Biden issues memo to push critical infrastructure cybersecurity upgrades
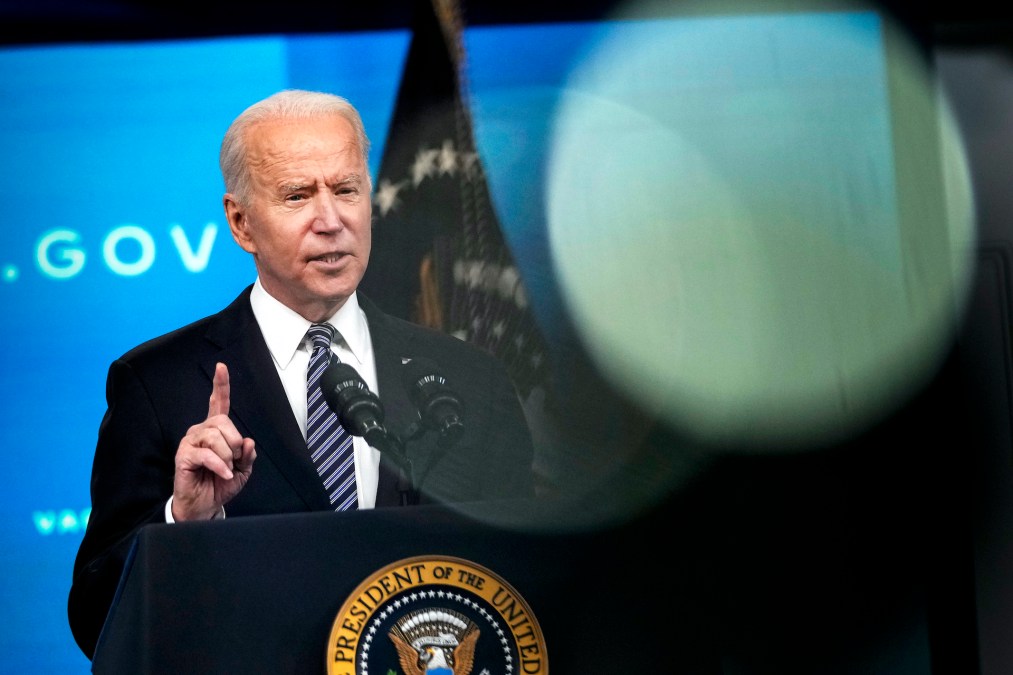
President Joe Biden on Wednesday signed a national security memorandum tasking a group of federal agencies to develop cybersecurity performance goals for critical infrastructure.
The directive is the latest effort from the Biden administration to get critical industries on board with improving cybersecurity in areas that could impact national security and the economy. The executive memo follows a security directive handed down by the Transportation Security Administration last week requiring owners and operators of TSA-designated critical pipelines to implement mitigations to protect against ransomware and other threats.
“Our current posture is woefully insufficient given the evolving threat we face today,” a senior administration official told reporters in a call on Tuesday. “We really kicked the can down the road for a long time. The administration is committed to leveraging every authority we have, though limited, and we’re also open to new approaches, both voluntary and mandatory.”
The Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency and the Commerce Department’s National Institute of Standards and Technology will take the lead on the initiative. The official did not elaborate on what benchmarks CISA and NIST might include in the performance goals, but offered that the initiative furthers the administration’s goal of modernizing U.S. cyber defenses.
“These performance goals should serve as clear guidance to owners and operators about cybersecurity practices and postures that the American people can trust and should expect for such essential services,” the memo outlines.
The memo sets a deadline of September 22 for DHS to issue preliminary goals across critical infrastructure sectors. Final cross-sector and individual industry goals will be issued within a year of the memo’s release.
The memorandum also formally establishes President Biden’s industrial control system cybersecurity initiative, a pilot launched in April with the electricity sector. The official said that as a result of the pilot, more than 150 electric utilities representing almost 90 million customers are either deploying or agreeing to deploy control system cybersecurity technologies. The natural gas and pipeline sector is the next focus of the initiative.
“The point we want to make is the federal government cannot do this alone,” the official told reporters. “These may be voluntary, but we hope and expect that all responsible critical infrastructure owners and operators will apply them.”
A series of high-profile cyberattacks in recent months have placed the gaps in the security of America’s critical industries under the spotlight. Among them, a ransomware attack right before Memorial Day weekend forced major fuel-provider Colonial Pipeline to go offline and led to a panic-fueled gas shortage in the United States.
Currently, the administration is working within the power of existing authorities, which cover very little when it comes to businesses in critical industries, according to the administration official. The vast majority of America’s critical infrastructure is owned by the private sector. Security standards for critical industries are largely piecemeal, set by sector or state and local guidelines.
To move from voluntary standards to mandatory requirements would likely requiring partnering with the Hill, the senior official acknowledged.
“Short of legislation, there isn’t a comprehensive way to require the deployment of security technologies and practices that address really the threat environment that we face,” the official said.
Members of Congress have already introduced flurry of bills addressing security gaps in critical infrastructure, including legislation from Sen. Mark Warner, D-Va., that would require critical industries to report breaches to the federal government.
The administration is also exploring performance incentives to accelerate voluntary adoption, such as grants, tax credits and cyber insurance, the official said.
Updated 7/28: Updated to include additional information from the memorandum.






