Popular Mac app grabs your browser history and sends it to China

Update: Apple has pulled Adware Doctor from the Mac App Store. Our original story is below.
Apple’s famous walled garden isn’t keeping all the undesirables out.
New research on one of the most profitable apps in the official Mac App Store reveals developers are side-stepping around Apple’s controls to surreptitiously grab a user’s browser history and send it back a company in China. Even though it’s a clear violation of Apple’s data collection and storage rules, the app remains up and running in the store.
Apple has not yet commented on the subject.
Former NSA staffer and notorious Mac hacker Patrick Wardle and security researcher @privacyis1st published research on Friday spotlighting Adware Doctor, a popular anti-adware application that is the fifth-most popular paid app in the Mac App Store. The app, the researchers write, steals browser histories and a handful of other private information that it should not be able to access, including App Store searches and processes running on a machine.
“Our research uncovered blatant violations of user privacy and complete disregard of Apple’s App Store Guidelines,” Wardle wrote. “And surprising, though this was reported to Cupertino through official channels, the app remains in the Mac App Store even today!”
The app’s developers did not respond to a request for comment.
Besides siphoning data and never asking permission, Adware Doctor has a few other skeletons in the closet. The app originally was named “Adware Medic,” a name clearly designed to mimic a different AdwareMedic app. The latter software was acquired by MalwareBytes and rebranded in 2015.
When MalwareBytes complained two years ago, the app was removed and reappeared under the current name. It sits near the top of the Mac Store, thanks to what may be a mountain of fake reviews.
The store itself is supposed to vet and sandbox apps so they can’t access and take data without explicit permission. The app then serves a pop up in which it asks the user to “clean” their system by “restoring your browser.”
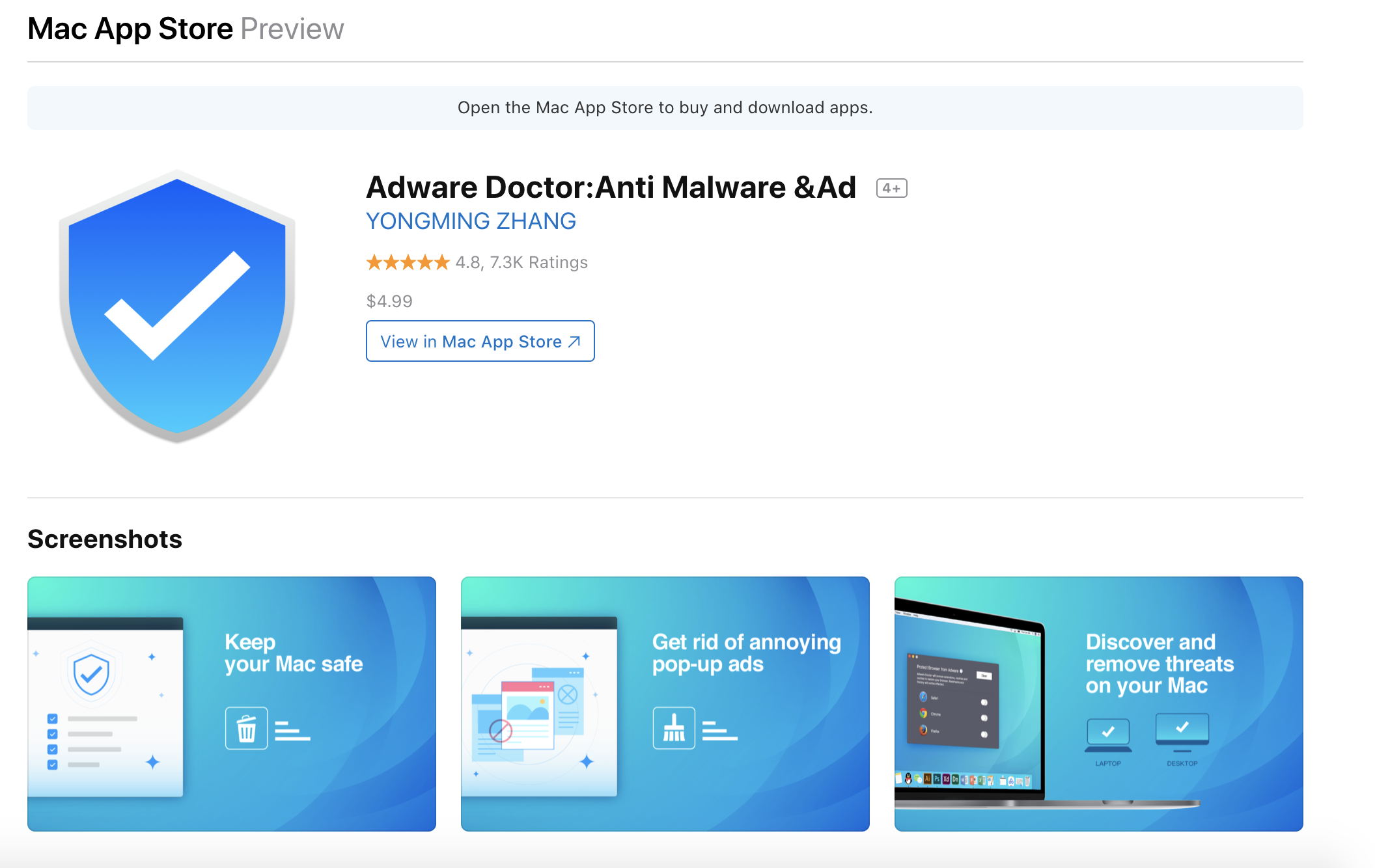
A screenshot from the Mac App Store where Adware Doctor is still being sold.
Watching Adware Doctor closely through tools such as a process monitor and network monitor, researchers noticed the app create a “history.zip” file, then sends the file to yelabapp.com, which is owned by an entity in China. If that’s not enough, the history.zip file has a hardcoded password sent to the Chinese company in plain text.
“When an application runs inside a sandbox it is constrained by what files or user information it can access,” the researchers wrote. “For example, a sandboxed application from the Mac App Store should not be able to access a user’s sensitive browser history. But Adware Doctor clearly found away.”
This process regarding the history.zip file was shut down several days ago after @privacyis1st tweeted publicly about the findings. It’s not clear why the shutdown occurred but the app, which has been online for at least two years, continues to collect and package private data before attempting to exfiltrate it to a currently downed domain at adscan.yelabapp.com.
The process can be continued at any point if Adware Doctor’s owners decide to launch the site once again.






