Dark net markets moving to adopt bug bounty programs
From the Pentagon to some of the biggest companies in the world, bug bounty programs are de rigueur: Big companies pay big money hackers to tell them how to fix their cybersecurity problems rather than have the hackers use it against them.
The dark net is no different. Hansa Marketplace, a large anonymous black market which brought in an estimated $3 million in business in the last year, launched a bug bounty program this week with rewards ranging upwards of $10,000 (10 bitcoins) for people who find critical vulnerabilities.
Like other major dark net markets, Hansa sells a variety of products including hacked account credentials and illicit drugs. There are approximately 15,000 unique product listings on the site.
The program was launched in the wake of a high-profile bugs found on AlphaBay Market, the dark net’s biggest black market, as well as Hansa itself. One hacker told CyberScoop she found two bugs on Hansa: A Captcha bypass that allows for spamming and phishing users and an exposed database that did not contain sensitive information. Hansa offered 1 bitcoin (worth a little over $1,000 right now) as a reward, though it was turned down by the researcher.
Bug bounties have skyrocketed in popularity over the last seven years with the hope that hackers would be heavily incentivized to responsibly disclose technological flaws rather than use them for illicit purposes. Bug bounties are now a multimillion dollar industry, with full time “bounty hunters” as well as major firms, like Bugcrowd and HackerOne, dedicated entirely to running bounty programs.
Hansa’s program formally launched on January 30 and has seen numerous non-critical and simple bugs already reported, according to Hansa administrators and independent bounty hunters.
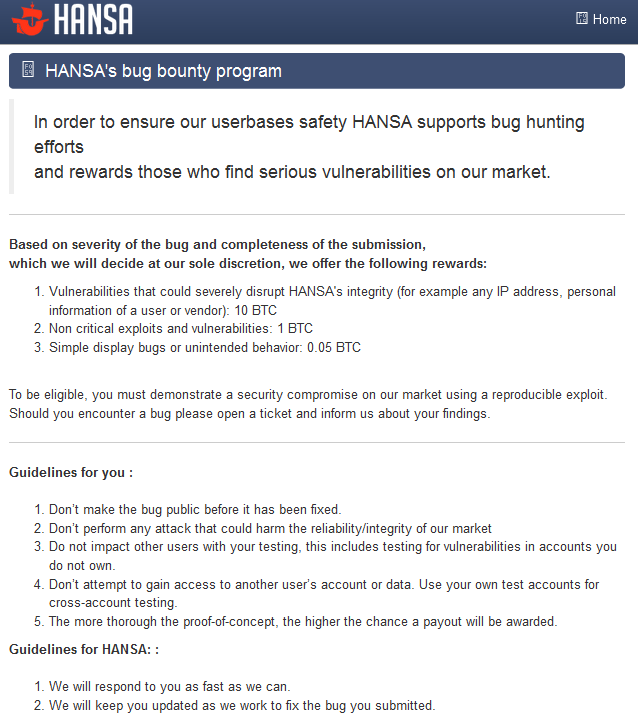
Guidelines for Hansa’s bug bounty program. (HANSA)
The rise of bug bounty programs on the dark net comes after years of criticism for sloppy security in an arena where shoddy work can result in a prison sentence. Ross Ulbricht, the founder of the dark net black market Silk Road, is currently appealing a double life sentence.
OnionScan, software launched in April that scans Tor hidden services for security issues, has put the exclamation mark on the security woes that plague the dark net’s persistent black markets. According to Sarah Jamie Lewis, the anonymity and privacy researcher behind OnionScan, told CyberScoop things haven’t improved much in the last year.
“If anything, the landscape looks worse because of issues found by OnionScan,” Lewis said. “It seems like new hidden services with security issues appear faster than the older ones fix them. Apart from a few isolated cases, I’ve not seen any major changes in vulnerable hidden services fixing problems.”
Formerly a computer scientist for the U.K. Government and a security engineer at Amazon, Lewis sees bug bounty programs ultimately accomplishing little for dark net markets.
“The problems pervading onions [the nickname for websites accessed on the Tor network] are caused by bad assumptions at the software design level — the reliance on web technologies designed for an Internet without consideration for privacy. Bug bounties are only a patch, what we really need are new privacy-oriented software stacks, servers, blog platforms, etc.”
After being told about the bugs on their site, AlphaBay administrators paid a bounty hunter for finding and sharing the vulnerabilities. Yet AlphaBay doesn’t have a formal bug bounty program, share how much they pay for bugs, or actively solicit new information.
Hansa’s program is the first publicized long-term bug bounty program by a major dark net market — and it could conceivably be copied elsewhere. It’s not the first instance of the idea being used on the dark net: Aside from Hansa’s program and AlphaBay’s individualized payments, extinct markets like TheRealDeal and Catina also offered the occasional substantial reward for bug disclosure.
However, bug bounty programs for dark net markets can only go so far. Many users fail to take personal security measures. Last month’s leak of over 218,000 private messages from AlphaBay show that many users still send private data, like real names and addresses, unencrypted. Additionally, the lukewarm use of PGP encryption has been a persistent issue for half a decade since infamous dark net market Silk Road launched in January 2011. The reasons dark net denizens often skip PGP are the same reasons for most security-minded users: It’s cumbersome, annoying and easy to mess up.
No bug bounty program will fix that.






