Here’s how the FBI’s most wanted cybercriminal hacks his targets
The FBI’s most wanted cybercriminal — who was indicted by the Justice Department for helping Russian intelligence break into Yahoo’s digital infrastructure — has repeatedly taken advantage of self-inflicted security mistakes made by private companies in order to compromise targets, according to Chris McNab, co-founder of AlphaSOC.
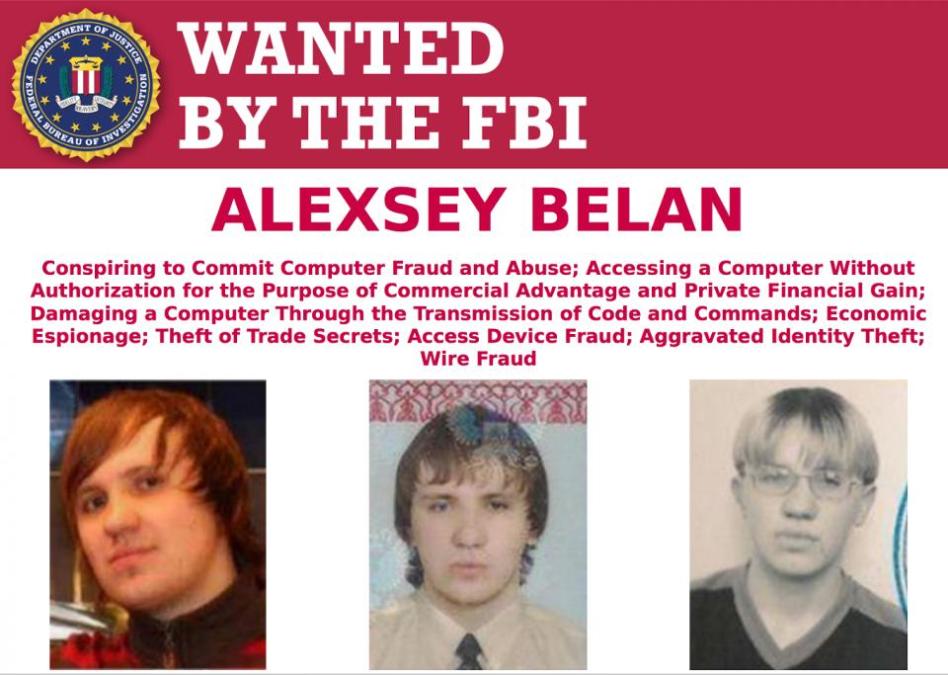
FBI agents told reporters Wednesday that the 2014 Yahoo breach possibly began with 29-year-old Latvian native Alexsey Belan sending a routine phishing email sent to a “semi-privileged” employee. It appears that the attacker was able to progressively gain access to new systems after entering the company’s network via a malicious attachment.
As a former employee of NCC Group, McNab responded to a data breach in 2012 that Belan was also allegedly behind. McNab wrote about Belan’s hacking tactics, techniques and procedures, which he discovered during that investigation in a blog post published Monday.
McNab’s article provides some rare insight into how Belan, also known as “M4G,” attacked specific targets in the past.
Some of Belan’s tactics include his use of known, unpatched WordPress flaws; altering Linux authentication mechanisms to capture credentials; targeting systems responsible for cataloguing IT help desk requests; identifying peripheral web servers through Google and LinkedIn searches; and searching for administrative workflows and VPN details in corporate wikis.
A corporate wiki can be understood as a company’s internal guidebook, helping to answer common questions and share up-to-date information. They are hosted on websites that can be simultaneously edited by multiple, approved users.
“Proper segmentation, enforcement of a sensible policy around the safe transmission of secrets, and close monitoring of production systems nullify this threat,” McNab wrote.
According to the Justice Department, Belan was able to amass a massive library of compromised email addresses and password hashes over the course of his many exploits. This information, McNab explained, would likely be beneficial because password reuse is so common: cracking a Yahoo or Google email account for a single individual may also open the door to other services used by that same person. Password reuse is exacerbated in cases where a service does not employ two-factor authentication.
It’s believed that Belan is responsible for breaching at least three high-profile U.S. tech firms: Yahoo, Evernote, Scribd and Zappos, according to The New York Times.
“Email addresses and password hashes were amassed with each compromise. Cracked credentials were used to target further victims via exposed mail services (e.g. Outlook on the Web or G Suite), and the exploratory process was repeated to gain privileged network access via VPN or similar means,” the blog post reads.
Based on this observation of Belan’s techniques and tactics, McNab recommends that companies make sure to “segregate risky Internet-exposed servers” and to not “leave secrets in [a] Wiki, ticketing, or bug tracking system.” He also advises that sensitive material should not be sent via email and an organization’s two-factor authentication service require more than username, password and software-based certificate.
It’s believed that Belan was recruited by Russian intelligence services to run clandestine cyber operations. Last week’s indictment was the clearest link yet between the Latvian hacker and Russia’s Federal Security Service, or FSB.
Last week was the fourth time the U.S. government has indicted Belan. Law enforcement originally put out an arrest warrant for Belan in 2013, but he managed to escape Europe to Russian-controlled territory shortly after the warrant was posted. The FBI subsequently posted a $100,000 reward for information leading to his arrest, with the Obama administration levying an economic sanction against Belan in Dec. 2016.






