Colonial Pipeline CEO says company didn’t have plan for potential ransomware attack
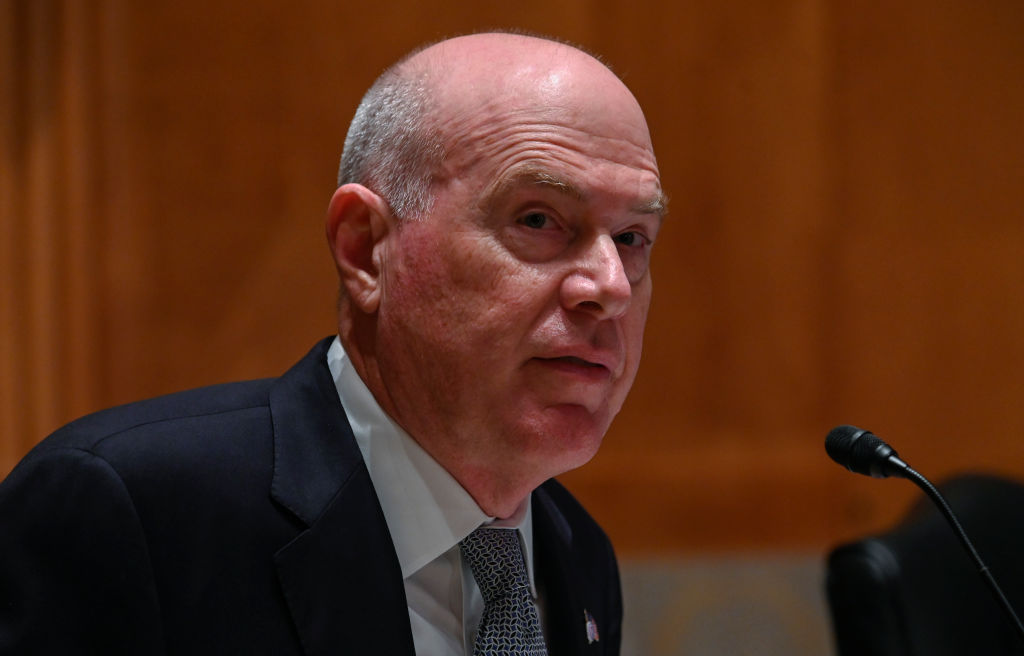
Colonial Pipeline did not have guidance in place on how to handle a ransom demand from cybercriminals who locked up its systems, its CEO testified in a hearing before the Senate Homeland Security and Governmental Affairs Committee Tuesday.
The company’s failure to prepare explicitly for a ransomware attack — despite warnings from Homeland Security Department’s Cybersecurity and Infrastructure Security Agency as early as February 2020 about the risk of such attacks against the pipeline industry — underscores growing concerns from lawmakers that the critical sector needs tighter regulations when it comes to cybersecurity.
“We have an emergency response process: See the threat, contain the threat, remediate the threat, and restore,” Colonial Pipeline CEO Joseph Blount said in response to a question from Sen. Maggie Hassan, D-N.H. about ransomware-specific guidance. “So in this case, you use the same process, but you use a different set of experts.”
Hassan chastized Blount’s response, though she noted Colonial Pipeline wasn’t alone in its failures to prepare for the rapidly growing ransomware crisis.
“I don’t think it’s acceptable to understand the critical nature … of your product, but then not really have the preparation and the system in place to protect it as if it’s critical infrastructure,” Hassan replied. “We need to start imagining what can happen, and respond accordingly as opposed to always be looking at what the last problem was and really investing in critical infrastructure. I think it’s absolutely important that we have standards that really make sure that companies are investing in the kind of infrastructure they need.”
Blount largely defended the company’s efforts to secure its fuel pipeline, which it took offline last month after cybercriminals seized its computer systems and demanded a ransom to decrypt them. The company ended up paying the attackers $4.4 million worth of cryptocurrency in exchange for keys to decrypt the files. The days-long effort for the company to restore service led to a panic at the pump.
On Monday the Justice Department announced that it had retrieved $2.3 million in cryptocurrency payments the company paid to the attackers.
Blount justified the company’s decision to make the payment and initially keep it confidential.
“I kept the information closely held because we were concerned about operational safety and security, and we wanted to stay focused on getting the pipeline back up and running,” he said. “I believe with all my heart it was the right choice to make.”
Blount expressed support for any additional regulations that helped improve the security of critical industries.
“Anything that can help industry have better security practices standards to follow would be extremely helpful,” he said. He said the company’s actions were already in line with new security requirements from the TSA that will require mandatory reporting of hacking incidents to CISA within 12 hours of detection.
Lawmakers also grilled the CEO about why it failed to immediately notify CISA. Acting CISA Director Brandon Wales told lawmakers last month that he believed that Colonial would not have reached out to CISA if the FBI had not notified the agency.
Blount said the company has an ongoing relationship with the agency and only failed to contact CISA directly because the FBI told them they would loop them in into a conversation later in the day: “If the FBI had not called them, we would have.”
Multiple senators also grilled the company about not securing a legacy VPN system that hackers used as an entryway. The system did not have two-factor authentication turned on.
Blount called the fact that testing didn’t detect the compromise “unfortunate” but said that the company regularly conducts outside audits. He said he was unaware the company did not follow through on a voluntary Transportation Security Administration audit until it was publicly reported. He doubted that the audit would have caught the unsecured system.
“I think in this case, it probably would not have resulted in finding that legacy VPN,” he told lawmakers. “They don’t actually go into the system. It’s a questionnaire-format type thing.”






