the victim and then encrypt. Because of the importance of domain controllers to the functionality of a network, security experts advise targets of ransomware to isolate at least one domain controller to limit the spread of the malware infection.
The US options for dealing with DarkSide
As Colonial Pipeline gradually restores its operations, public attention is also shifting to try to understand who perpetrated the hack.
“So far there is no evidence … from our intelligence people that Russia is involved, although there is evidence that the actors’ ransomware is in Russia,” Biden said on Monday. “They have a responsibility to deal with this.”
Within three days of the incident becoming public, the FBI said that the DarkSide ransomware was used in the hack of Colonial Pipeline’s IT systems. Howard Marshall, the former deputy assistant director of the FBI’s Cyber Division, said that turnaround was unusually swift, and could reflect the urgency of the situation and the maturation of the bureau’s cyber capabilities.
“Is it a broader signal from [the U.S. government] that they’re going to be more aggressive, that we’re not going to play this cloak-and-dagger game of not showing our hand?” said Marshall, who is now managing director and global lead of the cyberthreat intelligence program at Accenture Security.
The FBI last year announced a cybersecurity strategy that aims to impose harsher consequences on cybercriminals that threaten U.S. infrastructure. The bureau has on multiple occasions also targeted hackers’ infrastructure, knocking prolific scammers offline, including an operation earlier this year against the Emotet botnet. That trend will likely continue, White House deputy national security adviser Anne Neuberger said Monday.
Short of putting the perpetrators in handcuffs, though, it has proven difficult to permanently disable malicious infrastructure. For example, TrickBot, a vast botnet used for ransomware attacks and fraud, has lived on months after U.S. Cyber Command and private companies like Microsoft disabled some of the botnet’s infrastructure.
“I’ve always equated it to the drug game: You can knock off corner drug dealers all day long [but] there’s going to be a new one there the next day,” Marshall said.