Criminals sell counterfeit certificates to make malware look legitimate

Enterprising cybercriminals are selling counterfeit digital certificates that allow hackers to disguise their malware as legitimate software, according to a new report from the cybersecurity firm Recorded Future.
The fraudulent files, which act like valid code signing certificates, render malware invisible to a large number of anti-virus engines.
“It’s not a cheap commodity,” said Andrei Barysevich, Recorded Future’s director of advanced collection. “But once you sign a payload with the certificate, then the file becomes pretty much undetectable by any antivirus out there.”
Barysevich’s team found a small group of independent vendors in the Eastern European cybercrime markets selling counterfeit code signing certificates to Russian-speaking customers.
The fake certificates are not stolen from legitimate owners but are instead created using real information that can deliver a unique, working and effectively real certificate to hackers willing to pay.
A 2017 paper from the University of Maryland highlighted the issue and showed that digitally signed malware effectively bypasses most security measures. The group showcased compromised code-signing certificates from companies including Thawte, Comodo and Verisign.
“If adversaries can compromise code signing certificates, this has severe implications for end-host security,” the researchers wrote. “Signed malware can bypass system protection mechanisms that install or launch only programs with valid signatures, and it can evade anti-virus programs, which often neglect to scan signed binaries.”
Legitimate certificates are issued by companies like Comodo and Symantec, which recently sold its certificate business to DigiCert after a lengthy losing battle with Google over security issues. In order to get a certificate, you have to supply a mountain of business information to verify your identity. The cybercriminals obtain sensitive corporate information from real companies in order to get effectively real certificates, according to Barysevich.
The scheme is effective. Recorded Future showed how a remote access trojan (RAT) payload became almost entirely undetected after encryption and code signing. Only Endgame’s endpoint security tool was entirely sure of what it was seeing. Here’s the VirusTotal results from an encrypted and code-signed payload:
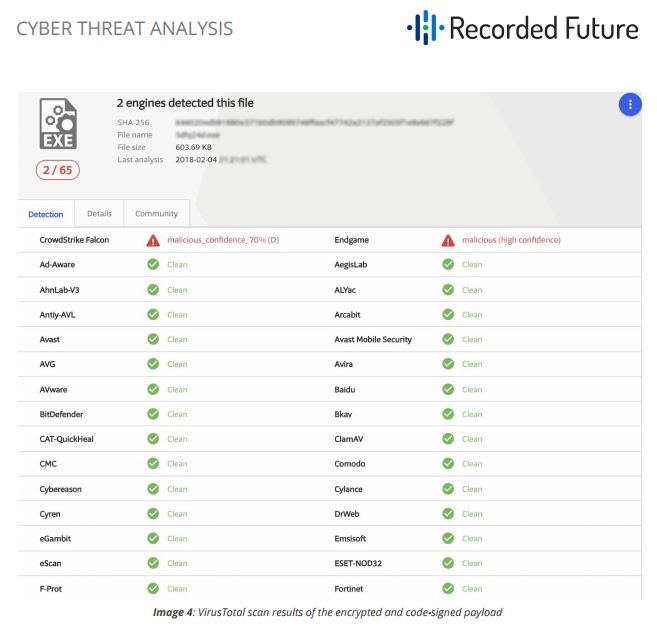
(Recorded Future)
One interesting data point from the research shows all the vendors of the counterfeit certificates explicitly acknowledge that Google Chrome’s security is far more effective and powerful than its peers and that the criminal customers have to expect less success hacking any targets using Chrome. Google didn’t respond to a request for comment.
“Chrome has their own methodologies about how to differentiate a legitimate website from a fake one,” Barysevich said. “Even if a company is using an SSL certificate to obfuscate the maliciousness of the domain, Google Chrome is still capable of highlighting the domain as fake or at least risky. The exact methodologies, we have no idea.”
Fraudulent digital certificates were used in attacks like Stuxnet and Duqu 2.0, two successful hacking campaigns linked respectively to the United States and Israel beginning over a decade ago. But the technique is climbing down from those lofty perches of high-level nation-state campaigns to prices affordable to a wider range of cybercriminals.
“We know it’s been used in the wild,” Barysevich said. “No one is buying for fun. If someone pays upwards of thousands of dollars, I can guarantee you it’s being used to infect victims.”
The counterfeit certificates range widely in price but all of them tend to be relatively expensive compared to other illicit goods on underground markets. For that reason, they’re much more likely to be used by well-funded groups. The cheapest code signing certificate costs $299 while an Extended Validation (EV) certificate with SmartScreen reputation rating sells for $1599.
“Obviously if a nation-state actor or a well-funded cybercriminal group is trying direct operations to infect one company, organization or person, then the use of the certificates is very justified,” Barysevich said. “When someone attacks a specific company, they have a very clear agenda. They have enough funds to research the company. To spend an extra $500 on a certificate to make sure the final payload will be delivered and the victim will be infected is in line with their modus operandi. The cost is irrelevant to attackers like that.”



