Meet Berla, the little-known company that can pull smartphone data from your car

Late morning on Jan. 7, 2015, a black Citroën C3 arrived in front of Charlie Hebdo’s headquarters at 10 Rue Nicolas-Appert in Paris. Two men stepped out dressed in black, toting Kalashnikov assault rifles and a long list of people to kill. That was the beginning of a historic terrorist massacre and subsequent battle with police that left 12 dead and left much of the world wondering how it happened.
Police immediately turned to the digital evidence trail, including the Citroën C3. A French supermini, the C3 is advertised as a “smart car,” meaning it creates mountains of data waiting to be analyzed by anyone who can figure out how to gain access.
In order to obtain that evidence, French authorities turned to Berla Corporation, a little-known Maryland-based cybersecurity company that works with and receives funding from the Department of Homeland Security’s Science and Technology Cybersecurity Division.
Berla’s flagship product is Project iVe, a forensics tool that breaks into a vehicle’s data systems to find, organize and analyze a vast range of information that often includes far more than what the car generates itself. As might be expected from a company that works quietly with law enforcement, Berla did not respond to CyberScoop’s requests for interviews, and there is limited public record of discussion about the product, which launched in 2013.
At the time of the Charlie Hebdo attacks, Berla focused almost exclusively on North American vehicles. Nevertheless, the researchers went to work on the Citroën C3 — three such cars were used by the attackers — and company officials have said they helped French authorities gain access and intelligence from the vehicles.
Exactly what was learned from the cars is not public.
This much is certain: Phones plugged into cars often carelessly give away data including SMS messages, contact lists, emails, social media feeds and more. Cars themselves track everything big and small, including GPS location and data on doors opening and closing. The latter can be a surprisingly useful piece of information for investigators.
The process was mirrored less than a year later by a different company. After the deadly terrorist attack in San Bernardino, California, the FBI reportedly turned to the Israeli forensics firm Cellebrite to break into an attacker’s iPhone and gather data for the subsequent investigation. When Apple’s refusal to build a backdoor sparked a front-page dispute that led to then-candidate Donald Trump’s publicly calling for an anti-Apple boycott, the issue of encryption and government access gained an intense public spotlight like never before.
Less publicized was the fact that Berla also assisted in the San Bernardino case, along with many others since. The company’s CEO, Ben LeMere, has spoken publicly about it.
“We’ve assisted in pretty much every major terrorism investigation in the last year, from the Paris bombing to the Chattanooga, Tennessee, shooting to San Bernardino,” LeMere told the Armed Forces Communications and Electronics Association in 2016.
The forensics business is a rich and growing market as more devices gather piles of data that can be used in unprecedented ways by police, intelligence agencies and hackers.
The market for vehicle forensics is booming. About a decade ago, most cars had less than 10 computers on board. Now the average number is rapidly approaching 100.
In the U.S., cars generate 25 gigabytes of data per hour, a number made even more daunting when added to the fact that each American spends an average of 728 hours per year in a car. All added up, we’re generating nearly 20 terabytes of data per year per person in our cars.
When Berla launched in 2013, iVe could access 80 car models. Now the company says the number is over 6,730 globally, including cars from BMW, Ford, General Motors and Volkswagen, among others.
Growing out of earlier law enforcement efforts to hack into and take data from GPS devices, iVe has grown into a global force guided by DHS and private sector developers who sell to exclusively to governments. As part of Berla’s work with DHS, the iVe Steering Committee meets quarterly with representatives from 17 federal, state and local law enforcement agencies to guide the tech’s next steps.
Smartphone forensics — the business of getting at the data inside cutting-edge mobile devices — is the star of the industry because smartphones have come to contain nearly every piece of data in a person’s life. But vehicle forensics can be a powerful work-around when smartphone manufacturers like Apple fight to keep their devices locked and secure.
Then again, a work-around isn’t always required.
Berla works directly with numerous unnamed automobile manufacturers, LeMere said at a Department of Homeland Security event last year, by providing security consulting in exchange for automatic access for Berla’s government customers. Responding to a question about the possibility of eventual public pressure to encrypt data and lock out law enforcement, LeMere explained why the automobile industry was, for now at least, different.
“One of the byproducts of the work we’ve been doing with [the Department of Homeland Security’s Cyber Security Division] is we’re a tier 1 automotive supplier, which is funny because we’re such a small company,” LeMere said, referring to a designation that car manufacturers give to partner companies.
“We’ve been working directly with the [original equipment manufacturers] themselves to educate them. Hey, ‘this is privacy data,’ ‘this is what you need to secure.’ But we only do that when it’s part of an agreement that they will allow law enforcement in,” LeMere explained. “It’s been kind of nice. It’s been kind of a double-edged sword when we give presentations and everyone is immediately scared to death and doesn’t want to plug anything into their cars ever again. But hopefully you guys aren’t going to murder anybody, so it’ll work out.”
None of the companies involved with the 2015 case, including Berla or Citroën, responded to interview requests. The Department of Homeland Security also did not respond to requests for comment.
As the realization dawns on the public that cars are increasingly a collection of computers and high-tech gear on wheels, experts expect to see battles over privacy, security, access and transparency erupt for the same reason we saw fights around smartphones and our other computers: The amount of data at stake is titanic.
“Whenever a mobile device is connected to a vehicle system via USB, Bluetooth, or Wi-Fi, some data from that device is stored in the vehicle,” Berla’s Scott Vaughan explained earlier this year on the firm’s blog. “Potentially, device contacts, call logs, and SMS messages are stored and can thus be acquired in iVe, though the exact data types recorded will vary from one [car] to another.”
A rough outline of the data that can be accessed from cars, as outlined on Berla’s website:
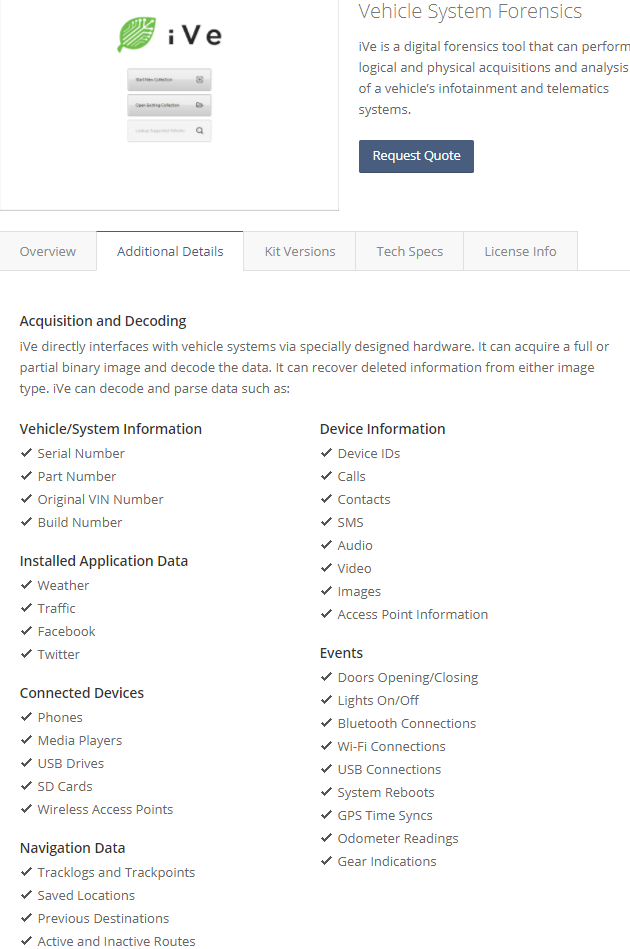
Berla’s iVe

