State Department offers $10 million for details on Conti ransomware gang members
The State Department on Thursday announced a $10 million reward for information related to five specific individuals associated with the Conti ransomware group.
The Russian-based cybercriminal group has wreaked havoc around the world. As of January 2022, there were more than 1,000 victims of attacks associated with Conti ransomware and payouts exceeding $150 million, according to the FBI.
The agency is seeking information on Conti associates known as “Tramp,” “Dandis,” “Professor,” “Reshaev” and “Target,” the agency said Thursday and first reported by Wired. A previous reward offer, announced May 6, promised $10 million for information leading to the identification and/or location of people who held “a key leadership position” within Conti. An additional $5 million reward was available to anybody who could provide information leading to the arrest and or conviction of anybody in any country conspiring to take part in a Conti variant ransomware attack.
“If you have information that ties hacking groups such as Conti, TrickBot, Wizard Spider; the hackers known as “Tramp,” “Dandis,” “Professor,” “Reshaev,” or “Target”; or any malware or ransomware to a foreign government targeting U.S. critical infrastructure, you may be eligible for a reward,” the announcement reads.

It’s unclear where the information about these particular individuals came from a tip or from somewhere else.
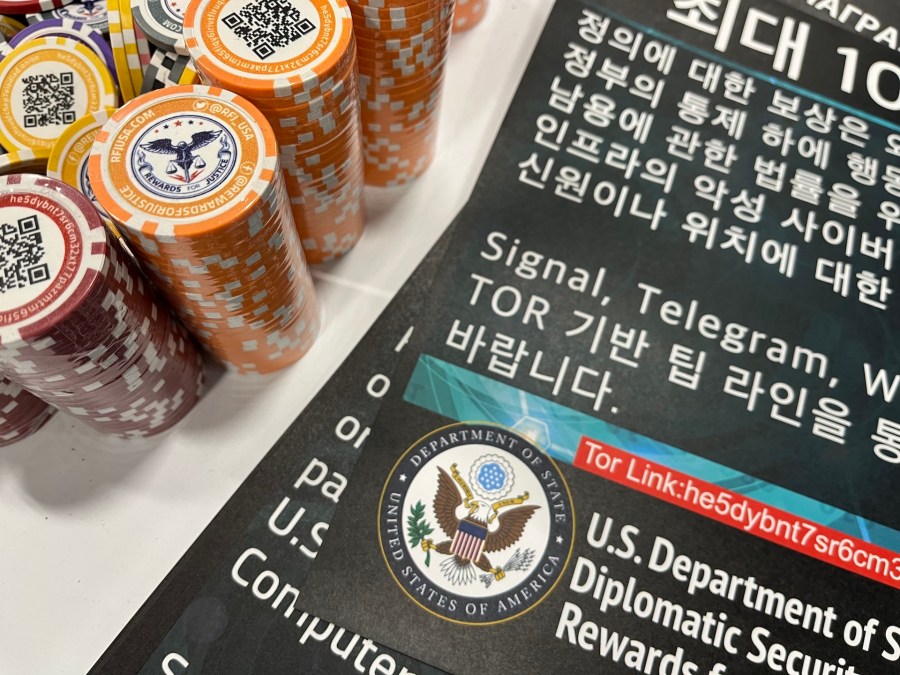
Agency officials made the announcement at Black Hat, the annual cybersecurity conference in Las Vegas that brings together cybersecurity experts and policy makers from around the world. The State Department had a booth at the event advertising the rewards — with T-shirts, posters, casino chips with QR codes — which are administered through its Rewards for Justice program.
The Rewards for Justice program is one of four within the State Department that pays rewards for information, with the others related to war crimes, narco terrorism and transnational organized crime, a State Department official told CyberScoop. In its nearly 40 year-existence, the program has paid roughly $250 million, primarily related to counter terrorism.
The critical infrastructure reward offer was announced last year.
U.S. Air Force Maj. Katrina Cheesman, the spokesperson for the Cyber National Mission Force, said in a statement that “Conti has publicly acknowledged its connection with foreign governments, specifically its support of the Russian government. Based on its ties to Conti and other indicators, it is assessed the leadership of the organized crime group known as Wizard Spider likely have a connection to government entities inside of Russia. While we don’t speak to specific intelligence, planning, or operations, we can say these actors continue to look for cyber vulnerabilities to conduct cyber activity that undermines U.S., allied, and partner interests. U.S. Cyber Command works closely with its interagency partners to address threats to national security and critical infrastructure in foreign cyberspace.”
On Feb. 25, the day after Russia invaded Ukraine, a message appeared on Conti’s website pledging support for Russia and warning that it would attack “the critical infrastructures” of any country that took action against Russia. The group quickly softened the message, but a Ukrainian researcher with access to Conti’s servers released a trove of messages exposing the inner workings of the group.
Some thought the situation hobbled the group, but it remains up and running. In late April the group launched a series of attacks on the government of Costa Rica, demanding $20 million and calling for protests in the streets as the government refused to pay. In July, researchers with IBM’s Security X-Force published research showing TrickBot, an associated cybercrime operation, had been “systematically attacking Ukraine.”
But the chats did offer a window into the day-to-day operations of the group, showing it to be a highly organized, if somewhat inefficient, and structured operation. “Target,” for instance, was seen chatting to “Stern,” one of the main
leaders, about various teams’ monthly salaries, according to an analysis from cybersecurity firm Trellix, implying some kind of management role.
Similar excerpts show “Professor” and “Reshaev” as active members as well.
Allan Liska, a threat intelligence analyst with Recorded Future, praised the State Department’s efforts.
“For too long the government treated cybercriminals differently than nation-state actors and responded differently,” he told CyberScoop. “But the truth is we have seen ransomware attacks that do as much, if not more, damage than many state sponsored attacks.”
Even though the suspects are not likely to ever see the inside of a U.S. courtroom, he added, the effort is worth it.
“We are not likely to see arrests of these actors, unless they are dumb enough to leave Russia,” Liska said. “But getting their names and faces out there can make them, rightfully, paranoid. It also could lead to collecting more intelligence on them and their operations.”




