U.S. charges eight in complex ad-fraud scheme

U.S. prosecutors in the Eastern District of New York filed a 13-count cybercrime indictment Tuesday against the suspected orchestrators of a scheme to defraud internet advertisers out of tens of millions of dollars.
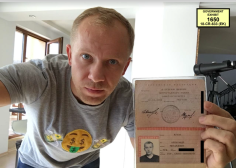
The indictment accuses the eight defendants, who hail from Russia, Ukraine and Kazakhstan, with criminal violations including wire fraud, computer intrusion, aggravated identity theft and money laundering. The list includes Aleksander Zhukov, one of the Department of Justice’s recent high-profile cybercrime arrests.
The group between September 2014 and December 2016 ran a purported advertising network, known as Methbot, that used 1,900 computer servers to load ads on more than 5,000 fabricated websites, prosecutors said. Defendants also leased some 650,000 IP addresses to falsify billions of visits to those fake websites, charging real companies for ads that real humans never viewed, the indictment alleges.
“As alleged in court filings, the defendants in this case used sophisticated computer programming and infrastructure around the world to exploit the digital advertising industry through fraud,” Richard P. Donoghue, U.S. attorney for the Eastern District, said in a statement. “This case sends a powerful message that this Office, together with our law enforcement partners, will use all our available resources to target and dismantle these costly schemes and bring their perpetrators to justice, wherever they are.”
Aleksandr Zhukov, a 38-year-old Russian citizen, served as the CEO of the group, which is described as a private company with offices in Russia and Bulgaria. Zhukov and four others, known as the “Methbot” defendants, developed business arrangements with other ad networks which paid the Methbot team to place ads on real publishers’ websites, prosecutors said.
They allegedly used this method to reap roughly $7 million for legitimate advertisers. The Methbot team then reinvested some of that money to continue their fraud operation while redirecting some funds to other companies. Zhukov is accused of directing $5.4 million from one account into a corporate account located in New Zealand. His arrest was first reported by CyberScoop on Nov. 15.
Three defendants also used a global botnet to carry out another ad fraud scheme known as “3ve.2.” The botnet commanded 1.7 million infected computers belonging to users in the U.S. and elsewhere to load more ads on fabricated web pages. Ad Network #2 between December 2015 and October 2018 caused businesses to pay more than $29 million for ads never viewed by actual humans, the indictment states.
In addition to the charges, U.S. officials seized 31 internet domains and 89 computer servers that were all used in the schemes.
Three defendants — Sergey Ovsyannikov, Yevgeniy Timchenko, and Zhukov — have been arrested and are awaiting extradition. The other five — Mikhail Andreev, Denis Avdeev, Aleksandr Isaev, Dmitry Novikov, and Boris Timokhin, remain at large.
You can read the full indictment below.
[documentcloud url=”http://www.documentcloud.org/documents/5302121-Zhukov-indictment.html” responsive=true]
Greg Otto contributed to this report.