Russian hacking unit Cozy Bear adds Google Drive to its arsenal, researchers say

The state-backed Russian hacking team behind some of the biggest digital intrusions in recent years has been using both Google Drive and Dropbox to deliver malware against a range of targets, researchers said Tuesday.
Researchers with Palo Alto Networks’ Unit 42 threat intelligence team said Tuesday that the Russian Foreign Intelligence Service (SVR) hacking unit — known as Cloaked Ursa by Unit 42, but more generally as APT29 or Nobelium or Cozy Bear — had previously used legitimate cloud services such as Dropbox as part of malware delivery efforts.
But in a series of spear phishing attacks dating back to early May, the hackers have demonstrated “sophistication and the ability to rapidly integrate popular cloud storage services to avoid detection,” most notably by mixing Google Drive’s cloud storage services into their mix.
“This is a new tactic for this actor and one that proves challenging to detect due to the ubiquitous nature of these services and the fact that they are trusted by millions of customers worldwide,” the researchers said. “When the use of trusted services is combined with encryption, as we see here, it
becomes extremely difficult for organizations to detect malicious activity in connection
with the campaign.”
Dropbox and other cloud and web services such as project management app Trello and Google’s Firebase app development platform aren’t new to the APT29 playbook, as documented in April 2022 by Mandiant and May 2021 by the Microsoft Threat Intelligence Center. But adding Google Drive brings an additional layer of threat.
“Google’s ubiquity, combined with the trust that millions of customers worldwide have in them, make their inclusion into this APT’s malware delivery process exceptionally concerning,” the researchers said. The findings highlight the ongoing potent threat of APT29, which the U.S. government has blamed for the SolarWinds hack, for instance, one of the worst hacks on record.
“Google’s Threat Analysis Group tracks APT 29’s activity closely and regularly exchanges information with other threat intelligence teams, such as Palo Alto Networks, for the good of the ecosystem,” Shane Huntley, senior director of Google’s Threat Analysis Group, told CyberScoop in an emailed statement. “In this case, we were aware of the activity identified in this report, and had already proactively taken steps to protect any potential targets.”
A Dropbox spokesperson told CyberScoop the company “worked with our industry partners and the researchers on this matter, and disabled user accounts immediately. If we detect any user violating our terms of service, we take appropriate action, which may include suspending or disabling user accounts.”
The latest hacking campaigns highlighted by Unit 42 targeted several unnamed “Western diplomatic missions” between May and June 2022 using what appears to be compromised email accounts within foreign embassies of Portugal and Brazil. On May 13, cybersecurity firm Cluster25 reported Cloaked Ursa activity involving Dropbox. Building off that the researchers identified an additional campaign May 24 which consisted of two emails to the same unnamed NATO country’s ministry of foreign affairs just a few hours apart.
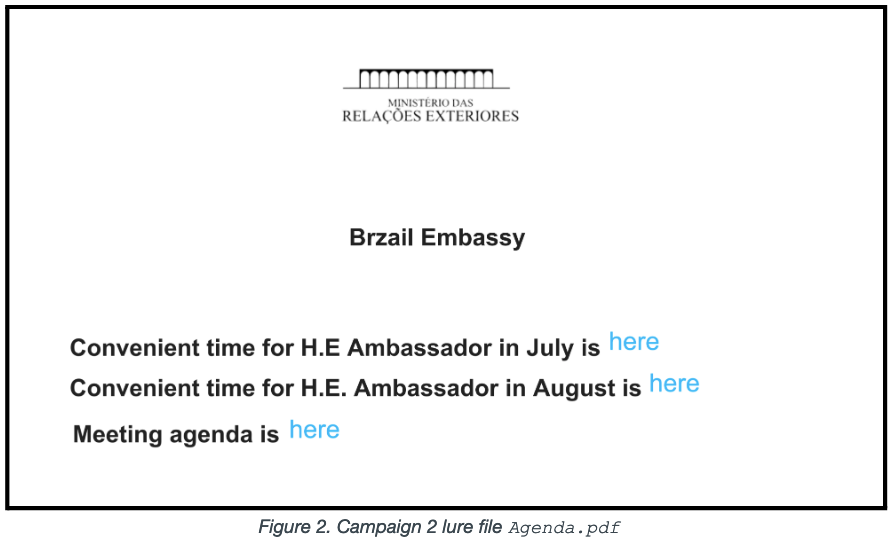
Both contained a malicious document titled “Agenda.pdf,” which linked to an agenda for an upcoming meeting with an ambassador in Portugal. The researchers said they aren’t sure why the emails were sent back to back, but one reason could be that the recipient could not access the file in Dropbox.

“Regardless of the reason, the actors were compelled to rapidly build and send a second spear phishing email the same day with a link to an EnvyScout HTML file with the same name hosted on a legitimate website,” they said. EnvyScout is a malicious dropper used to get additional malware onto the targeted system.
Metadata associated with the file allowed the Unit 42 researchers to find yet another Cloaked Ursa campaign dated to June 30. This campaign a similar lure of discussing a diplomatic visit, this time with a reference to an unnamed foreign embassy in Brazil. Notably, the hackers misspelled Brazil as “Brzail” in the document.
The researchers reiterated that the ubiquity of Google Drive, Dropbox and other popular cloud services, that “are trusted by millions of customers worldwide,” means that “all organizations [should] review their email policies” and the details included in the report to address the threat.






